Photo Gallery
 |

 |
Sqrrl

Additional Info
| Company | Sqrrl |
| Company size | 50 - 99 employees |
| Website | http://www.sqrrl.com |
NOMINATION HIGHLIGHTS
Sqrrl is an industry-leading Threat Hunting Platform that unites proactive hunting workflows, link analysis, user and entity behavior analytics (UEBA), and multi-petabyte scalability capabilities into an integrated solution. Sqrrl reduces attacker dwell time (i.e. the amount of time between when a breach occurs and when it is detected) by isolating adversarial behavior faster and with fewer resources than traditional security solutions. As a proactive investigation tool, it enables analysts to evaluate the scope, impact, and root cause of an incident more efficiently and thoroughly than ever before.
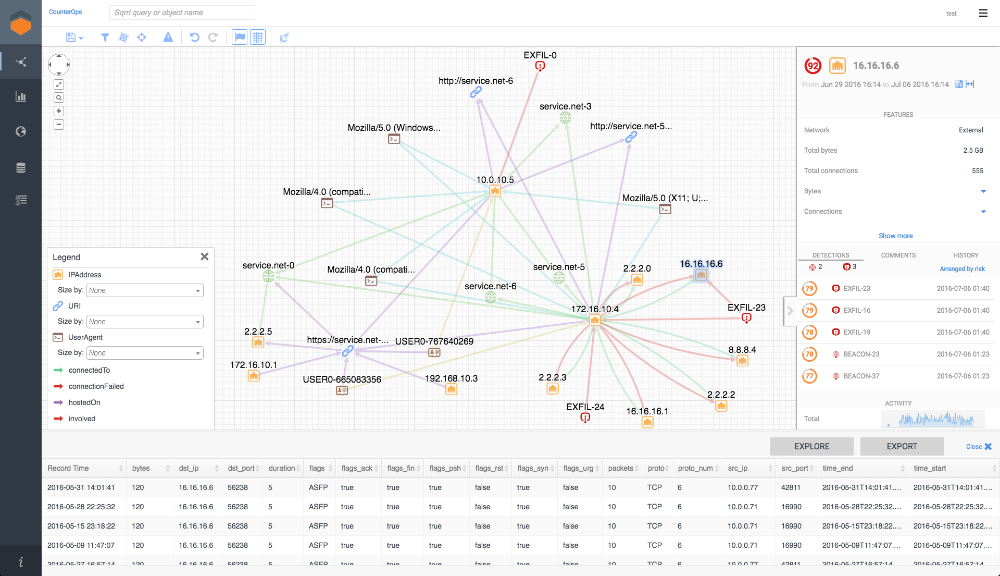
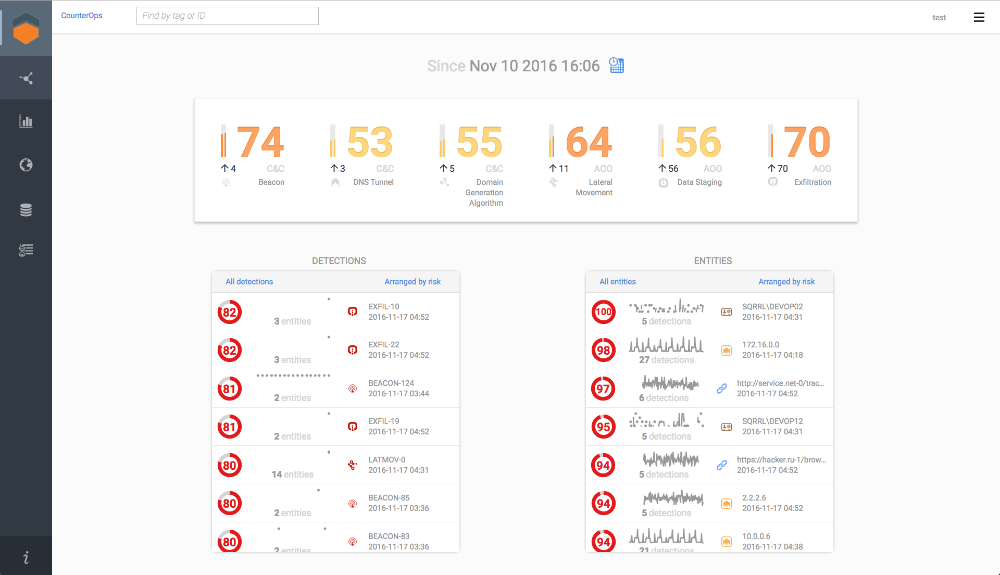
A core feature of Sqrrl Enterprise is an array of adversarial behavior detectors that identify threat actor Tactics, Techniques, and Procedures (TTPs) by utilizing a combination of analytical approaches including machine learning, behavioral baselining, peer group analysis, and graph analytics. The Behavior Graph, an interactive visualization at the heart of Sqrrl investigations, automatically recognizes and analyzes inherent connections or links in data, evaluating their meaning and context and deriving new insights for the end user to interpret. Sqrrl’s organization of data in a linked data model streamlines the question-based, iterative process of threat hunting through its powerful and interactive graph representation of users and entities. The latest Sqrrl release expands these capabilities by introducing custom-built, analyst-defined analytics and risk triggers.
Sqrrl’s visualization tools enable more junior analysts and hunters alike to improve and expand their analysis workflows with relative ease. The platform addresses many of the challenges and obstacles to hunting, such as finding starting points for hunts or recognizing anomalous behaviors. Using Sqrrl’s risk scores, profiles, and reports, analysts can quickly assess user and asset risks, holistically evaluate the conditions of even a large group of entities, and identify new insights to improve their automated solutions.
How we are different
-A pioneer in enterprise threat hunting, Sqrrl is one of the first purpose-built solutions for this important Security Operations Center (SOC) activity. Through thought leadership in whitepapers, trainings, articles, and more, Sqrrl has introduced concepts like the hunting loop and hunting maturity model, seeking not only to build an innovative product but also to take steps to formalize this growing field.
-Sqrrl lowers the barrier of entry for less experienced analysts so that hunting is no longer a practice of only the top 1% of security practitioners. Through capabilities that include predefined search pathways in a linked data model, a comprehensive search language, asset tagging, investigation recording, and multiple domain data fusion, Sqrrl brings aspects of multiple different hunting tools together into one. Everything that an analyst needs to hunt is packaged in a single platform. Sqrrl also includes tools for collaboration within a SOC, such as hunt recording, helping experienced hunters mentor junior analysts.
-Sqrrl unites three critical aspects of SOC activity, including traditional proactive threat hunting, incident investigations, and automated analytics for making hunts repeatable and machine powered. No other threat hunting product on the market has tackled each of these important aspects of the security puzzle, and brought them together into a cohesive platform.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



