Photo Gallery
|
|
 |
Strongarm
Additional Info
| Company | Percipient Networks |
| Company size | 5-10 employees |
| Website | https://strongarm.io/ |
NOMINATION HIGHLIGHTS
Small and medium-sized businesses (SMBs) have become prime targets for cybercriminals because they don’t have the financial and staffing resources necessary to execute a sophisticated security strategy. Strongarm alleviates the budget and security expertise struggles of SMBs by automating and simplifying the process of stopping and cleaning up malware. The solution is 100% cloud-based so it eliminates the need to install hardware, software or agents, thus reducing the burden on IT staff. The natural scalability of the cloud enables a cost structure that is a fraction of traditional appliance-based approaches.
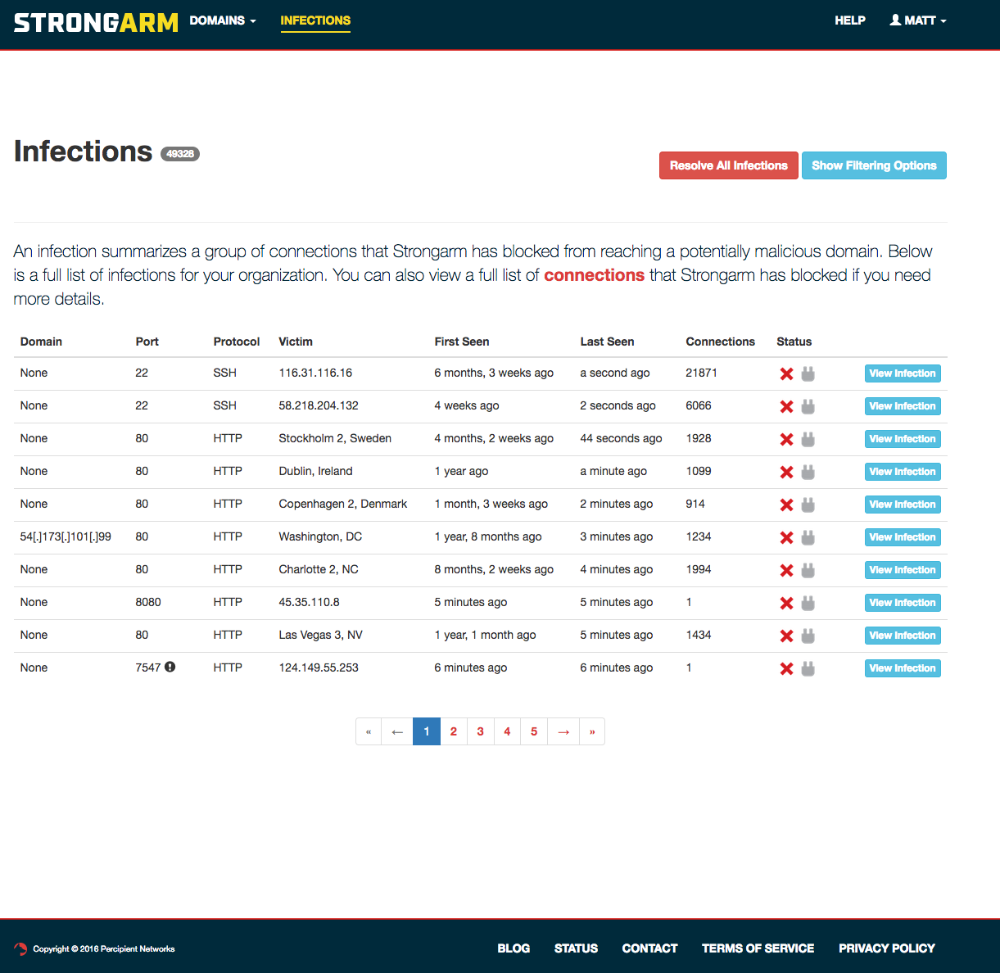
Unlike traditional security solutions that attempt to keep malware out, Strongarm takes a unique inside-out approach to security that assumes malware will get in. The solution monitors outbound DNS requests, noticing when devices try to communicate with malicious command and control sites. If an attempt is made, Strongarm blocks the request, preventing cybercriminals from stealing information or launching most ransomware attacks. Strongarm then goes one step further and “speaks malware” to the device that made the request. By communicating with the malware, Strongarm can automatically alert IT which machine is infected and how to best clean it up.
Strongarm comes with “Always on Protection”. This capability coupled with Strongarm’s agentless approach, enables all devices (computers, tablets, phones, IoT devices) to be protected whether they are connected to a corporate network or to less secure public WiFi Hot Spots. The mobile nature of today’s workers requires people to be secure whether in the office or on the go.
Strongarm was born in a federal research lab. The founding team behind Strongarm’s technology has experience helping protect governments, countries and large enterprises. The team at Strongarm utilizes this knowledge and wakes up every day dedicated to helping regular people and SMBs protect their businesses from the bad guys.
How we are different
•Simple – Strongarm deploys in under 10 minutes, requiring no agents, SW, or HW appliances.
•Automated – Strongarm “speaks” malware, automating the process of blocking malware from doing damage and providing pinpoint details on which machine the malware was targeting. In many cases the malware can be automatically removed.
•Affordable – At just $3 per user/month, Strongarm is affordable for all.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



