Photo Gallery
 |

 |
Syntax Ransomware Response Services


Additional Info
| Company | Syntax |
| Company size | 1,000 - 4,999 employees |
| Website | https://www.syntax.com/ |
NOMINATION HIGHLIGHTS
Ransomware attacks have jumped more than 715% in 2020 with more people working remotely during the global COVID-19 pandemic, increasing cybercriminals’ attack vectors. Syntax has successfully helped its enterprise customers prevent ransomware attacks before they happen and, if they occur, has responded quickly and effectively so their business doesn’t shut down.
Once Syntax is notified of an attack in progress, its ransomware response team quickly helps customers identify security vulnerabilities and determine if an attack really occurred. Syntax has strong relationships with its customers at the executive level, so it’s easy for the customers to quickly call if a ransomware attack occurs. Syntax partners with CrowdStrike, an American cybersecurity company, to provide advanced endpoint protection with expert intelligence and to conduct forensic analysis. Syntax implements and deploys the CrowdStrike Falcon™ solution to determine the current risks and exposure.
Once the incident is contained, the event is transitioned to Syntax’s 24×7 Security Operations Center (SOC), which monitors the customer’s environment to prevent any future, more sophisticated ransomware attacks. Syntax’s SOC helps enterprises overcome the growing shortage and high cost of security talent and operates around the clock to answer any questions or address any security issues. Hackers usually attack on the weekends and late at night so it’s important to have 24/7 coverage.
Other Syntax security services include providing recommendations on the ransom, assisting in acquiring and validating keys for decryption, developing and implementing a plan to recover impaired systems, reverse engineering attacker-provided decryption utilities to ensure no malicious code exists, and investigating to identify the attack vector and any other malicious activity on the network.
How we are different
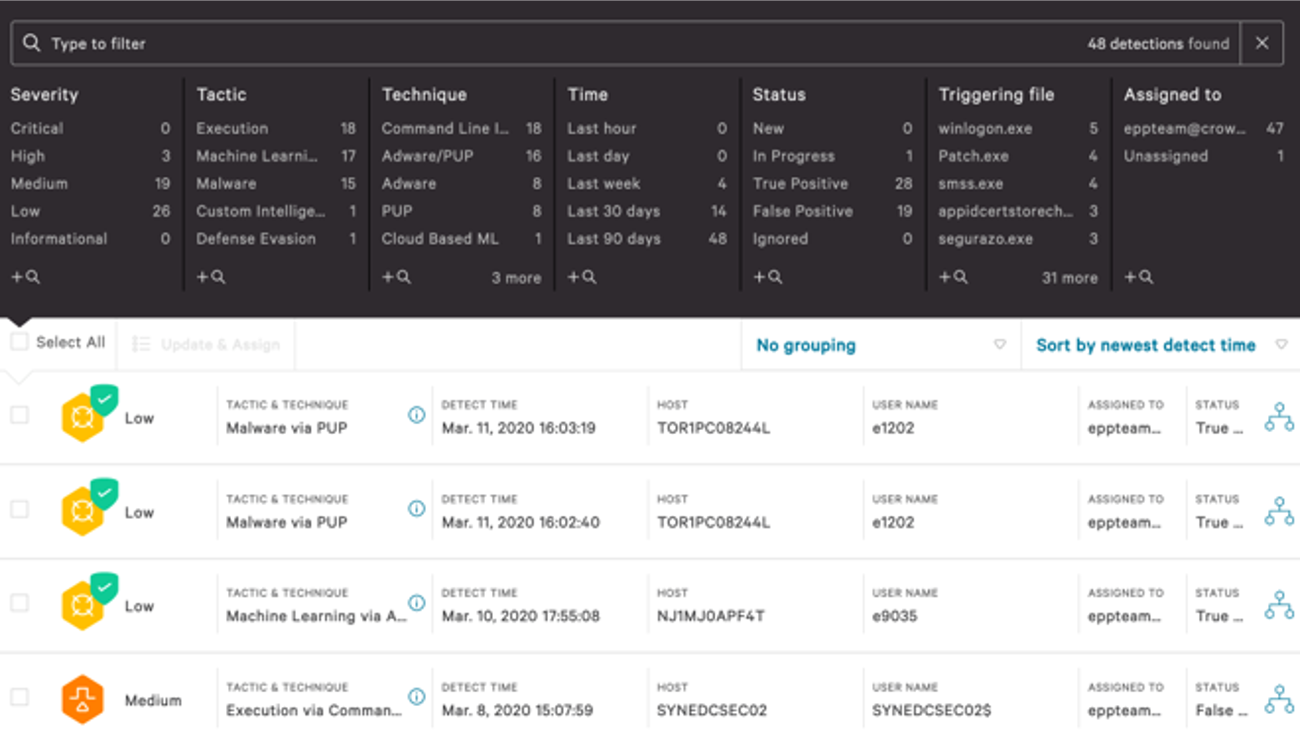
Syntax’s partnership with CrowdStrike helps determine risks and exposure immediately:
Syntax’s partnership with CrowdStrike helps a company pinpoint the adversaries perpetrating their network and systems. Syntax can set up and deploy an endpoint detection and response (EDR) solution so customers know their cybersecurity risks and exposure immediately. Syntax works with CrowdStrike to conduct forensic analysis, resolve immediate issues, and implement a long-term solution to stop future attacks. One of the advantages of Syntax’s partnership with CrowdStrike is its ability to provide customers with next-generation security technologies that move beyond traditional signature-based antivirus solutions that are ineffective against sophisticated ransomware attacks. Syntax leverages CrowdStrike’s best-in-class product that is in the upper right-hand corner of Gartner Magic Quadrant for Endpoint Protection, and also utilizes their professional services team.
Immediate response team and security operations center:
Syntax’s 24x7 Security Operations Center (SOC) monitors and manages a customer’s environment after a ransomware attack to prevent a future and more sophisticated attack by hackers. Syntax’s SOC helps customers overcome the growing shortage and high cost of security talent so they can successfully secure their environment to prevent future security breaches. It also has a team that monitors and manages environments during the weekend and late at night when ransomware attacks usually happen.
Syntax’s Endpoint Detection and Response (EDR) solutions:
Syntax’s Managed EDR solution records and stores endpoint system-level behaviors, and uses various data analytics techniques to detect suspicious system behavior, provide contextual information and remediation suggestions to restore affected systems, and block malicious activity. The EDR solution provides advanced algorithms to detect and contain ransomware based on the bad actors’ behavior to allow a company to become ransomware-resistant by utilizing next-generation security technologies. Customers can also work directly with CrowdStrike, but many defer to Syntax given our expertise in managed services.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



