Photo Gallery
 |

 |
Tenable.io™

Additional Info
| Company | Tenable, Inc. |
| Company size | 500 - 999 employees |
| Website | http://www.tenable.com |
NOMINATION HIGHLIGHTS
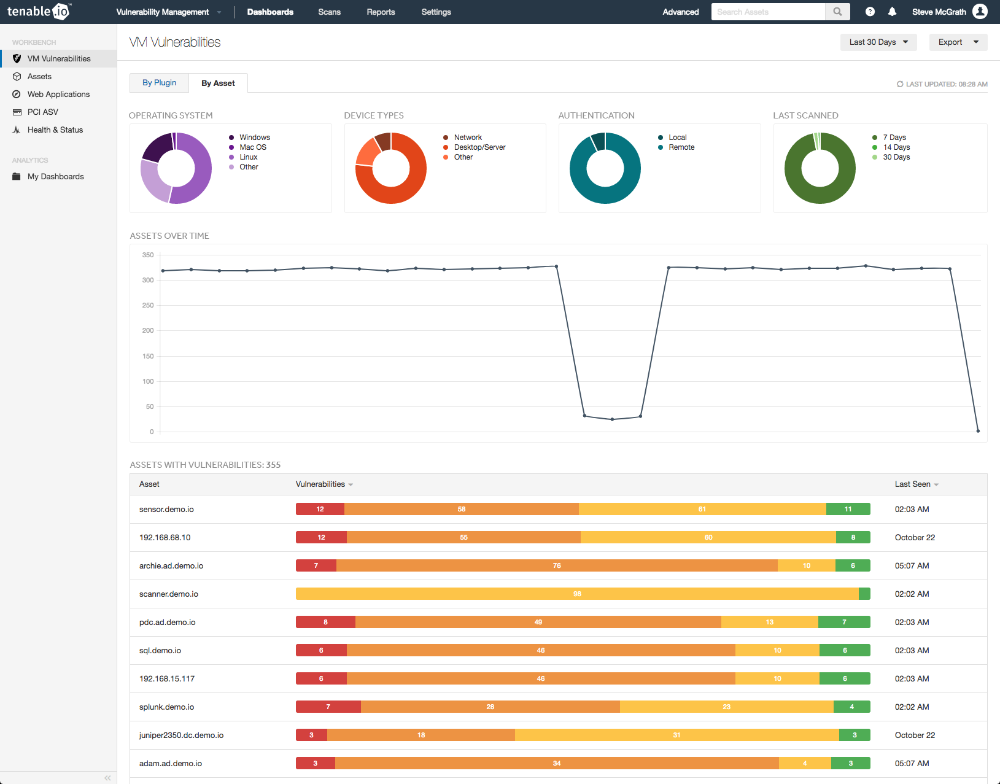
Today’s modern attack surface is now a complex mix of compute platforms and assets spanning IT, cloud, containers, mobile, IoT and more. Information security teams can barely keep up with the pace of identifying vulnerabilities, let alone prioritize and make sense of what is found. This volume of data and pace of change coupled with the industry’s cybersecurity skills shortage means it’s more critical than ever for security teams to have a clear view of all vulnerability data and how to prioritize it, within a single intelligent solution. Tenable.io provides the industry’s first Cyber Exposure platform, an evolution of vulnerability management that delivers visibility into any asset on any platform and guidance on how to act.
Built on the industry-renowned Nessus technology, Tenable.io’s comprehensive scanning, passive network monitoring, and true asset tracking – all key differentiators – help eliminate vulnerability blind spots. Passive monitoring gives security teams continuous visibility into both managed and unmanaged assets on their networks, while agents monitor on- and off-network endpoints. To more accurately track vulnerabilities while accommodating dynamic environments, Tenable.io offers true asset tracking and the industry’s first elastic asset licensing model. This allows customers to easily and accurately identify, track and license all their assets – even short-lived assets like cloud and containers – while reducing costs and not double counting.
Tenable.io also helps security teams better prioritize vulnerability remediation, based on whether a vulnerability can be easily exploited, if an exploit kit exists for it, and if it is in the news. Tenable.io’s well documented API and SDK and pre-built integrations make it easier for customers to programmatically access Tenable.io and use it in broader, automated business processes. The end result is a Cyber Exposure platform that helps customers measure their attack surface to accurately understand and reduce cyber risk.
How we are different
With the explosion of cloud adoption, the rise of DevOps processes, and the convergence of IT and OT, every organization has more at risk. Tenable.io is the first and only vulnerability management solution to provide asset discovery and vulnerability detection across the entire modern attack surface, including IT, cloud, web applications, containers, OT and IoT, in one solution.
One of the great weaknesses of traditional vulnerability scanning is that it is inherently limited to providing a point-in-time view of the network. With the speed of endpoints, cloud instances, virtual machines, and containers appearing and disappearing, such a limited view leaves organizations with a massive Cyber Exposure gap, unable to see the current state of their environment. That is why Tenable offers passive network monitoring – to see assets and discover vulnerabilities continuously – and we include it with Tenable.io at no extra cost. No other vulnerability management vendor offers this capability. Our patented passive monitoring technology is essential for live discovery of managed and unmanaged assets, continuous monitoring of the environment, and asset discovery and passive vulnerability detection of IoT & sensitive OT assets (which can't be scanned).
Tenable.io is also the first vulnerability management solution to offer container security capabilities, bringing security into the container build process up-front. By integrating directly into the DevOps (CI/CD) pipeline, Tenable.io provides vulnerability assessment, malware detection and policy enforcement prior to container deployment. This enables organizations to gain visibility into the hidden security risks present in container images and to remediate them before they reach production, all without slowing innovation cycles.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



