Photo Gallery
|

|
Tenable.ot

Additional Info
| Company | Tenable, Inc. |
| Company size | 1,000 - 4,999 employees |
| Website | http://www.tenable.com |
NOMINATION HIGHLIGHTS
Digital transformation has made much of the operational technology (OT) that runs critical infrastructure internet-accessible, bringing efficiencies and converging these once isolated systems with IT. Today’s critical infrastructure is vulnerable as security incidents can traverse across both IT and OT environments to cause potentially devastating business impacts, such as halted operations or unsafe product output.
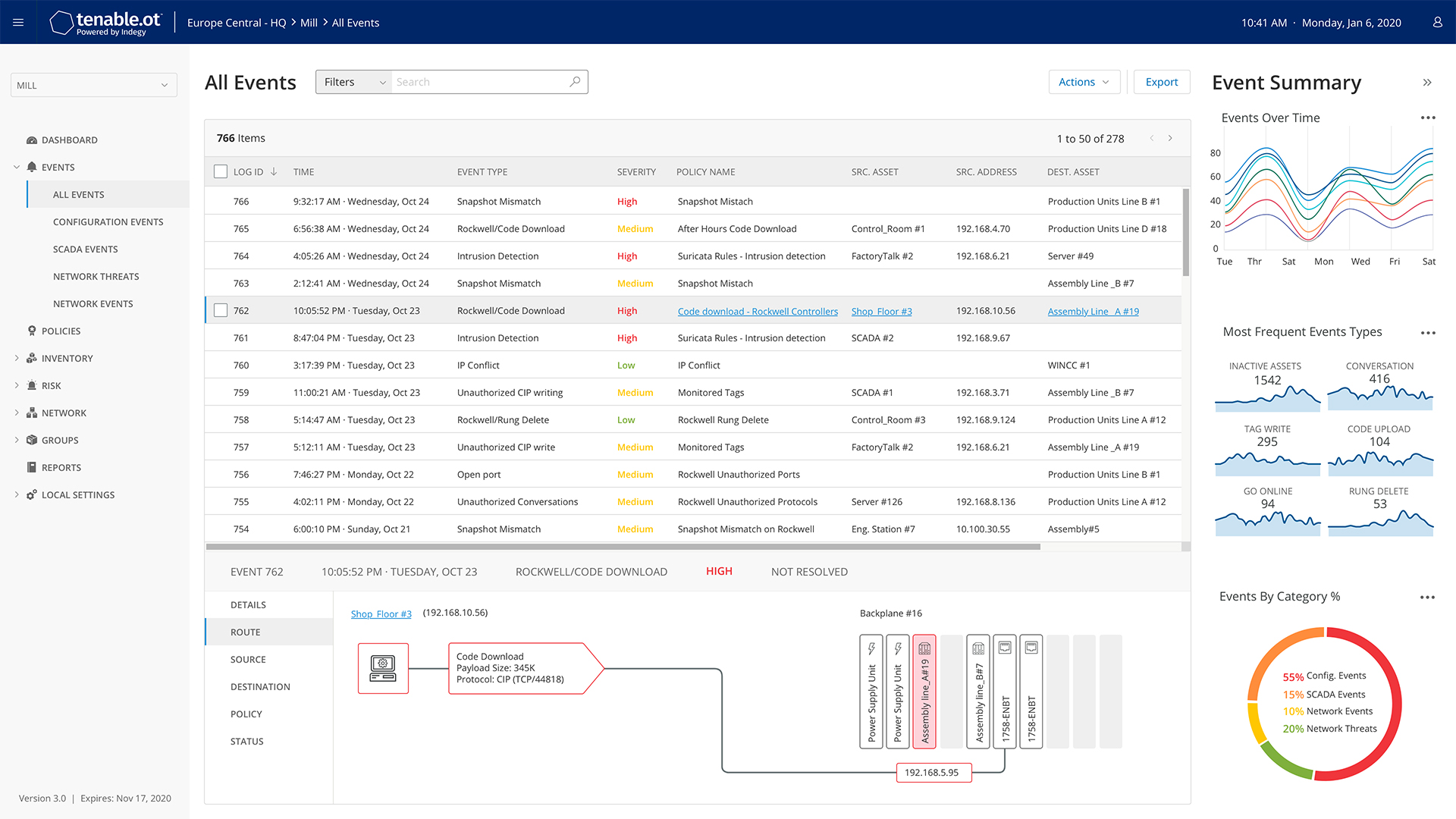
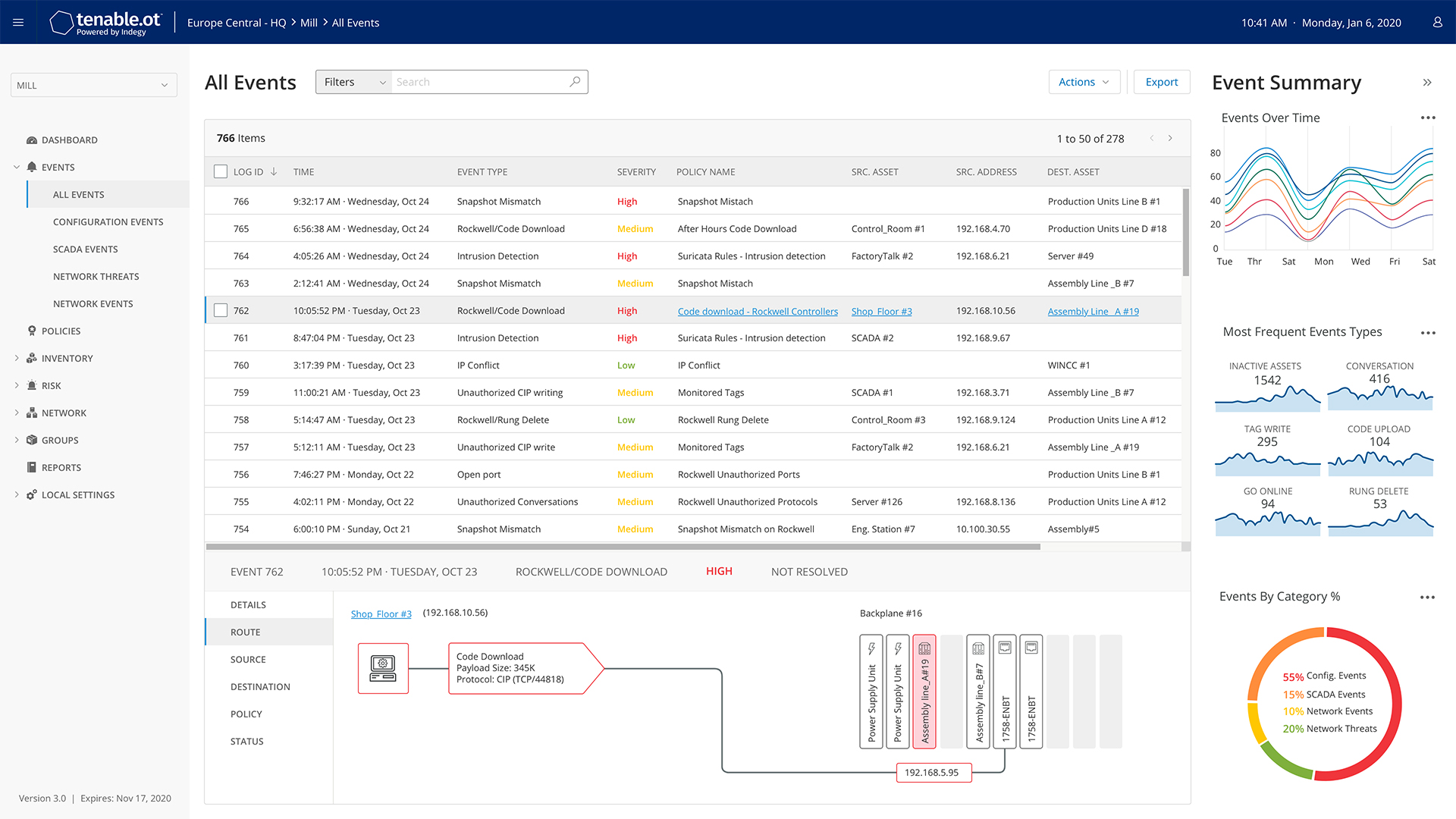
Tenable introduced Tenable.ot™, which includes Nessus® Professional, to help organizations address cyber exposure in converged environments. The first-of-its-kind innovation, Tenable.ot presents unmatched visibility, security and control with real-time insights about IT within OT environments, enabling security teams to attain holistic visibility, predict threats and act to address risk.
Features and capabilities include:
Threat Detection and Mitigation
Tenable.ot’s multi-detection engine identifies policy violations, detects anomalous behaviors and tracks signatures for potential high-risk events. Users benefit from granular control over detection methods while real time vulnerability insights allow users to quickly respond and mitigate threats to prevent operational impacts.
Adaptive Assessment
Tenable.ot offers unparalleled situational awareness into IT/OT infrastructure, without impacting operations. This patented active approach gathers significantly more information than passive monitoring alone, including identification of devices that do not communicate across the network.
Risk-Based Vulnerability Management
Tenable’s Vulnerability Prioritization Rating (VPR) provides a detailed, threat-based vulnerability score optimized for both IT and OT assets that takes into account the severity of vulnerabilities combined with the existence of public proof-of-concepts (PoC), Dark Web chatter and more. This enables users to quickly identify high-risk vulnerabilities for priority remediation.
Configuration Control
Tenable.ot provides a full history of device configuration changes to enable administrators to establish a backup snapshot with the “last known healthy device state” for swift recovery and compliance with industry regulations.
Enterprise Management
Designed for distributed environments, Tenable.ot provides centralized security, vulnerability management, and full reporting capabilities, regardless of location.
How we are different
OT has been brought online as organizations drive digital transformation efforts with new technologies. This has converged OT with IT, expanding the attack surface and introducing new attack vectors that can impact critical infrastructure. Solely securing a singular environment can translate to significant blind spots, leaving critical infrastructure at risk. Tenable.ot is a first-of-its-kind, industrial-grade solution that allows organizations to attain and maintain continuous visibility, insight and control across both IT and OT environments.
As the era of convergence continues, organizations look to protect new technologies from outside threats and to equip security teams with real-time insights to maintain holistic visibility, predict oncoming threats and act to address cyber risk. Tenable.ot differentiates itself by bringing a single pane of glass and rich vulnerability criticality data with Vulnerability Priority Ratings (VPR) to prioritize and expedite vulnerability response workflows across converged environments.
With the added contextual insight into the network as well as the devices on the network, security teams are better poised to prioritize high-risk threats. This functionality within Tenable.ot, alongside its unique anomaly detection, configuration control capabilities, threat intelligence and unmatched vulnerability coverage, allow organizations to build out robust OT security programs that work in conjunction and are fully integrated with leading security products that may be already implemented in the existing environment. With Tenable.ot, organizations supporting critical infrastructure can benefit from the efficiencies and cost savings of leveraging new technologies without introducing unnecessary and unacceptable risk.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

