Photo Gallery
 |
 |
Threat Stack Cloud Security Platform

Additional Info
| Company | Threat Stack |
| Company size | 70 employees |
| Website | https://www.threatstack.com/ |
NOMINATION HIGHLIGHTS
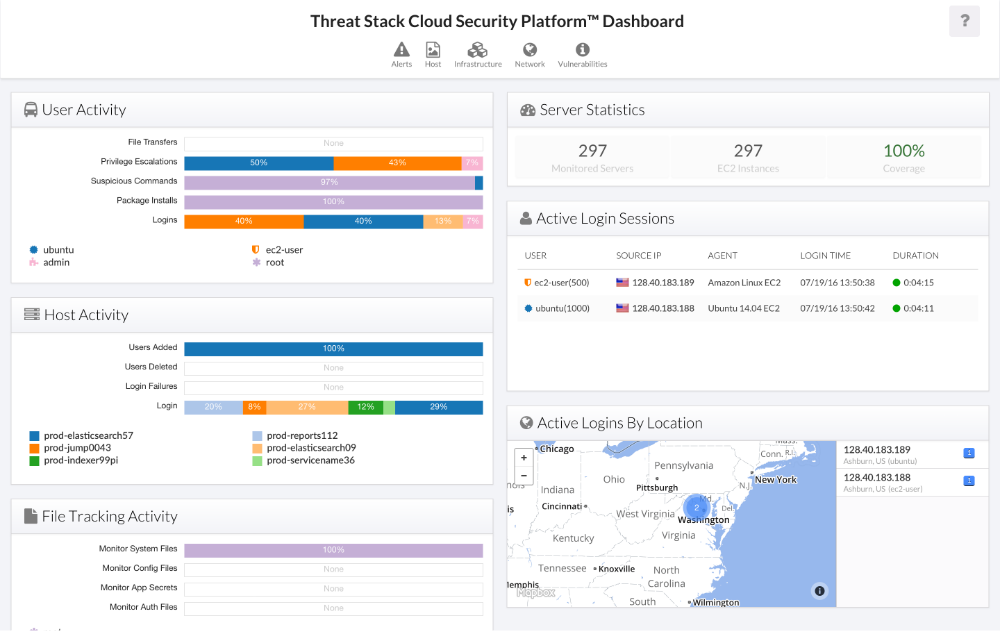
Threat Stack Cloud Security Platform (CSP) is designed for companies of all sizes operating on premise or in public, private or hybrid cloud environments.
Whether a company is just transitioning to the cloud, well-established in the cloud or has built its business in the cloud from day one, it is critical to integrate continuous security monitoring into its environment to assure immediate detection of anomalous or suspicious behavior. Threat Stack CSP helps customers of all sizes and levels of cloud maturity achieve this visibility and protects against external attacks, insider threats and data loss. Unlike point solutions available today, Threat Stack CSP assures integrated and contextualized security through each stage of the cloud security journey by providing:
-AWS Configuration Auditing that scans to ensure the proper security settings are in place and enabled, while achieving an accurate security baseline.
-Cloud workload insights that help organizations verify – in real-time – whether their environments have been compromised by external attacks, insider threats and/or data loss.
-Infrastructure monitoring that tracks changes to infrastructure in real-time and generates infrastructure alerts based on user, event name, counts of events and source IP.
-Vulnerability assessments that analyzes packages against common vulnerabilities and exposure (CVEs).
-Threat intelligence that knows when workloads are communicating to known “bad hosts”.
-Compliance reporting the helps customers meet compliance for HIPAA, PCI DSS, SOC 2, ISO 27001 and SOX 404 regulations.
Fast-growing companies traditionally had to sacrifice speed and efficiency to run securely and compliant in the cloud. Threat Stack CSP removes the expense, complexity and time required to identify and verify threats and keep data protected. It auto-scales to the demands of rapidly changing infrastructure and offers automated integrations with leading DevOps tools and workflows, giving users complete security visibility.
How we are different
-Threat Stack CSP eliminates the need for customers to procure fragmented security products, and provides a single-pane-of-glass view into integrated workload insights, infrastructure monitoring, vulnerability management, threat intelligence and compliance reporting for faster detection and remediation.
-It’s the only cloud security monitoring platform on the market that can meet the cloud security needs of any company at any phase of cloud maturity - from those who are just transitioning to the cloud to those that are cloud-native and taking a more sophisticated approach.
-Threat Stack is unique in its simplicity, designed to eliminate the complexity, time and expense it takes to deploy, configure, integrate and manage security services. The platform was built in the cloud for the cloud, with scalability in mind, automatically scaling up and down with the capacity of a customer’s infrastructure to ensure continuous visibility across the environment.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



