Photo Gallery
 |

 |
Threat Stack, Inc


Additional Info
| Company size | 100 - 499 employees |
| World Region | North America |
| Website | http://www.threatstack.com |
NOMINATION HIGHLIGHTS
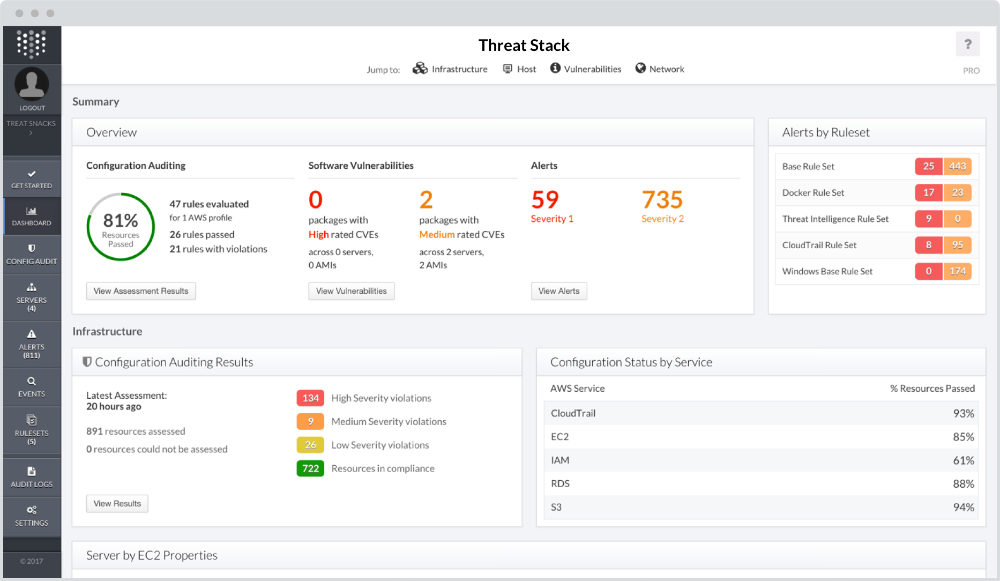
Threat Stack is tackling one of the most important problems facing cloud-based companies today — security visibility across the entire back-end infrastructure. We’re doing this by giving security, operations, and development professionals one platform to leverage and understand whether all compliance standards, best practices, and centralized workflows are being followed across the organization.
Through key innovations, Threat Stack addresses a large number of security-related issues for SMB to Enterprise such as achieving compliance, moving upmarket, and strengthening internal security practices and policies across any cloud or on-prem infrastructure.
Our mission goes beyond delivering a comprehensive Intrusion Detection Platform to educating the market about how they can better protect themselves, approach security in the context of today’s cybercrime environment, and implement smart security practices across the organization.
How we are different
- Rather than the traditional signature-based approach, Threat Stack sits at the host level and uses a behavior-based approach to intrusion detection that sends real-time alerts about any abnormal behavior from both internal and external sources.
- Threat Stack makes security part of the everyday build and release cycle rather than a potential blocker at the end of the project. Teams using Threat Stack are able to move securely at the speed of DevOps.
- With continuous monitoring and real-time alerting, Threat Stack users can be certain that there are always eyes on their infrastructure. This expands beyond their own data to their customer data, which Threat Stack users know exists in a safe, secure, and compliant environment

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



