Photo Gallery
 |
 |
ThreatConnect

Additional Info
| Company size | 100 - 499 employees |
| World Region | North America |
| Website | https://www.threatconnect.com/ |
NOMINATION HIGHLIGHTS
ThreatConnect has unquestionably helped pioneer and define the threat intelligence space with its product innovation. It’s helping the entire cybersecurity industry sort through and prioritize the intelligence arising from dozens of third-party tools used by their customers, essentially making every one of those tools more useful.
2017 was a pinnacle year for ThreatConnect as it launched a new product suite allowing organizations of any size or maturity level to leverage threat intelligence to make more informed business decisions. Through its four new products, TC Identify, TC Manage, TC Analyze, and TC Complete, ThreatConnect now addresses all levels of need, whether a team of one or many. This year, ThreatConnect also introduced a first of its kind capability, Multi-Environment Orchestration – enabling organizations the flexibility and scalability needed to unify their security management across their digital business, from cloud to office networks or virtual.
In 2017, ThreatConnect’s Platform helped some of the largest companies across industries to sort through and manage their threat intelligence programs. US Fortune 500 companies using ThreatConnect have increased 15% this year alone. Today, nearly half of the Fortune 100 and nearly a quarter of the Fortune 500 are using the platform – showing its reach across top US organizations.
ThreatConnect’s contribution to the broader cybersecurity community can be seen in both its product advancements and research team. In 2017, ThreatConnect reached 100 total integrations, allowing its platform to easily integrate with a wide range of existing security products – fostering maximum collaboration and information sharing.
Additionally, ThreatConnect’s research team has been a leader in identifying and sorting through data surrounding some of the year’s largest cybersecurity events, including Fancy Bear, NotPetya, WannaCry and others. The team’s research is shared among the cybersecurity community to elevate organizations’ ability to mitigate and manage current and future threats.
How we are different
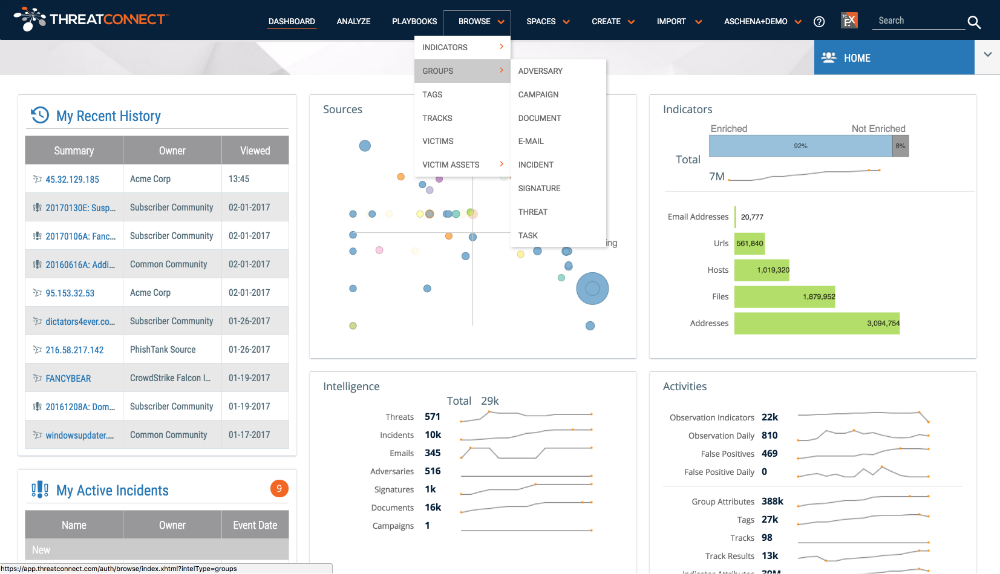
• Dashboard control isn't a new concept but a single view across the cloud, on premise and everything in between can be elusive in security products. ThreatConnect's new built-in and customizable dashboards help users easily visualize data that displays the impact of their security efforts and gain a better understanding of the threats their organizations face. By viewing the built-in dashboards or creating their own and adding custom metrics - even from outside of ThreatConnect - analysts are able to make critical security operations decisions and act to mitigate them quickly.
• While many of today's threat intelligence platforms enable some orchestration, ThreatConnect introduced platform-level multi-environment orchestration to the industry - allowing "Playbooks" (which enable automation of almost any cybersecurity task) to run across multiple environments including cloud, office networks, or virtual. This first of its kind security orchestration capability provides organizations the flexibility and scalability they need to unify their security management across their entire digital business and take action seamlessly across networks. Multi-environment orchestration is especially beneficial to MSSPs because of its ability to enable multi-tenancy without creating repetitive tasks. Providers' ability to manage security workflows for multiple customer environments from a single platform with ThreatConnect is unmatched.
• ThreatConnect's Research Team is an elite group of globally acknowledged cybersecurity analysts that consistently put forward news making intelligence. The team comprises some of the industry's best, arising from intelligence agencies and the most informed analyst circles, and are informing the ThreatConnect platform and the entire cybersecurity community about emerging threats. The team curates an intelligence source, TC Identify™, which provides vetted, actionable threat intelligence compiled from more than 100 open source feeds and crowdsourced intelligence from within our dozens of communities, our own ThreatConnect Research Team, and the option to add intelligence from any of our TC Exchange™ partners.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



