Photo Gallery
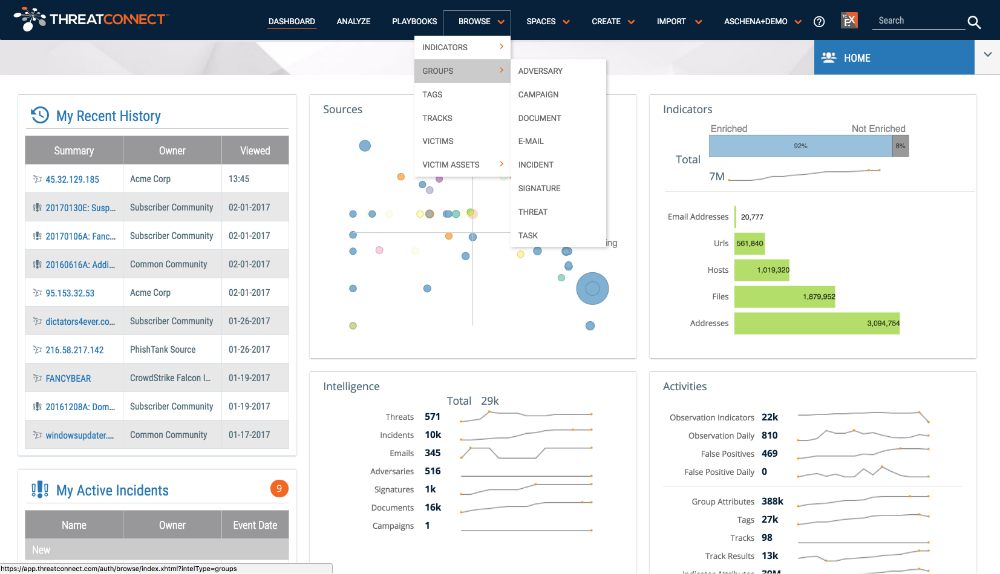 |
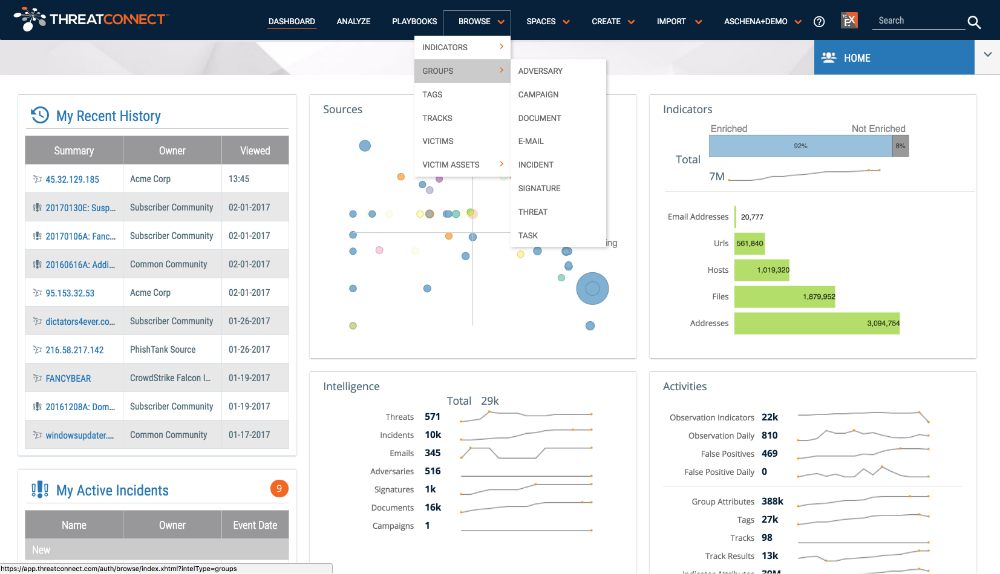
ThreatConnect Platform
Additional Info
| Company | ThreatConnect |
| Company size | 100 - 499 employees |
| Website | https://www.threatconnect.com/ |
NOMINATION HIGHLIGHTS
The ThreatConnect Platform is the industry’s only extensible, intelligence-driven security platform. It is helping the entire cybersecurity industry to sort through and prioritize the intelligence arising from the dozens of third-party tools used by their customers, essentially making every one of those tools more useful. And, unlike others in the industry, it offers a suite of four products built on the ThreatConnect platform that are designed for teams of all sizes and maturity levels. This enables the Platform to adapt with organizations as they grow and their security needs change.
The ThreatConnect platform also includes several innovative capabilities, including Playbooks which automates almost any cybersecurity task using an easy and intuitive drag-and-drop interface – with no coding needed. This feature enables teams to automate and orchestrate time consuming tasks to reduce them from hours or days to seconds. This year, ThreatConnect also introduced a first of its kind capability, Multi-Environment Orchestration – enabling organizations the flexibility and scalability they need to unify their security management across their digital business, from cloud to office networks or virtual. This first of its kind orchestration capability is especially beneficial to managed security service providers (MSSPs) as they can manage security workflows for multiple customer environments from a single platform.
ThreatConnect’s flagship product, TC Complete, enables informed strategic and tactical decision-making based on the power of an organization’s threat intelligence. With TC Complete, the industry’s first security operations and analytics platform, organizations can run their security operations center with high efficiency and effectiveness, thereby detecting threats faster. With the ability to proactively hunt and detect threats, leverage comprehensive and normalized threat data, and automation and orchestration, TC Complete brings analysts and security operations teams unparalleled efficiency and confidence in security threat detection and decision making in one central place.
How we are different
• While security is a top priority for organizations large and small, ThreatConnect recognized that no security product can effectively act as a “one-size-fits-all” solution. This year, it announced a new suite of products designed for organizations at any maturity level. Through its four new products, TC Identify, TC Manage, TC Analyze, and TC Complete, it can now address all levels of need in the marketplace, whether a team of one or many. All products are built on the ThreatConnect Platform which was created to help organizations understand adversaries, automate their security operations, and mitigate threats faster using threat intelligence; and can adapt as organizations grow and change.
• In 2017, ThreatConnect’s platform helped some of the largest companies across industries to sort through and manage their threat intelligence programs. US Fortune 500 companies using ThreatConnect have increased 15 percent this year alone, and Fortune 100 companies using the platform have increased 16 percent. Today, nearly half of the Fortune 100 and nearly a quarter of the Fortune 500 are using the platform – showing the platform’s reach across some of the top organizations in the US.
• ThreatConnect is committed to extensibility and a unified defense by bringing together its customers’ specialized and disparate solutions. In 2017 alone, ThreatConnect has added more than 15 new integrations with other security products, bringing its total integrations to over 100. ThreatConnect also operates an open application programming interface (API) that enables users to easily integrate with their existing security products. Users can ingest data from their current tools into ThreatConnect or push ThreatConnect’s own multi-sourced, curated threat intelligence back into those tools. ThreatConnect currently integrates with industry-leading enrichments tools, open source and premium feeds, security products and is continuing to add more integrations every month.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



