Photo Gallery
|


|
ThreatDefence XDR Platform

Additional Info
| Company | ThreatDefence |
| Company size | 10 - 49 employees |
| Website | https://www.threatdefence.com |
NOMINATION HIGHLIGHTS
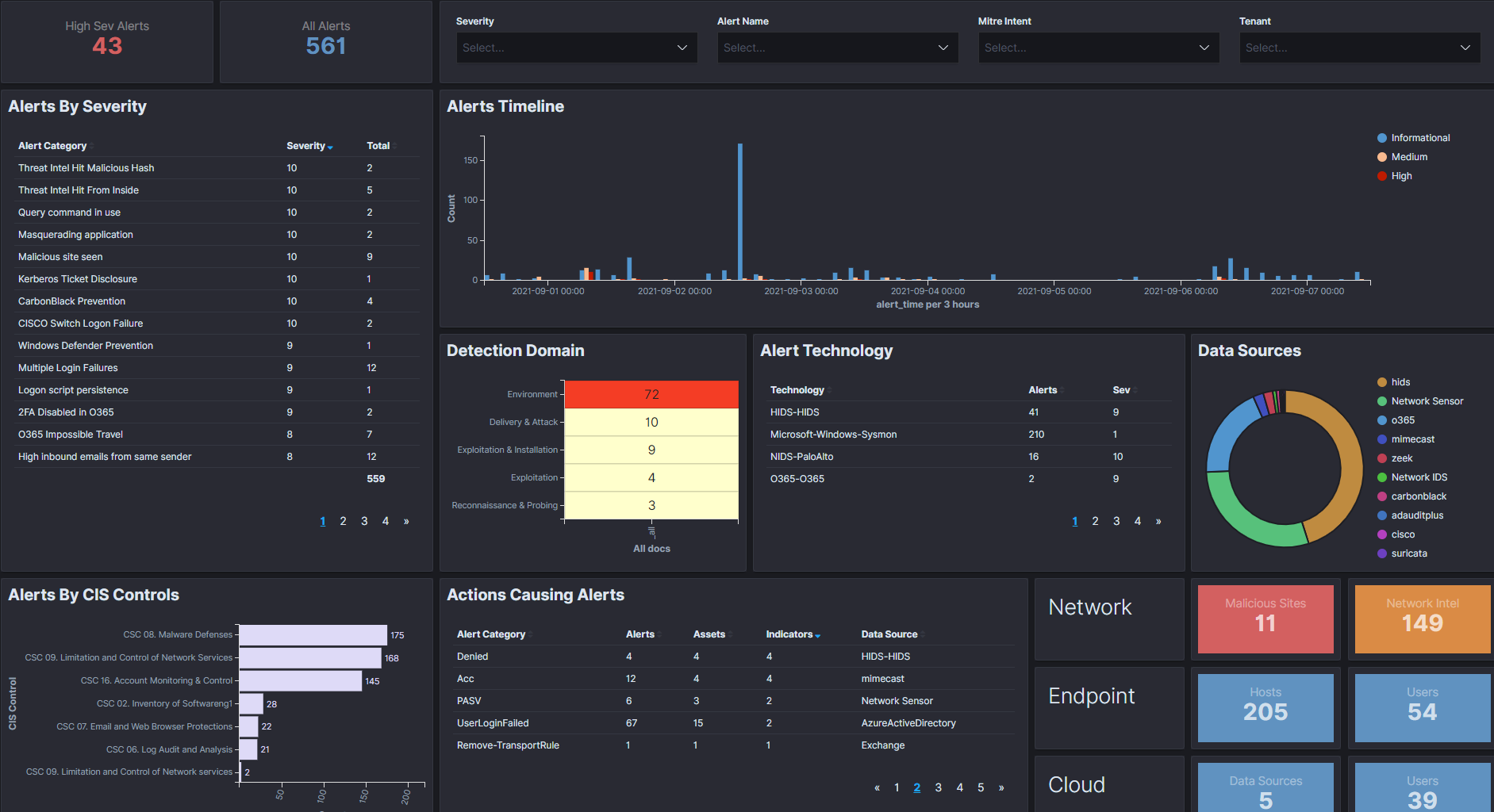
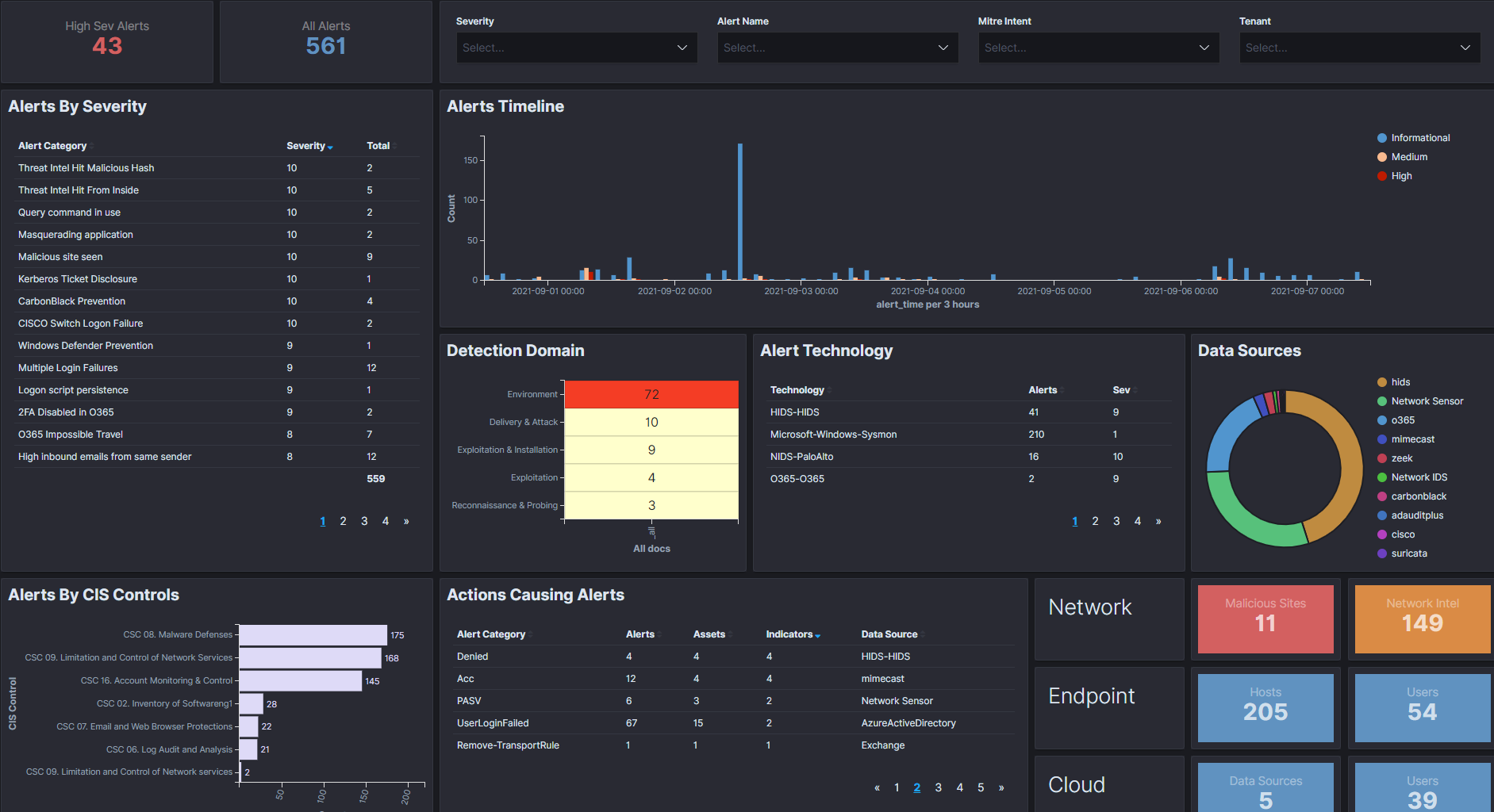
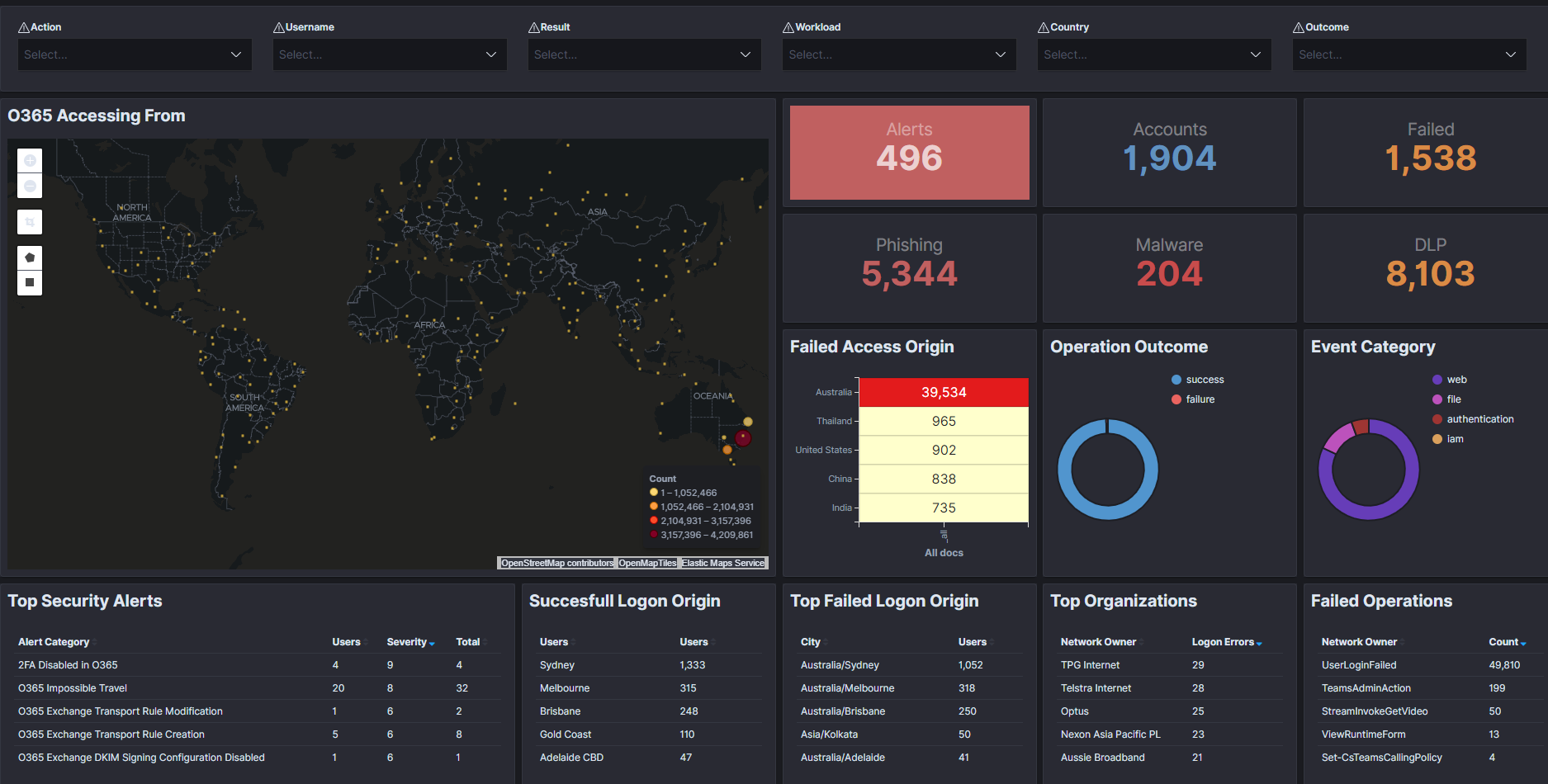
Our XDR platform is the foundation of effective cyber threat detection and response services. Providing deep visibility, great threat detection, sophisticated behaviour analytics and automated threat hunting, the platform adds efficiency and value to your security operations capability. Leveraging our proprietary detection methodologies, including AI-empowered machine learning, our platform uncovers suspicious and anomalous behaviour revealing even the most hidden threats.
The platform creates high fidelity detections, flagging real threats and assisting SOC analysts and investigators to focus on what really matters. Our XDR platform equips cyber security experts with the insights and tools they need to perform deep investigations and contain threats, all in real time.
Our platform provides next generation Threat Hunting, Incident Response and Digital Forensics capabilities across the entire enterprise attack surface. We provide deep visibility, remote triage and evidence gathering, and in-depth investigation and incident recovery on a scale.
The platform provides:
– End-to-End Incident Management
– Enterprise-wide Forensics, collecting as much data as possible from your systems and networks
– Deep real-time visibility and extraction of forensic artefacts, RAM, registry keys and file systems objects, including deleted data and unallocated disk space, as well as an ability to intelligently analyze user, machine and software behavior
– across the entire attack surface of an organization, and operating at the enterprise-wide scale
– Reaching to all assets and networks across your entire enterprise.
How we are different
Our platform provides:
1. AI-assisted threat hunting, investigation, and incident response, providing automated threat detection, containment, and artefact acquisition.
2. Enterprise-wide digital forensics capability, enabling security analyst to run forensic searches remotely over unlimited number of endpoints
3. Deep real-time visibility across the entire attack surface, recording even the most subtle security events missed by our competitors.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

