Photo Gallery

|


|
ThreatMon Supply Chain Risk Management


Additional Info
| Company | THREATMON |
| Company size | 40-69 employees |
| World Region | North America |
| Website | https://threatmon.io/ |
NOMINATION HIGHLIGHTS
Modern enterprises are no longer evaluated solely by their own security posture. A single vulnerability within a third-party vendor can trigger cascading operational, financial, and reputational damage across the entire ecosystem.
ThreatMon’s Supply Chain Risk Intelligence module redefines Vendor Risk Management by transforming fragmented external signals into structured, prioritized, and business-aligned risk intelligence.
Unlike traditional questionnaire-driven or self-declared compliance tools, ThreatMon provides a continuous outside-in view of third-party exposure. The platform discovers and normalizes externally visible supplier assets; domains, subdomains, IP addresses, web and mobile applications, and cloud endpoints mapping them into a canonical vendor/asset graph
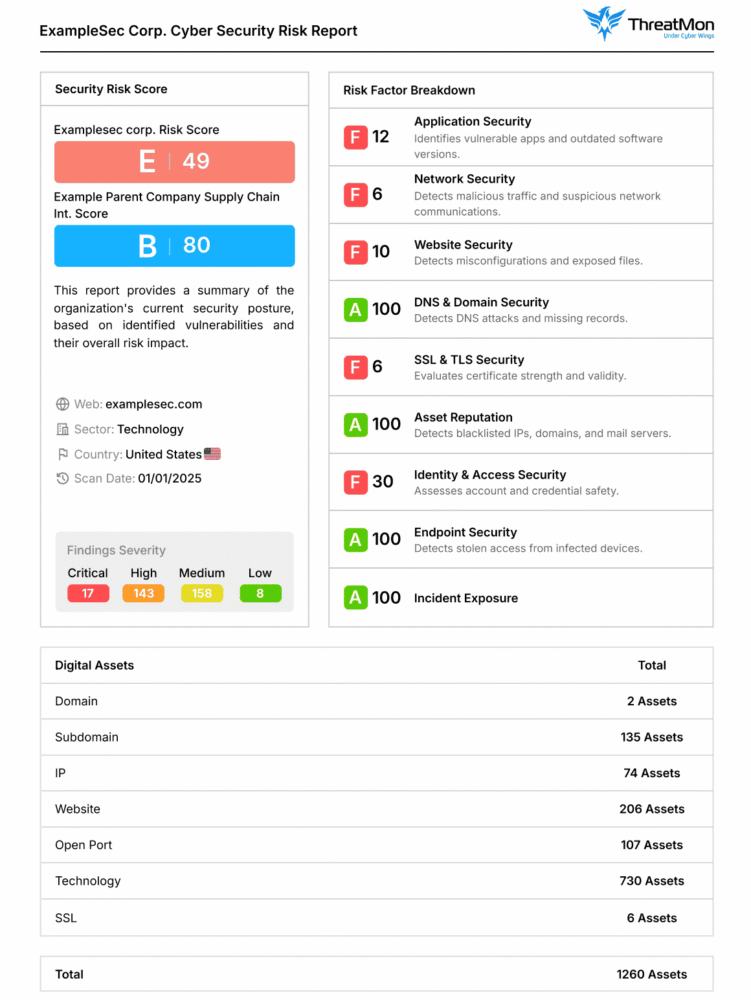
It then aggregates external signals including vulnerabilities, open services, leaked credentials, dark-web findings, and threat feeds to compute a weighted vendor risk score This scoring model factors in CVSS severity, finding volume, asset criticality, and threat context to produce a prioritized risk posture.
The system operates on more than 200 high-fidelity checkpoints and evaluates risk across nine distinct security domains including Application, Network, DNS/Domain, TLS, Identity & Access, Reputation, Endpoint, and Incident Exposure
What differentiates ThreatMon is its Business-Criticality Weighting model
Organizations can tune scoring logic to reflect operational dependency and real-world impact, ensuring remediation efforts focus on vendors that truly introduce cascade risk. Each vendor receives an individual Business Risk Vendor Score, alongside an aggregated ecosystem risk view .The output is not just a number but an actionable remediation roadmap supported by executive-ready reports and deep technical insights. ThreatMon moves Vendor Risk Management from static assessment to continuous intelligence-driven governance, delivering measurable, prioritized, and context-rich third-party security visibility at scale.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

