Photo Gallery
 |
ThreatStream
Additional Info
| Company | Anomali |
| Company size | 100 - 499 employees |
| Website | https://www.anomali.com |
NOMINATION HIGHLIGHTS
ThreatStream is the leading Threat Intelligence Platform, empowering organizations to identify, investigate, and respond to relevant security threats. ThreatStream automates the collection, enrichment, and integration of threat intelligence to help analysts make more informed decisions.
The past three years of Ponemon Reports consistently find that a growing majority of organizations believe a Threat Intelligence Platform (TIP) is necessary to maximize the value of intelligence data. Exceptional global adoption of ThreatStream supports this finding. Customers include nearly 30% of the Fortune 100, four of the top five US banks and the Bank of England. ThreatStream now powers numerous ISACs (Information Sharing and Analysis Centers), enabling threat intelligence sharing across industry communities. ThreatStream has also earned multiple industry accolades, including the highest possible rating in an SC Lab product review, conducted by SC Magazine.
In recent years, Anomali has added numerous advanced capabilities to ThreatStream, including:
SDKs: Expansion of the partner ecosystem with the release of three software development kits (SDKs) enabling partners to integrate seamlessly with the Anomali Threat Platform. Partners can now integrate third party products, threat intelligence feeds, and analysis enrichments with the new SDKs.
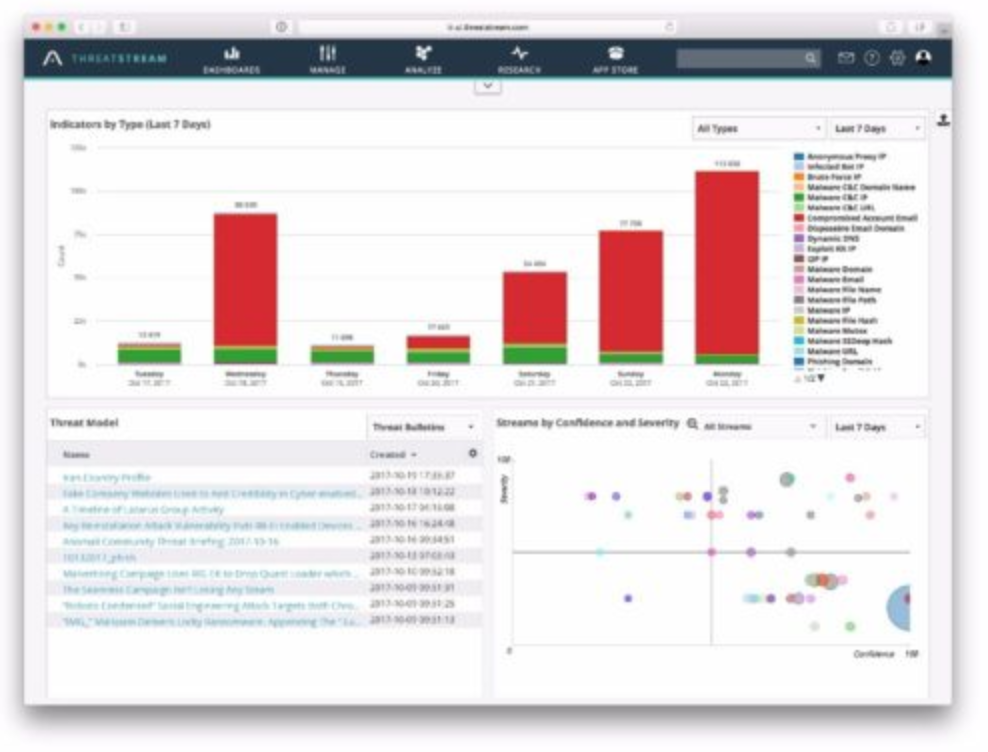
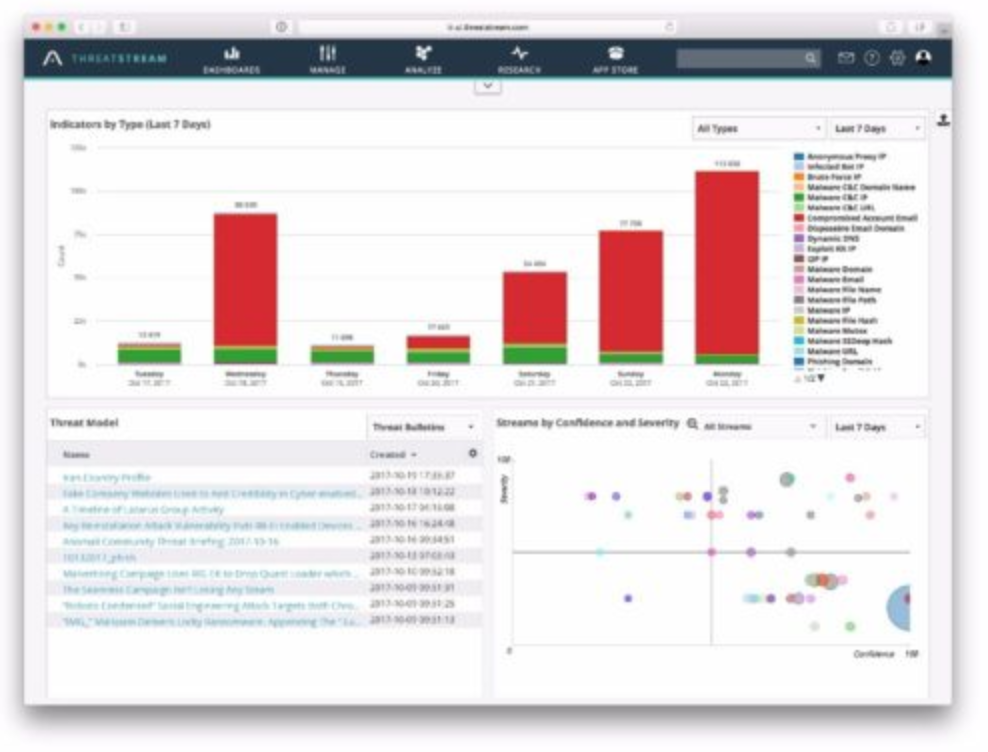
Analyst dashboards: Users can now tailor the dashboard and widgets to fit their needs, giving them more flexibility, control, and access to actionable information.
Phishing Indicator Analysis: Automatically extracts threat indicators from suspected phishing emails, which can then be integrated with internal security infrastructure and shared with other users to provide early warning.
Preferred Tags: Analysts leverage organization specific tags to streamline investigations, collaboration, and sharing of threat intelligence. Preferred and trending tags help ensure a consistent experience for all analysts using the platform.
Bidirectional Threat Intelligence: Client/server implementation enables bidirectional threat intelligence exchange with TAXII servers, allowing users to access and distribute threat intelligence over STIX/TAXII protocols.
How we are different
- Anomali ThreatStream is the market leader in threat intelligence platforms. ThreatStream has a growing customer base and numerous industry accolades.
- ThreatStream customers include thirty percent of the Fortune 100, comprised of organizations in every vertical, including financial services (four out of five top US banks), healthcare, and government.
- Anomali continues to add new capabilities to ThreatStream, including customizable Analyst Dashboards, Preferred Tags to empower organizations and expansion of the partner ecosystem with SDKs.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



