Photo Gallery
 |
ThycoticCentrify - Cloud Suite
Additional Info
| Company | ThycoticCentrify |
| Company size | 500 - 999 employees |
| Website | https://thycotic.com/ |
NOMINATION HIGHLIGHTS
As organizations modernize their IT estates and expand infrastructure from the data center to the cloud, they are faced with an exponential increase in identities and attack surfaces that challenges their ability to modernize their Privileged Access Management (PAM) in response.
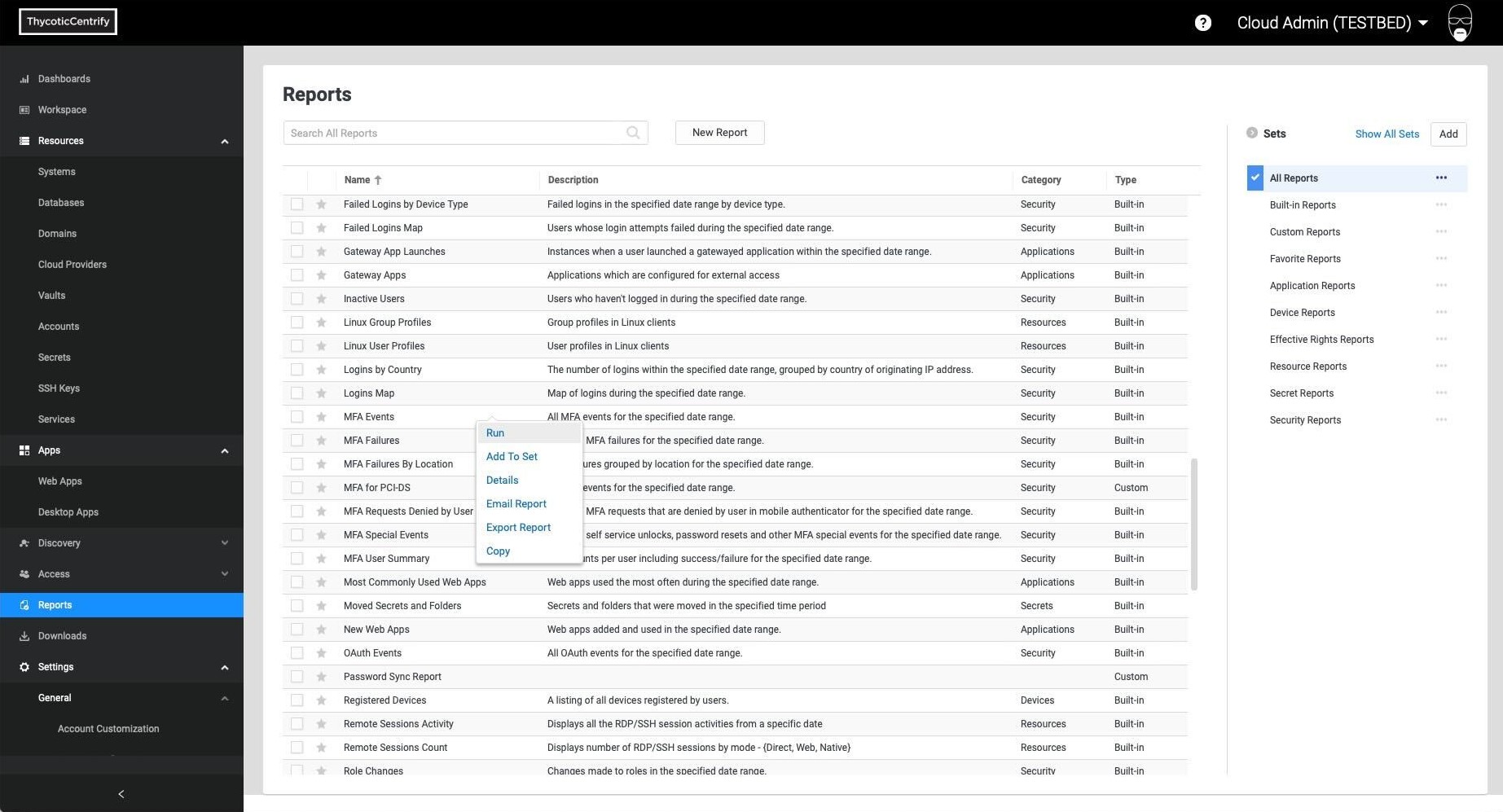
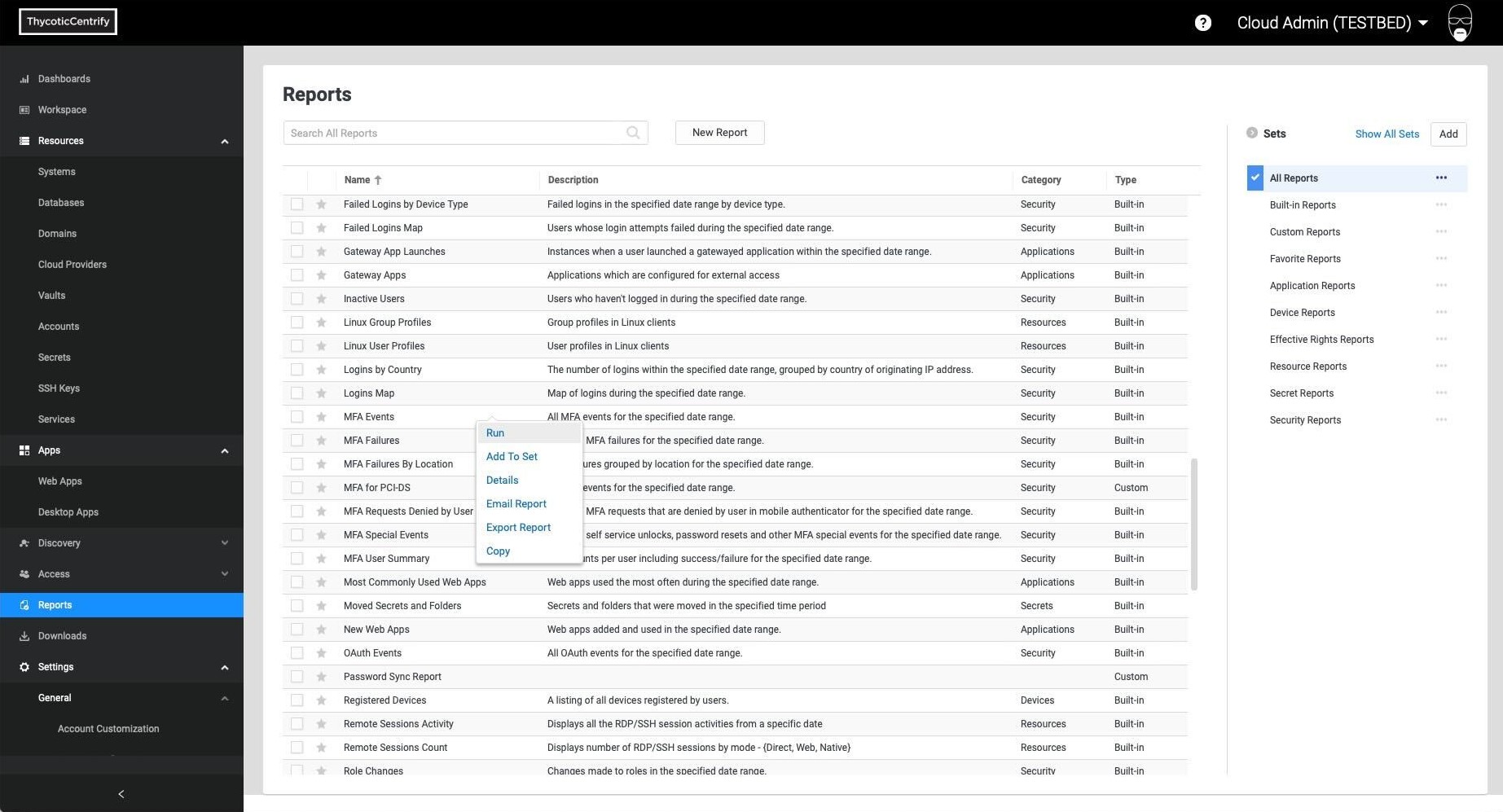
ThycoticCentrify Cloud Suite is a modern PAM solution that enables cloud transformation at scale. It empowers organizations to globally govern privileged access through centrally-managed policies dynamically enforced on the server — across elastic Windows and Linux workloads. With Cloud Suite, organizations minimize their attack surface by establishing trusted machine identities and leveraging corporate identities for authentication, implementing just-in-time privilege with multi-factor authentication (MFA), and securing remote access while auditing everything.
Cloud Suite leverages a native cloud platform to manage PAM policies centrally. As a SaaS service, it dovetails with an organization’s cloud environments, whether they be hybrid- or multi-cloud. It aligns with an organization’s Zero Trust or zero standing privileges requirements, implementing a least privilege access control model.
With Cloud Suite, organizations can:
Centrally Manage Access: Simplify user authentication to servers from any directory service including Active Directory, LDAP, and cloud directories. Organizations can take advantage of the benefits of the cloud without compromising the level of privileged access security and enterprise access they currently have on-premises.
Elevate Privilege: Consistent with a least privilege approach to PAM, organizations can enable users to request privilege when they need it to run privileged applications and commands, and if approved through the workflow process, it is granted for a limited amount of time and for a scoped set of systems.
Audit and Record Privileged Session Activity: Identify abuse of privilege, thwart attacks, and easily prove regulatory compliance with a detailed audit trail and video recordings that capture all privileged activity for visual proof that controls are in place and effective.
How we are different
1. PAM-as-a-Service: Easy to deploy and manage
As a cost effective, easy to integrate and low maintenance solution, Cloud Suite empowers users to take control of their privileged access accounts and credentials, and enforce a consistent privileged access security model across public cloud and on-premises infrastructure. Built with the end users in mind, Cloud Suite is a PAM-as-a-Service solution that is quick and easy to deploy (often up and running in under an hour), integrates seamlessly alongside other security solutions, removes management complexities, and has a comprehensive, yet easy to navigate, user interface.
2. Unique Hub-and-Spoke Architecture
Cloud Suite’s hub-and-spoke architecture makes scaling out PAM infrastructure simple and quick. A Cloud Platform SaaS tenant acts as the hub for shared services and centralized policy management. Lightweight Gateway Connector spokes deploy in minutes into infrastructure, linking it to the Cloud Platform to centrally manage and control access to new virtual instances and containers. This model avoids the hassles of a traditional PAM product that requires you to obtain and build-out supporting infrastructure and that depends on complicated vault synchronizations, failover, and disaster recovery.
3. Built in the Cloud, for the Cloud
Being ephemeral in nature, cloud infrastructure exposes new attack surfaces, as the number of machine identities explodes. Traditional PAM solutions - designed for on-premises infrastructure where policy management and policy enforcement controls are on the same network - can’t easily accommodate a decentralized architecture with control points in multiple VPCs/VNets and across multiple cloud providers. Built on a cloud native architecture, Cloud Suite fully protects an organization’s Windows, Linux, and UNIX estates as well as hybrid- and multi-cloud environments against identity-based attacks.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



