TrueFort Fortress Application & Cloud Workload Protection Platform
Recognized in the Category:
Photo Gallery
 |
TrueFort Fortress Application & Cloud Workload Protection Platform
Additional Info
| Company | TrueFort |
| Company size | 50 - 99 employees |
| Website | https://truefort.com/ |
NOMINATION HIGHLIGHTS
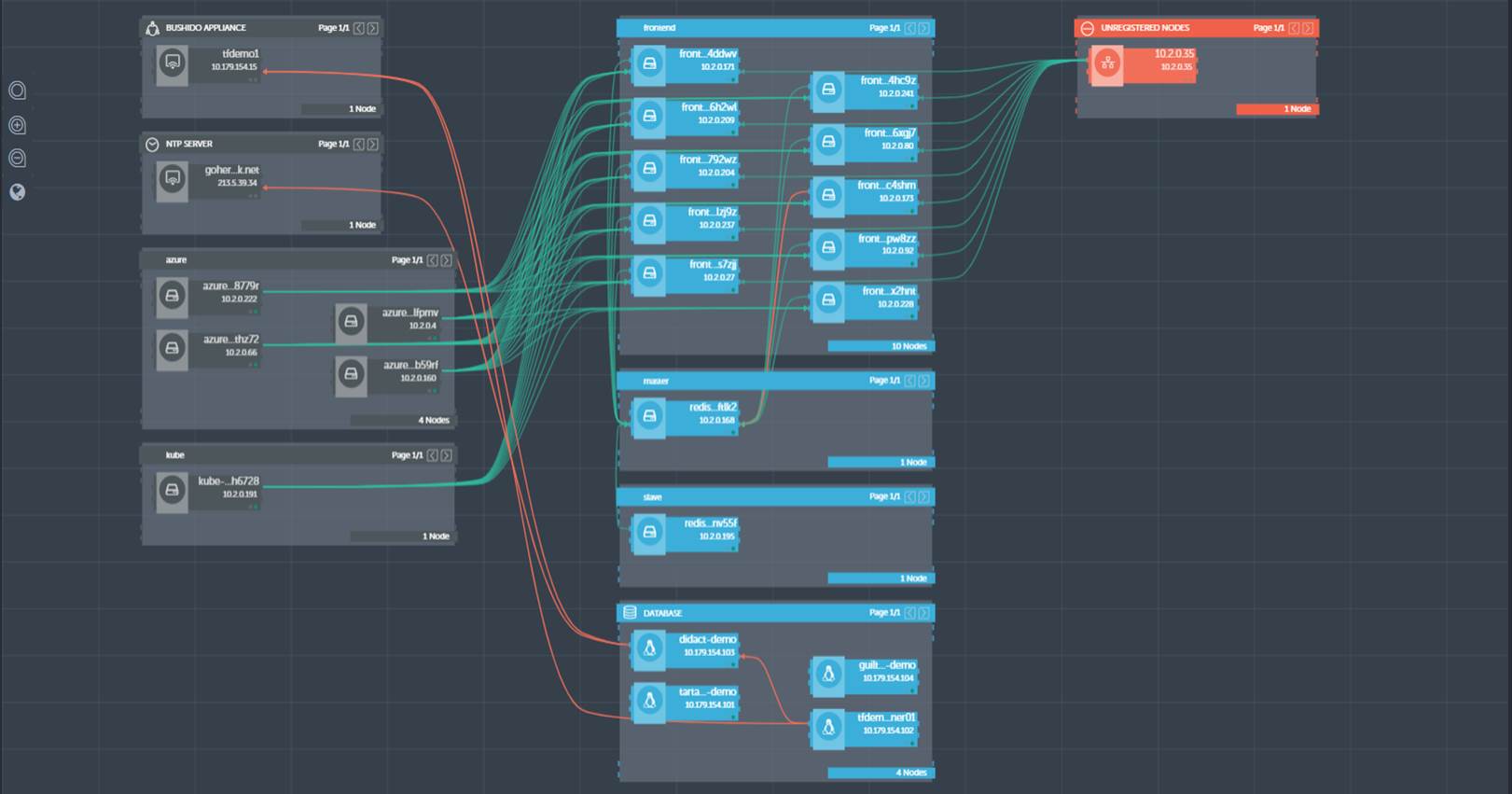
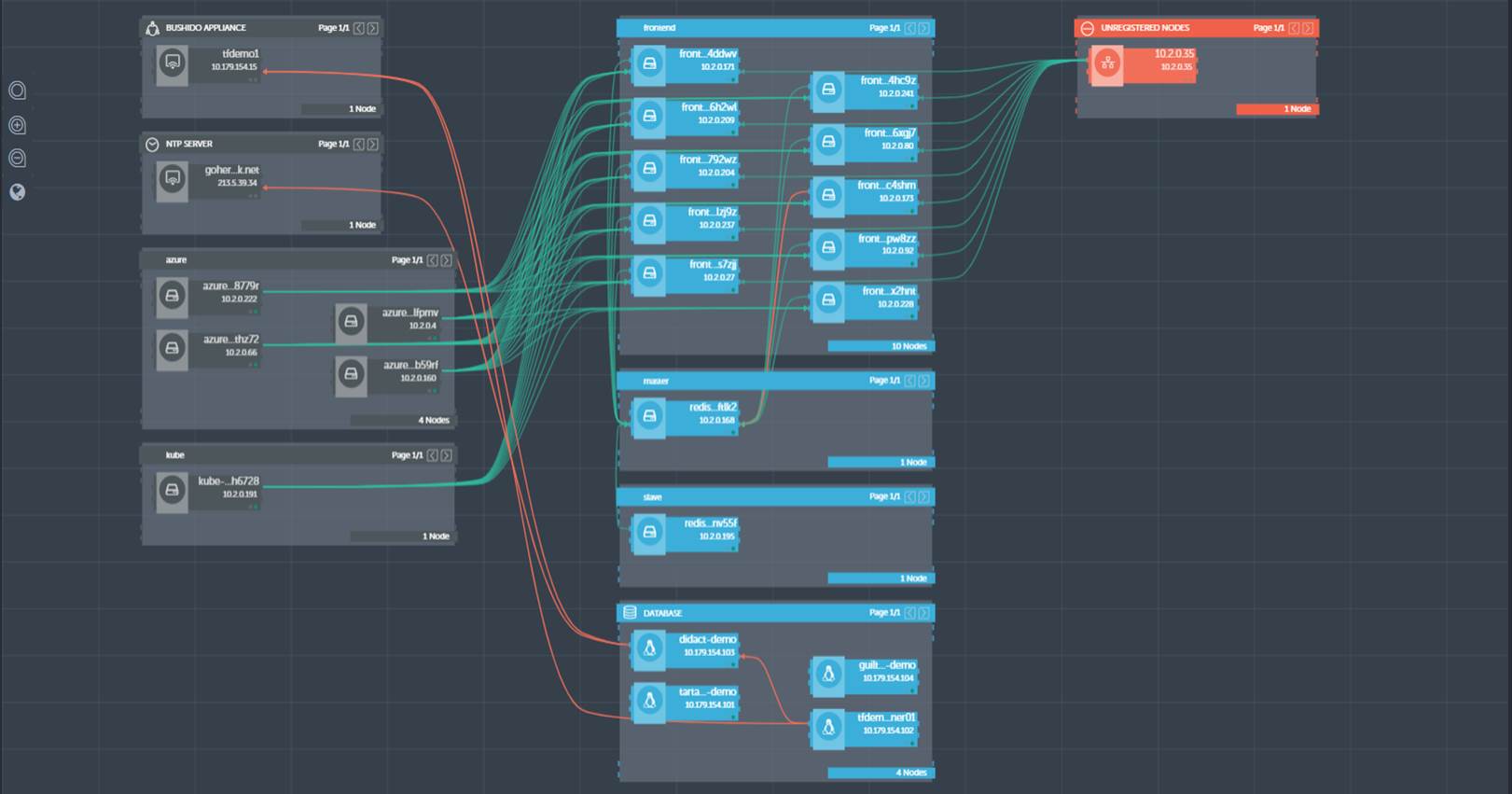
The application environment in modern enterprises is a collection of legacy, hybrid, and cloud applications with workloads distributed across virtual machines, containers, container orchestration platforms, cloud-native services, and legacy bare metal deployments. These environments are highly dynamic, in a constant state of change with a myriad of interdependencies, communication patterns and routines. This creates a complex ecosystem that exposes a host of attack vectors.
TrueFort has innovated a market-first approach to cloud workload protection that reverses the traditional model of securing applications at the infrastructure (server) and application (code vulnerability) layers. TrueFort Fortress provides true application-centric security, real-time visibility and advanced analytics that specifically address the complexities and dynamic nature of modern workloads across multi-cloud, hybrid and data centers. The platform applies deep and continuous analytics that not only identify threats, align and apply controls in real-time, but also adapt at machine speed to application and architecture changes, all while minimizing false positives.
Out of the box, TrueFort Fortress provides comprehensive, real-time cloud workload protection that covers all core server protection strategies including: (1) Hardening, configuration and vulnerability management; (2) Network firewalling, visibility and micro-segmentation; (3) System integrity monitoring and management; (4) Application control and allow listing; (5) Exploit prevention and protection; and (6) Server workload ADR (automatic deployment rule).
TrueFort Fortress provides consistent visibility and control for all workloads, regardless of location, including physical machines, virtual machines, containers and serverless workloads. It assesses system configuration, compliance, and vulnerability status and supports the creation of application control/allow-listing models in development, before the workloads are deployed into production. TrueFort Fortress can also secure applications and lockdown containers at runtime (supporting a zero trust model), and provides specific policy recommendations for workload hardening based on its role.
Using real-time analytics and machine intelligence, the Fortress platform automates monitoring, alerting and response to threats,
How we are different
- Full stack, integrated CWPP. TrueFort’s provides full-stack of cloud workload protection capabilities that are unavailable from any other product, including: patented behavioral analytics and policy automation; unique real-time telemetry and insight into the application environment; and flexible “bring-your-own agent” approach. This is why Fortune 500 companies in the financial, insurance, healthcare and other security-focused industries across the globe are adopting TrueFort Fortress for its unique application-centric approach to protect high-value cloud, hybrid, and legacy environments from hidden risks.
- Ability to leverage existing agents and telemetry. TrueFort supports an open ecosystem model that accepts telemetry data from existing third-party products to be processed by its advanced analytics engine. This allows customers to leverage existing investments in leading security and infrastructure vendors including CrowdStrike, Carbon Black, Cylance, Tanium, F5, Microsoft, VMware, Pivotal, Docker, ServiceNow, BMC Remedy, Splunk, QRadar and more. TrueFort Fortress is VMware Ready™ and is supported on VMware vSphere for production environments.
- DVR playback of suspicious activity. For post-breach forensics, TrueFort provides deep visibility for investigations, reducing IT effort and time. TrueFort focuses threat hunting, incident response and investigations and with on-demand playback of both real-time and historical data that can span minutes, months or even years – down to the process, network, identity and time levels. It allows security teams to dramatically improve accuracy and time-to-detection, response and compliance. TrueFort Fortress stops attacks that could otherwise be undetected for months or be identified only after data exposure. Whether deployed for SecOps or with DevOps for pre-production testing, TrueFort detects threats and microsegments against lateral attacks.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



