Vormetric Transparent Encryption (VTE) with Live Data Transformation (LDT)
Nominated in the Category:
Photo Gallery
|
Vormetric Transparent Encryption (VTE) with Live Data Transformation (LDT)
Additional Info
| Company | Thales eSecurity |
| Company size | 500 - 999 employees |
| Website | https://www.thalesesecurity.com/ |
NOMINATION HIGHLIGHTS
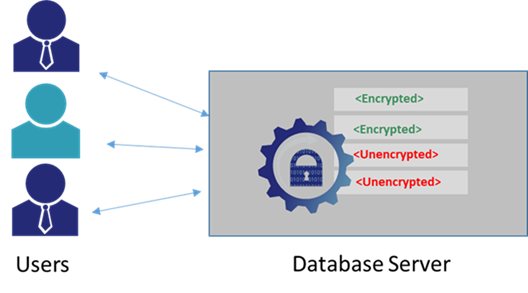
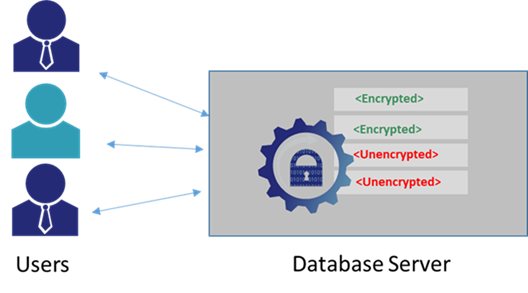
LDT delivers zero-downtime encryption. LDT is a patented technology that allows for databases from any vendor or file to be encrypted or re-keyed with a new encryption key while the data is in use by employees and customers. Therefore, it delivers the security and compliance of data encryption with key rotation without the need for planned downtime. For many organizations, this equates to tremendous yearly ROI because the applications aren’t taken offline to accommodate encryption and the on-going key rotation that many compliance programs require.
LDT was architected with IT operational simplicity top of mind: database backups run as normal, failure scenarios are accommodated, and CPU resources aren’t burdened. The solution automatically tracks versions of keys for backed-up files, failure scenarios are recovered without data corruption, and CPU cycles are proactively managed through scheduling. This assures that users are never slowed from doing their job and don’t call IT with complaints.
Since LDT is part of VTE, existing customers don’t have to deploy a new solution, they simply add the LDT license through centralized management to any server that wants to take advantage of zero-downtime encryption.
LDT is patented technology and is available for both Windows and Linux deployments that run on-premises and across multi-cloud environments including AWS, Azure, Google and private clouds. It works for any file types, traditional databases and Big Data environments. There is no other major data encryption provider that offers these capabilities.
The result of these capabilities is streamlined data security operations. For the business, it means remaining secure and compliant without customers experiencing downtime while encrypting or rekeying databases and without taxing the IT staff.
How we are different
1. Vormetric Transparent Encryption (VTE) is more than just encryption. Unlike competitors who offer Full Disk Encryption (FDE) or VM encryption, this solution also delivers privileged user access control and security intelligence logs. Cloud providers such as Rackspace, Centurylink, AT&T and many others offer VTE as part of their service. It also runs in AWS, Amazon, Azure and private cloud—always with centralized policy and FIPS 140-2 key management. Our largest competitor requires different management windows for each cloud provider.
2. Adding a license key to an existing VTE agent enables Live Data Transformation (LDT). LDT is a patented solution that enables encryption and regularly scheduled key rotation to meet stringent compliance requirements like PCI DSS and NIST 800-57 without taking data offline. Our competition offers file-level, FDE and VM encryption solutions that all require the data be inaccessible while it is being re-keyed. Planned downtime is very expensive because employees can’t use the data they need or customers can’t access systems that drive revenue. Thales customers typically see ROI with LDT in less than a year.
3. Perhaps, most important is the unique capabilities that assure IT can encrypt and re-key to keep the company safe and compliant without ever disrupting the business. No other encryption solution offers the same sophisticated error and failure handling to assure any network, server, or database failure doesn’t corrupt data. This capability is unprecedented in the industry, which is why LDT is deployed in the most demanding enterprise environments. Furthermore, only LDT offers a scheduling mechanism to vary CPU resources dedicated to encryption processes dependent on the time of day. This assures that performance Service Level Agreements (SLAs) are not put at risk by encryption tasks and additional CPU resources are made available to complete the encryption processes faster during off hours.


