Photo Gallery
 |

 |
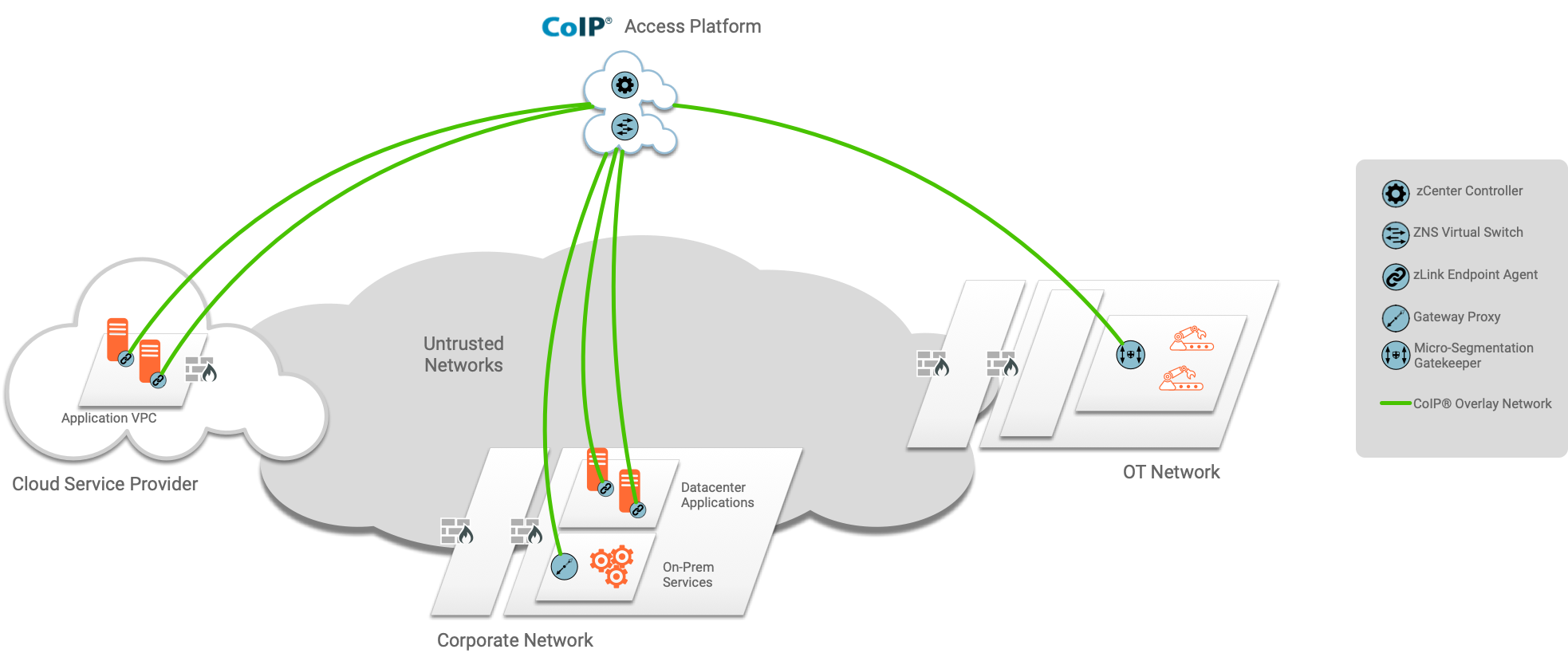
Zentera Systems' CoIP Access Platform


Additional Info
| Company | Zentera Systems, Inc. |
| Company size | 10 - 49 employees |
| Website | http://www.zentera.net |
NOMINATION HIGHLIGHTS
CoIP Access Platform is a strict implementation of the SASE model, in which security enforcement is pushed as close as possible to the application edge – ideally delivered through a software agent running on the endpoint operating system (agentless models are available for endpoints which require alternate onboarding models).
CoIP Access Platform enables users to be authenticated through standard identity providers, while endpoints and software processes are identified through fingerprinting and metadata. The agent then enforces policies that are stored on a centralized policy server (the zCenter orchestrator), applying security filtering on all traffic into and out of the server as defined by authorized policies. Applying security filtering at the endpoint eliminates the need for administrators to find ways to route traffic through fixed network security appliances, which is increasingly difficult to do in today’s complex hybrid and mobile environments – not to mention being inefficient in terms of application latency.
CoIP Access Platform supports the use of whitelist policy models that enforce default block actions. In this flow, all communication between protected servers is identified and authorized before each connection is made. This dramatically reduces the attack surface, while providing the administrator with a single pane of glass control to visualize and manage the security of all applications and endpoints.
How we are different
- CoIP Access Platform employs a Zero Touch deployment model. It builds an endpoint overlay network, allowing SASE to be deployed on top of any combination of existing vendor infrastructure (firewalls and routers).
- CoIP Access Platform provides a single pane of glass that allows SASE controls in any environment - on-prem or cloud - to be managed centrally, reducing operational silos.
- CoIP Access Platform provides a wide range of onboarding models, from software-based agents to the inline Micro-Segmentation Gatekeeper, enabling nearly any existing endpoint or application to be rapidly converted to SASE protection.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



