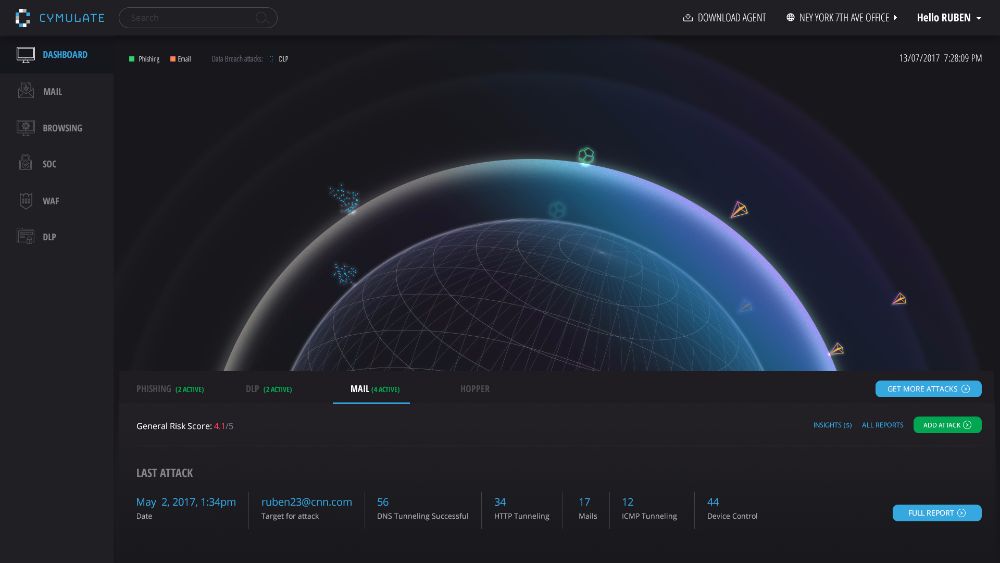
Cymulate – Breach & Attack Simulation Platform
Photo Gallery
 |
 |
Cymulate - Breach & Attack Simulation Platform

Additional Info
| Company | Cymulate - Breach & Attack Simulation |
| Website | http://www.cymulate.com |
| Company size (employees) | 10 to 49 |
| Type of solution | Cloud/SaaS |
Overview
Organizations now have the power to verify their security posture on-demand through a unique breach and attack simulation platform. Cymulate’s advanced technology allows them to launch simulations of cyber-attacks against themselves, immediately providing vulnerabilities and mitigation procedures to close each gap.
The centralized platform allows security testing through multiple attack vectors such as Email, Browsing, Internal Network (Lateral Movement), Human awareness, Data Exfiltration, WAF and SOC Simulation. Fully-automated and diversified attacks allow for complete security testing anytime, providing organizations with a better understanding of their security posture while continuously improving it. By eliminating false positive, Cymulate delivers only accurate and actionable results.
Organizations may relax into a false sense of safety after integrating security solutions and beefing up its infrastructure. Cymulate measures a company’s true preparedness to handle cybersecurity threats effectively. Using offensive approach and defensive actions, Cymulate exposes critical vulnerabilities by simulating multi-vector cyberattacks from an attacker’s perspective, before an actual attacker has a chance to exploit any weaknesses. Cymulate testing is simple to perform on demand, anytime and anywhere, without impacting the users or infrastructure. While most cyber security solutions are notoriously hard to implement, Cymulate’s plug-and-play platform is much simpler to deploy, even for non-technical users.
Key Benefits:
o Mitigate attacks before they happen
o Get a comprehensive assessment
o Remote test your entire infrastructure
o Plug & Play Solution
o SaaS based – No Hardware required
o Immediate results: 24/7
How we are different
1. Cymulate validate wider attack vectors: Email, Browsing, Internal network, Data exfiltration, Human, WAF and SOC.
2. Cymulate also validate the effectiveness of the organization security controls.
3. Cymulate platform is the easiest to deploy, allows you to perform your first assessment within minutes and does not require implementation or hardware



