Photo Gallery
 |

 |
iboss

Additional Info
| Company | iboss |
| Company size | 100 - 499 employees |
| World Region | North America |
| Website | https://www.iboss.com/ |
NOMINATION HIGHLIGHTS
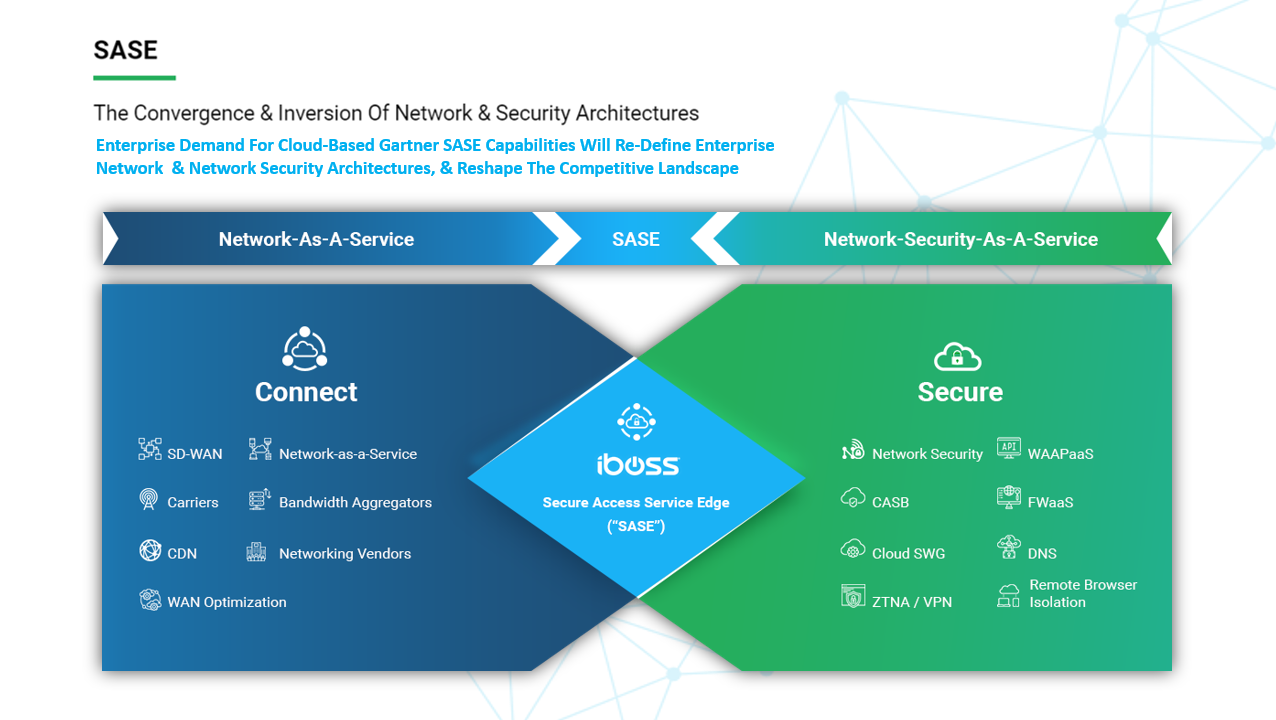
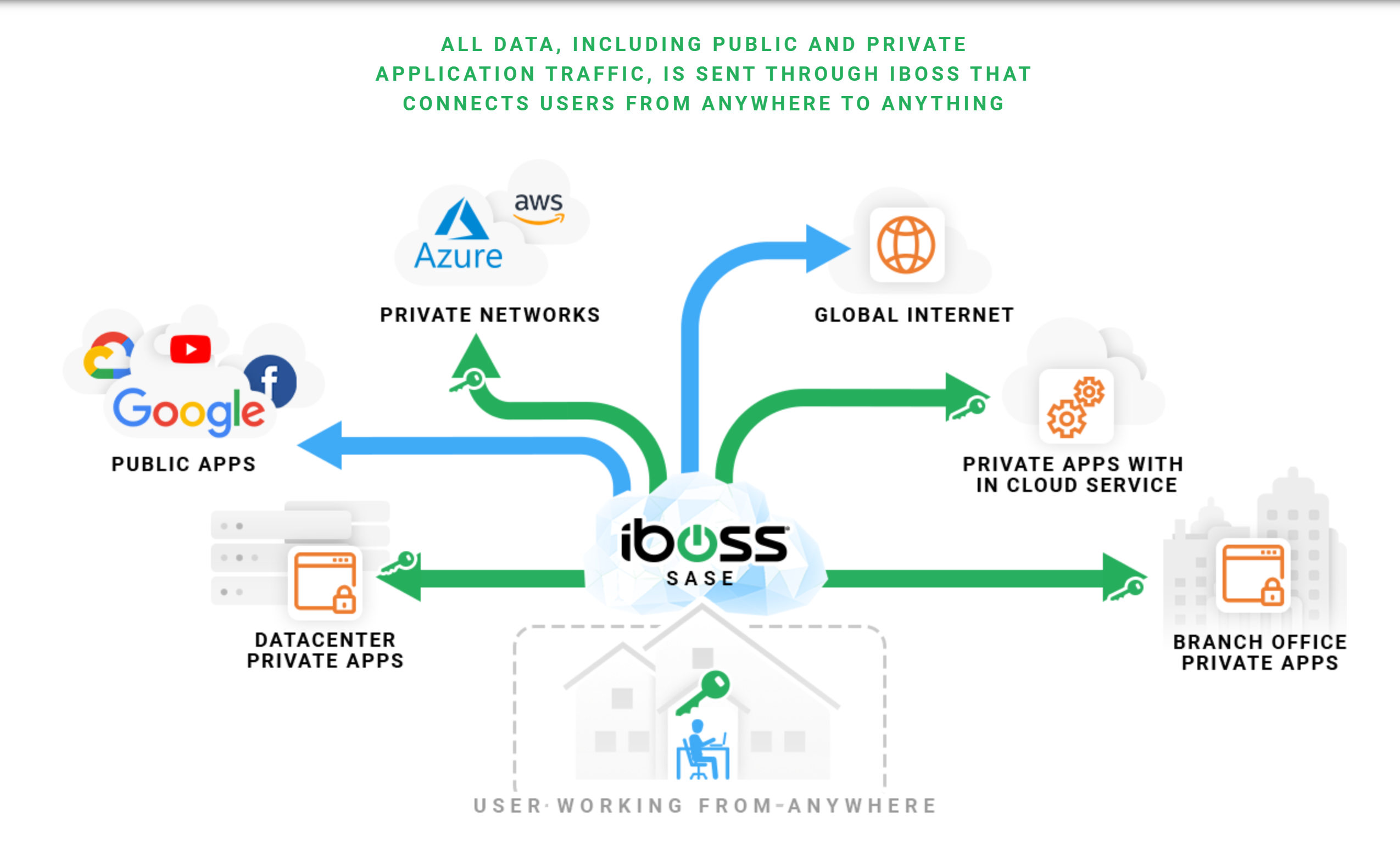
A Secure Access Service Edge, or SASE platform, ensures that any connection originating from a user or device to any destination in the cloud is secure and meets the organization’s connectivity requirements. However, with software and internet company regulations and security risks associated with SaaS cloud delivered platforms, leveraging a SASE platform for secure connectivity can be a challenge.
The iboss platform is the leading SASE platform that is architecturally based on containerization. Containerization allows iboss to deliver secure connectivity for users anywhere while maintaining a completely isolated and controlled network data path. In addition, a fully containerized architecture allows for natural hybrid deployments where proxy and firewall security features can be delivered within an organization’s private network, while leveraging the cloud based service, if needed, for remote users or branch offices.
Understanding containerization is the key for software and internet companies in need of a highly secure SASE service. With a containerized service like iboss, the network connections from devices and users are processed within isolated containerized gateways which perform proxy and firewall functions. The containerized gateways never process data for any other organization and data is never mixed with that of any other customer. Containerized gateways are destroyed and created in seconds providing horizontal scaling and a global SASE fabric.
With alternative SASE platforms that lack containerization, network traffic from multiple organizations are processed within the same gateways that proxy, decrypt and firewall data for other organizations. Mixing data within the gateways that perform functions like decryption not only results in latency but increases security risks. The largest organizations of the world have quickly migrated to iboss for cloud security as part of their cloud transformation strategy.
How we are different
With network perimeters disappearing, the need to secure users wherever they roam is critical. The iboss cloud lives in the cloud and can secure users regardless of location.
*With applications moving to the cloud, the need to access those applications securely from anywhere is critical. The iboss cloud follows users to ensure they have secure connections at all times and can access cloud applications with high speeds.
*Bandwidth and encrypted traffic is increasing by the day causing enormous strain on traditional network security appliances. The iboss cloud runs in the cloud and can inspect and secure any volume of traffic while eliminating infrastructure resulting in big savings and reducing IT strain from managing appliances.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



