Photo Gallery
|
|
Manufacturing, Cybellum, The Product Security Platform
Additional Info
| Company | Cybellum |
| Company size | 100 - 499 employees |
| World Region | Middle East |
| Website | http://www.cybellum.com |
NOMINATION HIGHLIGHTS
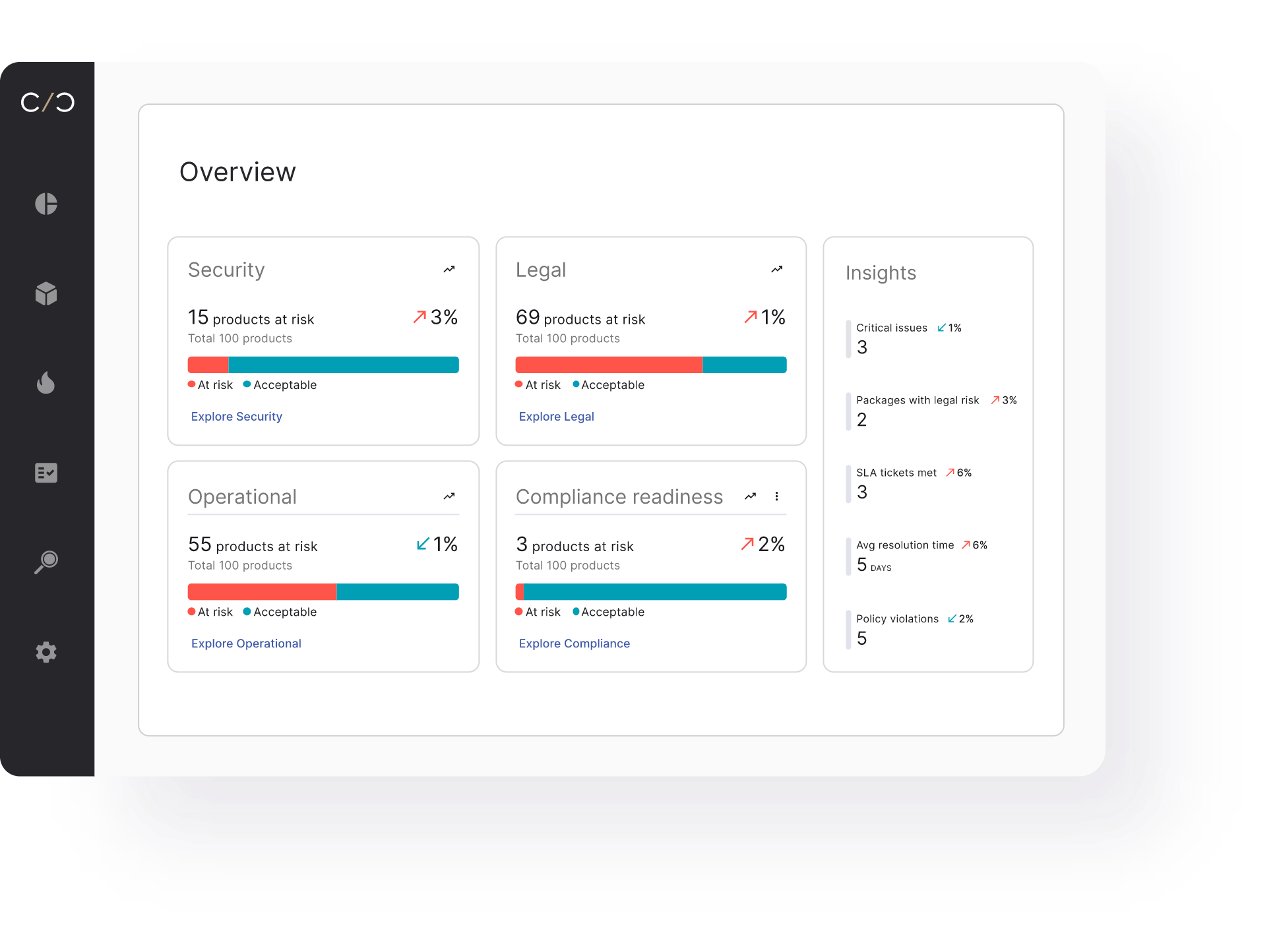
Cybellum’s product security platform is all about enabling teams to secure devices and products while complying with ever growing regulations.
With an extensive platform to match the needs of specific industries and the individual needs of their products, managers and their teams can rely on dashboards, live vulnerability updates, SBOM-based security approaches, and automating compliance report generation. Simply put, they can generate, manage and validate SBOMs, detect and prioritize vulnerabilities, comply with regulations and manage incident response. All from one place.
Once SBOMs are generated automatically, it opens a world of proactive opportunity for product security teams to utilize all of the Product Security platforms capabilities, such as:
– SBOM Management
– VEX Reporting
– Vulnerability Management
– PSIRT
– Product licensing
– And more
When teams use Cybellum, they are choosing to secure their vehicles, medical devices, and industrial equipment that all have to operate securely, no matter what.
How we are different
Cybellum is the only security tool focused on full management of connected products.
As opposed to working with various tools with limited integration, Cybellum provides a comprehensive Product Security Platform that focuses on the needs of managers and teams who are tasked with keeping devices and products secure in compliance with growing regulations.
- Complete product-specific risk coverage- Automatically detect, prioritize and mitigate software vulnerabilities, zero-days, malware, and security gaps throughout the product development lifecycle.
- Compliance validation for your industry- Ensure industry regulations, standards, and your own security and licensing policies are validated and enforced
- Customizable policies to your internal needs- Designed to fit specific industries, our default settings or configure Cybellum with your risk scoring logic, thresholds, security policies, automated workflows and more.
As our competitors offer similar bits and pieces of what we do, we are the only ones to offer it all, within one application– allowing teams to focus on security, not combining data from various non-synchronized applications.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

