Photo Gallery
 |

 |
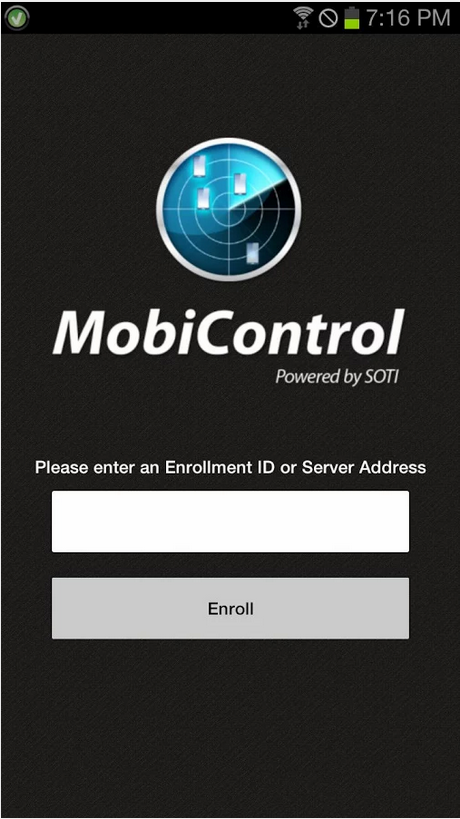
SOTI MobiControl 13.0

NOMINATION HIGHLIGHTS
With more workers outside the traditional office and the proliferation of mobile devices, mobile security has become a cyber security concern for businesses. SOTI has been delivering security and management solutions for mobile devices for more than 15 years, with thousands of companies worldwide depending on SOTI MobiControl.
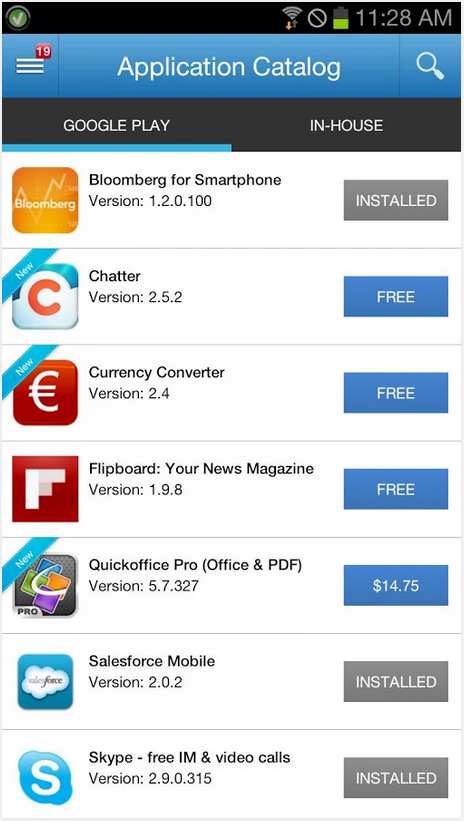
SOTI’s MobiControl is an end-to-end enterprise mobility management (EMM) solution that securely manages mobile devices, applications, and content. Its advanced security features − physical, network, data and device security − enable businesses to ensure that on-device data remains private and secure. SOTI MobiControl deserves recognition for the following reasons:
• SOTI MobiControl adapts to new security threats before they become a problem, detecting suspicious new directories and files and alerting IT administrators to compromised devices. The solution employs device authentication, data encryption and certificate management to prevent unauthorized device use and data loss.
• SOTI MobiControl supports containerization to assure regulatory compliance and to prevent the misuse of valuable company assets. By creating a “secure container” − an encrypted area of users’ mobile devices that separates corporate information and applications from personal ones − IT teams can remotely wipe corporate content from devices as well as push updates and transmit information securely to employee devices. And because malicious apps are often used by hackers to gain access to a device’s data through malware and spyware, SOTI MobiControl can restrict the use of applications in the “secure container” of corporate devices.
• Physical security is an important part of a business’ mobile device policy, especially since lost or stolen phone or other mobile devices can enable intruders to access corporate networks, apps or content. SOTI MobiControl can track lost or stolen devices, lock down the device or restrict employee access to company data, and can shut devices down or remote-wipe them in the field.

Vote by Sharing
- Like
- Digg
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- SMS
- Viber
- Telegram
- Subscribe
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Each completed social share counts as a vote for this award nomination.



