Photo Gallery
|

|
Mobile Threat Protection
Additional Info
| Company | Zimperium, Inc. |
| Company size | 50 - 99 employees |
| Website | http://www.zimperium.com |
NOMINATION HIGHLIGHTS
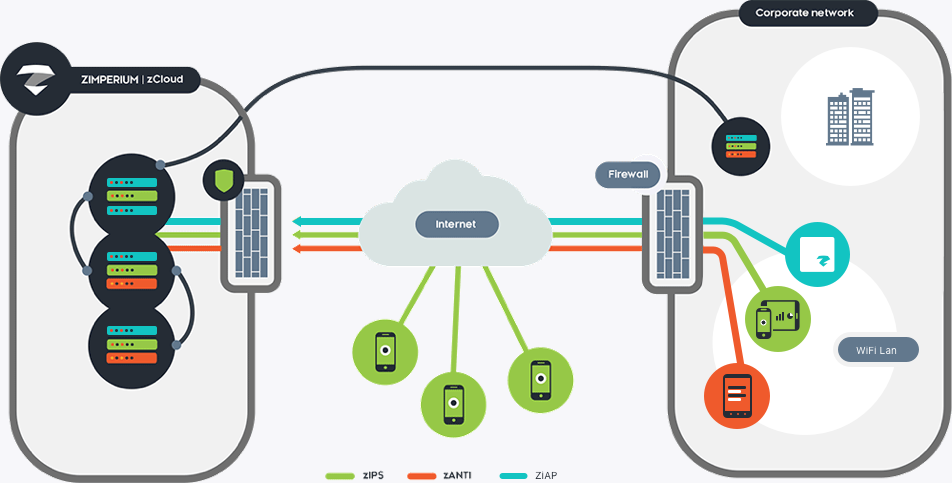
Zimperium Mobile Threat Protection is the industry’s first and only on-device mobile threat detection platform delivering continuous and real-time cyberthreat protection for mobile devices and applications. Powered by its z9 detection engine and patented machine-learning models developed and refined over four years of threat intelligence research, Zimperium dynamically and accurately identifies malicious known and detects zero-day attacks. By analyzing slight deviations to the mobile device’s operating system’s statistics, memory, CPU and other system parameters, Zimperium accurately identifies not only the specific type of malicious attack, but also provides forensics associated with the who, what, where, when, and how of a threat event. Businesses can easily enable existing mobile devices into powerful mobile cyber threat sensors. Adding sensors to a company’s mobile devices to detect attacks increases the chances an intrusion via mobile will be detected and provides data on how to defend itself from future attacks.
Unlike other solutions that may tunnel data to the cloud for analysis, Zimperium isn’t reliant on an Internet connection. Not relying on an internet connection provides a better user experience so not to introduce latency or invade privacy. Zimperium’s comprehensive offering detects all mobile attack vectors whether via operating system vulnerabilities, applications or communication networks.
With more business being conducted outside of the office and on Wi-Fi or cellular networks than ever before, the risk of a targeted mobile cyberattack significantly increases. One compromised mobile device can result in a security breach, compromising an organization’s data, assets and brand. Investing in security products decreases the chances a catastrophic breach will occur. Zimperium provides proprietary technology to detect known and unknown attacks.
How we are different
-- The majority of containerization and EMM solutions in the enterprise are inadequate as they solely focus on regulating employee behavior. This is where Zimperium comes in and fills the gap. Through sophisticated and machine-learning techniques, Zimperium is able to properly assess risk and perform on-device detection of threats, and, as a result, provides the greatest possible coverage and requires no private user information leave the device. Zimperium partners with leading mobile management and containerization vendors to provide pre-built integrations.
-- Built on scalable, multi-tenant architecture, Zimperium can handle hundreds of thousands of devices for any single enterprise. It flexes to accommodate any number of customers. For data-at-rest and in-transit, AES 256-bit encryption is strictly enforced. Security teams see only the detailed information specific to their enterprise, although they benefit from the knowledge of other threats that Zimperium has discovered at other customer companies.
-- Zimperium’s dedicated and world-renowned research team, zLabs, puts itself in the hacker mindset to discover new mobile vulnerabilities and develop solutions to fix the security flaws. This research is applied to Zimperium's technology, ensuring that its customers are protected from even the most advanced mobile threats.

Community Choice Award Voting
Help This Nominee Win
Cast your vote by sharing this nominee’s profile on LinkedIn, Facebook, or X, using the buttons above. Each completed social share adds one Community Choice vote.
Voting closes July 18, 2026. Community Choice winners will be announced before Black Hat USA.
What is the Community Choice Award? →
The Community Choice Award is separate from the judged Cybersecurity Excellence Awards. It is determined entirely by public voting, so nominees can receive both jury recognition and Community Choice recognition.

