Zentera Systems’ Zentera Secure Access (ZSA)
Photo Gallery
 |

 |
Zentera Systems' Zentera Secure Access (ZSA)


Additional Info
| Company | Zentera Systems, Inc. |
| Website | http://www.zentera.net |
| Company size (employees) | 10 to 49 |
| Type of solution | Software |
Overview
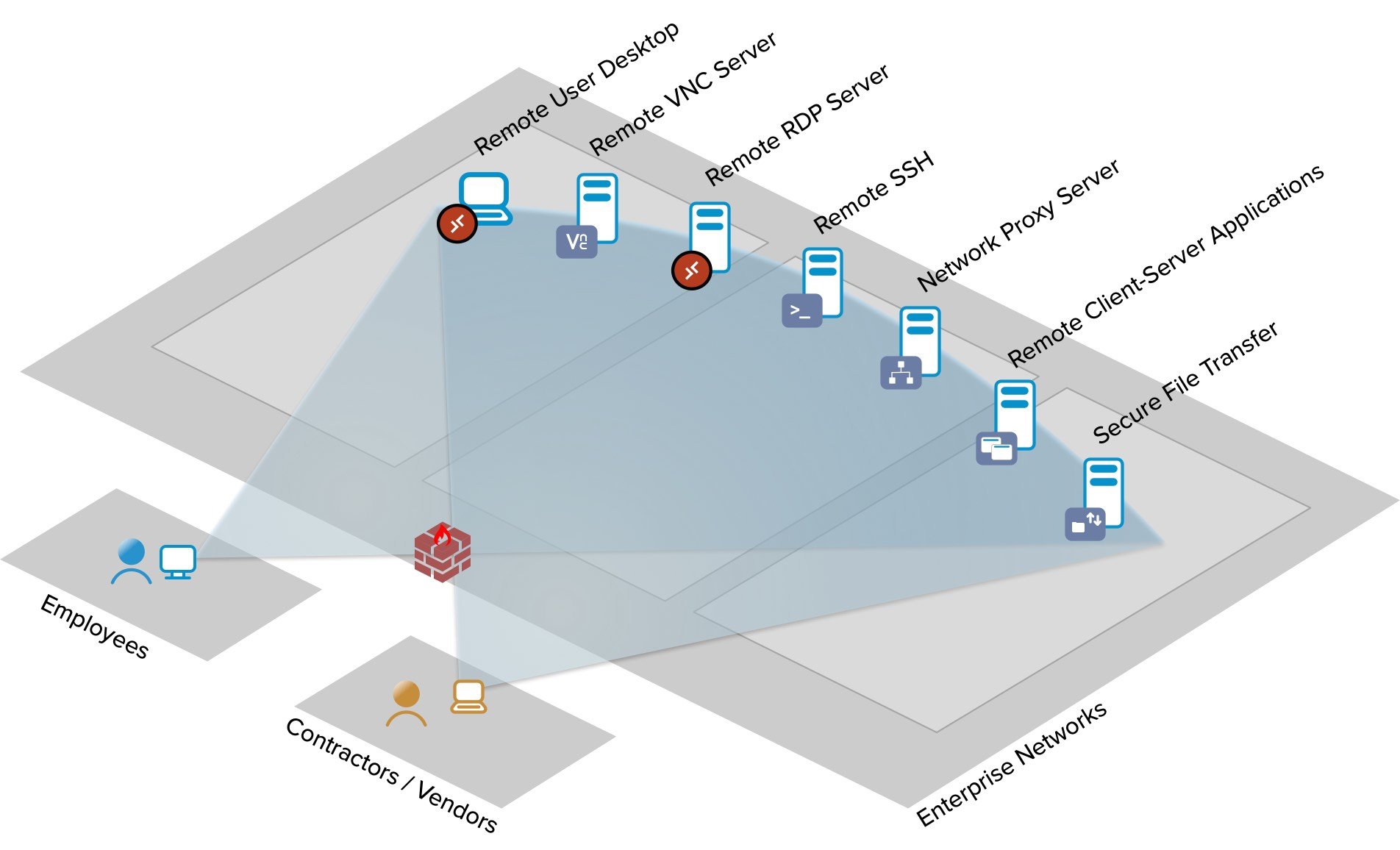
Zentera Secure Access (ZSA) is a privileged access platform that uses the principles of Zero Trust and SASE to dramatically simplify the process of configuring and managing privileged access. By identifying users, endpoints, and applications, administrators are able to create directed access to specific applications running on specific servers for users, based on roles and responsibilities, without providing them VPN access to the entire corporate network.
Current solutions are built on a patchwork of technologies: mobile device management to establish trust, VPNs to encrypt traffic, and UTM firewalls to filter out any unauthorized traffic. Deploying and managing user access requires wrangling a tangled web of policies, operated by separate teams. This approach requires constant tuning and upkeep to stay in step with increasingly mobile users and applications, and fails to cope with ever-increasing cybersecurity threats.
ZSA provides granular access for privileged users, who are identified using the customer’s existing identity provider. Without granting network level access, creating a VPN connection or opening a firewall, ZSA enables remote access, with built-in support for remote terminals, including VNC and RDP, as well as ssh, git, and any standard TCP/IP application.
Enabling remote access without opening the firewall significantly improves security. For example, ZSA can enable users to connect using Microsoft RDP without opening port 3389 to inbound traffic at the firewall, rendering that port inaccessible to unauthenticated users or client software.
End-to-end access control policies can be configured, managed and enforced centrally. Reducing the number of control knobs in the infrastructure significantly streamlines setup, reduces error-prone change requests, and minimizes troubleshooting effort.
ZSA also provides access logs, enabling auditing of user access to corporate resources for compliance initiatives or to inform digital forensics.
Customers have used ZSA to provide secure remote access for remote workers, 3rd parties, and securing access to OT environments.
How we are different
- Centralized policy management for end-to-end access control and visibility, with different levels of access based on user roles and responsibilities.
- Overlay-based Zero Touch deployment model, which works on top of existing network and security infrastructure, without reconfiguration.
- Directs authenticated user accesses to land on specific resources deployed deep inside enterprise environments. Unlike a VPN, which provides users the ability to connect to the entire network, our patented application proxy network, micro-segmentation. and centralized policy engine prevent users from connecting to any system beyond their privileges.



