Behavior
Photo Gallery
 |
 |
Behavior
Additional Info
| Company | Expanse |
| Website | https://www.expanse.co/ |
| Company size (employees) | 100 to 499 |
| Type of solution | Service |
Overview
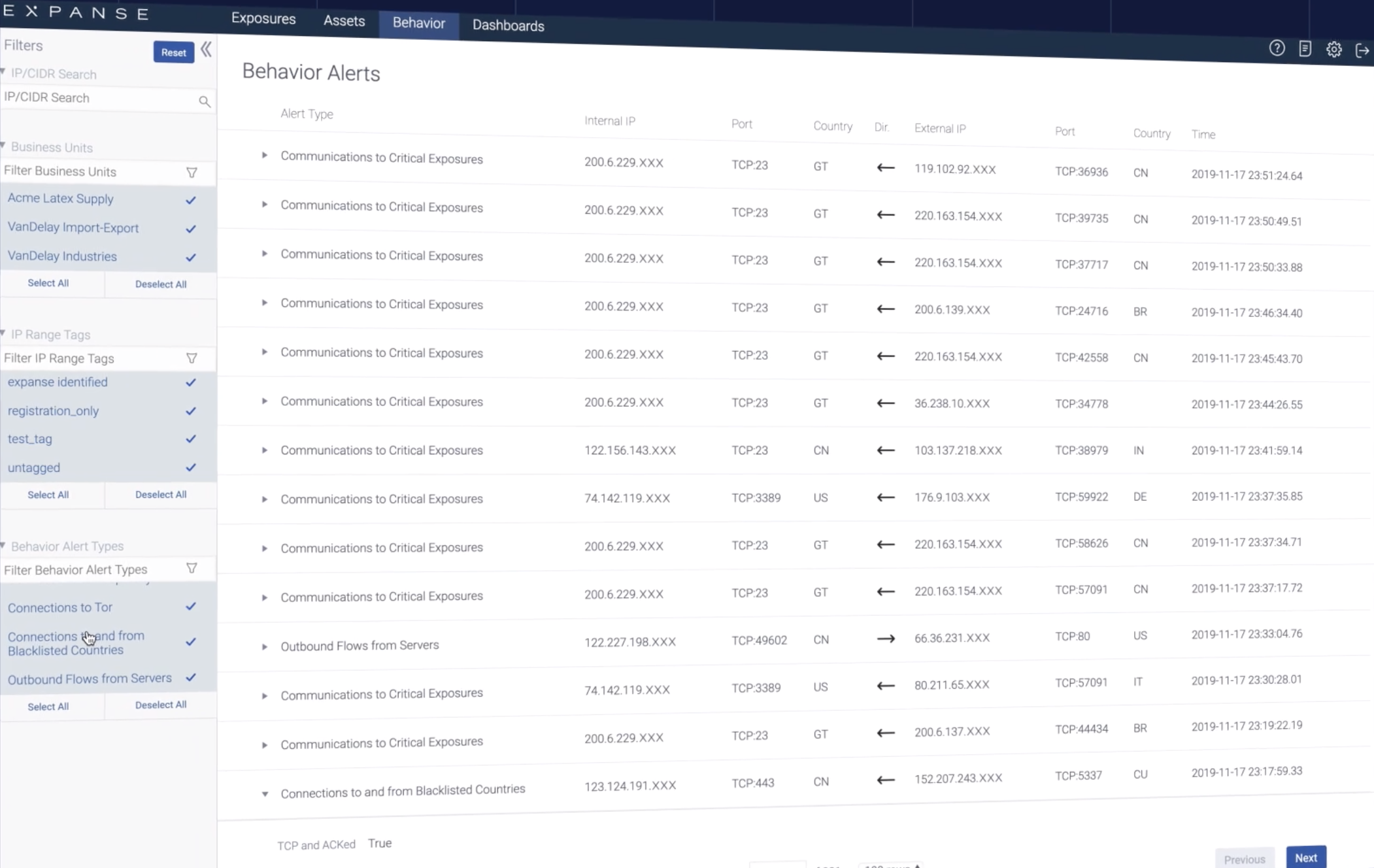
Behavior discovers, tracks, and notifies companies of risky and policy-violating activity from their network, all without agents or instrumentation. Using global netflow data from Tier 1 ISPs, Behavior surfaces communications between a company’s Internet Assets and others based on actual observed communication. This perspective removes the traditional challenges of traffic monitoring without the need for installation of agents or configuration of monitoring tools. The result is an accurate way to detect and stop risky and out-of-policy communications.
How we are different
● There is no other product on the market like Behavior that surfaces risky communications that can be indicators of a threat through sampling global netflow data. Most organizations focus their network defenses on deploying firewalls and endpoint protection tools. Behavior, however, takes an outside-in view to discover risky communications and give organizations valuable details on those communications so that they can quickly identify and eliminate a variety of threats originating from the Internet. Behavior does not require the deployment of any agents or sensors.
● Risky or out-of-policy communications may be related to a breach or be an indicator of poor management that could expose an asset to future threats. Behavior is an invaluable tool for security and incident response teams and provides a one-of-a-kind ability to surface these risky communications and guide first steps to drive remediation.
● Apart from preventing security breaches that can be financially costly and result in business interruption or damage to brand reputation, Behavior also helps organizations ensure that they are remaining compliant with regulations. In this way, Behavior prevents organizations from being hit with costly fines for falling out of compliance.



