Core Impact
Photo Gallery
 |

 |
Core Impact

Additional Info
| Company | Core Security by HelpSystems |
| Website | http://www.helpsystems.com |
| Company size (employees) | 1,000 to 4,999 |
| Type of solution | Software |
Overview
Core Impact is a powerful penetration testing platform that safely and efficiently replicates attacks and uncovers security weaknesses. Organizations can maximize their resources with certified exploits and guided automations, providing valuable insights that will help mitigate risk and protect essential assets.
Core Impact is designed to enable security teams to conduct advanced penetration tests with ease, allowing you to safely test your environment using the same techniques as today’s attackers. Users can efficiently execute common tasks, saving time while providing a consistent, repeatable process for their testing infrastructure. Additionally, Core Impact allows you to quickly re-test exploited systems to verify that remediation measures or compensating controls are effective and working.
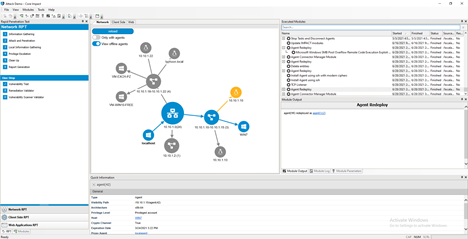
Accurately identify and target internal information systems for network penetration testing. Core Impact can help exploit vulnerabilities in critical networks, systems, hosts, and devices by imitating an attacker’s methods of access and manipulating data, as well as testing defensive technologies’ ability to stop attacks. Users can gain further insights with Core Impact’s attack map, a network graph that illustrates a real-time overview of attack chains, pivoting and any other activities completed during testing. Run web application penetration tests to find weaknesses through detailed web crawling, pivoting attacks to web servers, associated databases, and backend networks to confirm exploitability.
Easily deploy phishing campaigns for client-side social engineering tests to discover which users are susceptible and what credentials can be harvested. Use the step-by-step process to create emails, select targets, and choose between browser redirects or web page clones. Challenge users with more sophisticated, tailored spear-phishing emails that are harder to identify as fake. Actual emails can be imported from mail clients to increase the authenticity of the attack.
Core Impact provides an easy to follow and established automated framework that can support industry requirements and standards, including PCI-DSS, CMMC, GDPR, and NIST.
How we are different
Core Impact includes an up-to-date library of commercial-grade exploits to reveal how chains of exploitable vulnerabilities open paths to mission-critical systems and assets.
Core Impact's automated Rapid Penetration Tests (RPTs) help optimize the use of your security resources by simplifying processes, maximizing efficiency, and enabling pen testers to focus on more complex issues.
Provides multi-vector testing capabilities with the ability to replicate attacks across network infrastructure, endpoints, web, and applications.



