Photo Gallery
|
FireEye Email Security
Additional Info
| Company | FireEye |
| Company size | 1,000 - 4,999 employees |
| Website | http://www.fireeye.com |
NOMINATION HIGHLIGHTS
More than 91% of cybercrime begins with an email – and employees receive ~200 emails daily. Paired with the prominence of social engineering attacks – including the use of malicious URLs using HTTPS, phishing attempts, new impersonation techniques, and cloud-based attacks focused on file-sharing services – the growing danger of making that one wrong click is very real.
Email is a favorite attack vector for distributing malware. Bad actors are continually adapting their techniques to improve their ROI. In the past year, FireEye has observed a shift from malicious attachments or code to malware-less scams like spear phishing emails wrapped in impersonation packages.
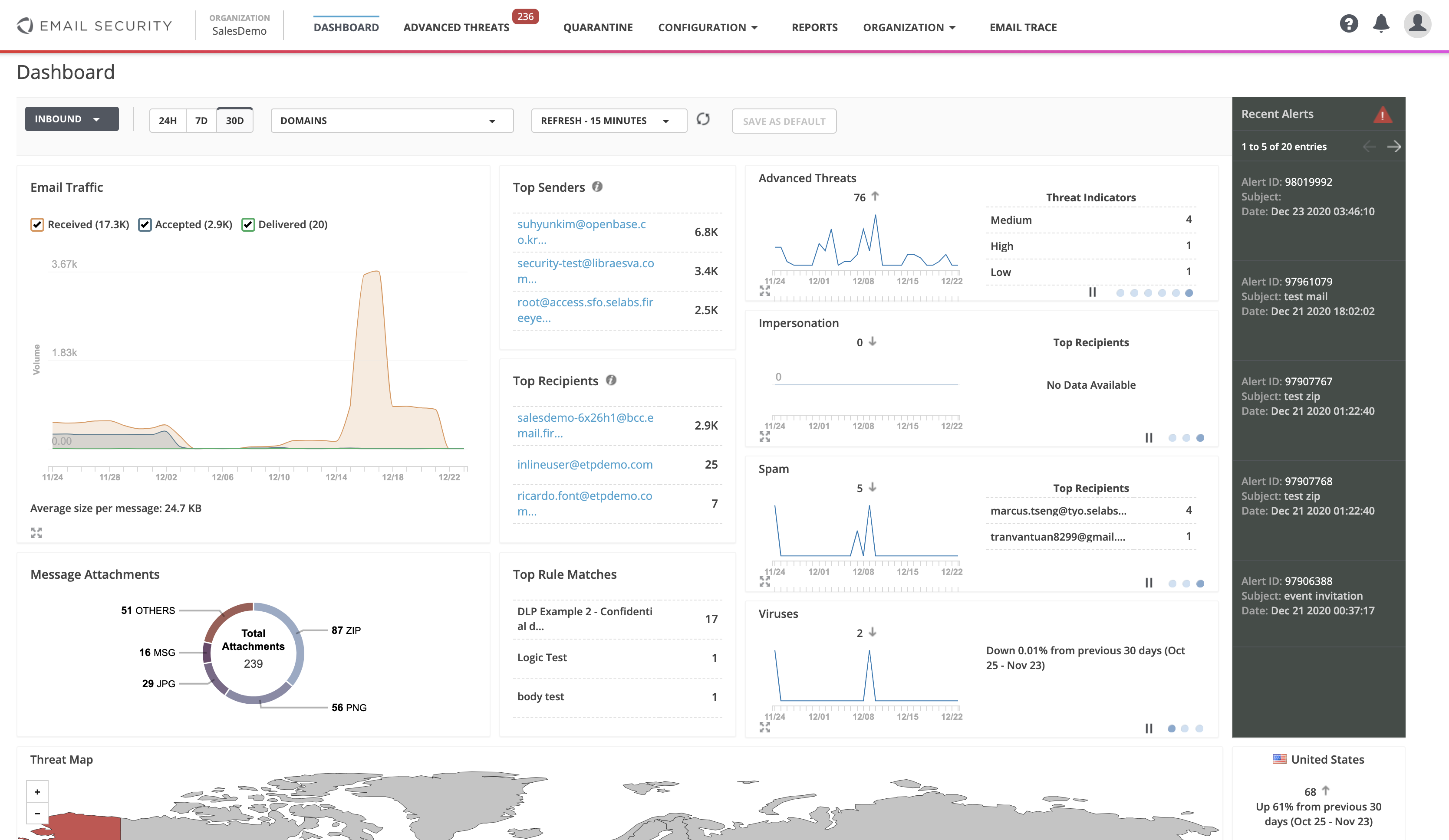
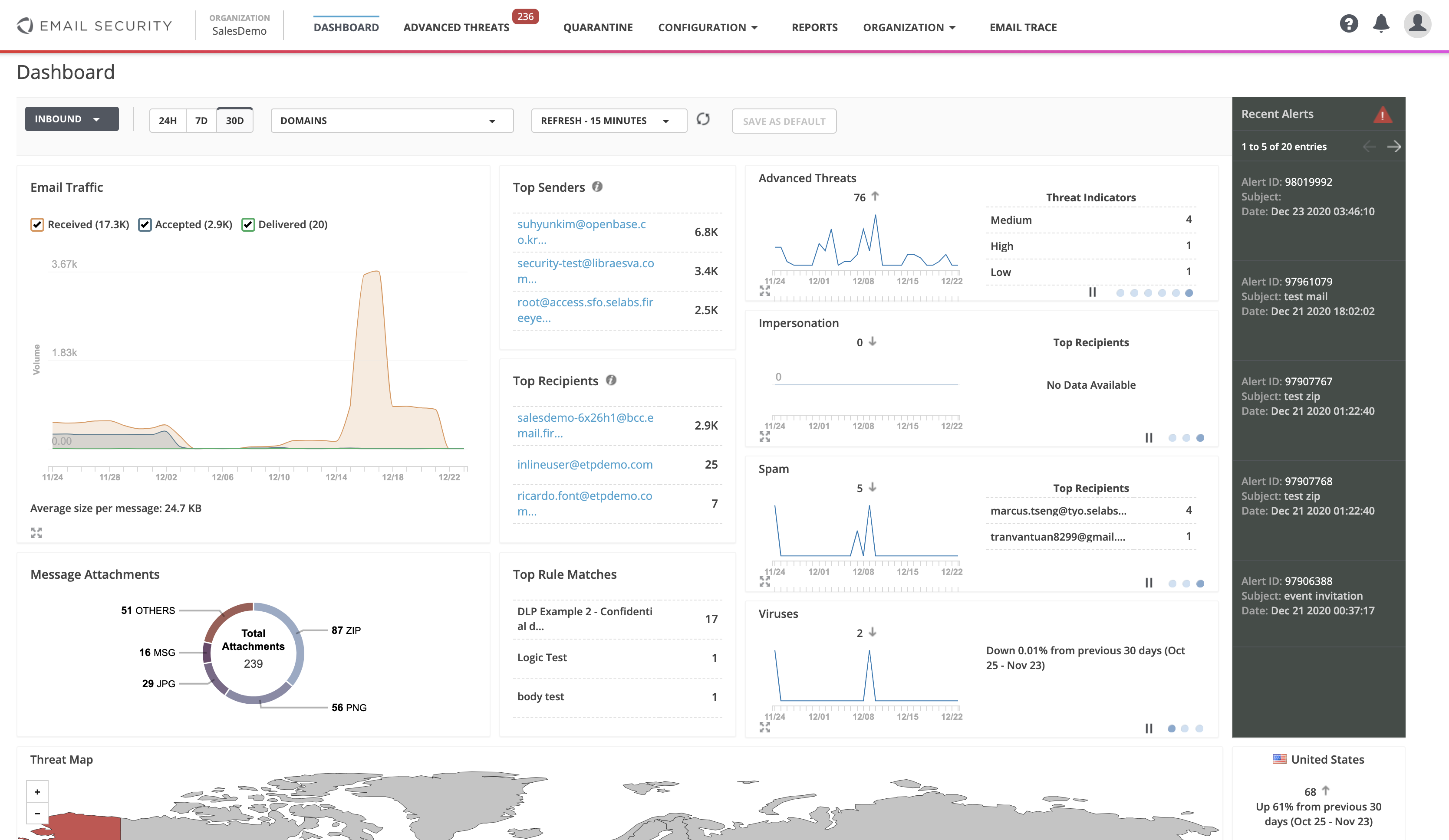
FireEye Email Security counters both breeds of threats. It not only blocks attachments weaponized with malware, but it also seeks and destroys fraudulent wire transfer requests, URL links to credential phishing sites, and other social engineering and impersonation techniques. Whatever the malicious tactic is, FireEye is quick to identify it and block it by leveraging first-hand intel on attacks and adversaries.
Frontline insights help us keep FireEye Email Security in lockstep with attackers, stopping threats with first-hand knowledge of attacks/attackers before they become more serious incidents – blocking not only malware and suspicious URLs, but also phishing and impersonation techniques.
FireEye Email Security is a full Secure Email Gateway. FireEye Email Security offers customers a strong defense through our attachment detonation, malicious URL discovery and impersonation detection. It’s differentiated from competitors because it provides advanced threat protection for outbound messages as well as inbound messages. It also provides custom YARA rules for both inbound and outbound messages.
FireEye Email Security’s high detection efficacy and low false positive rate minimizes organization’s operational costs. And with inline deployment, its ability to spot threats early, minimizes potential damage from incidents. This results in annual operating expense savings.
How we are different
• All corporations use email and need to safeguard sensitive company data. FireEye Email Security blocks threats before they become incidents, surfacing critical threats with intelligence from our ecosystem. This reduces business risk, simultaneously saving operational costs and protecting brand and reputation. Over-taxed security teams aren’t wasting time investigating spurious alerts. Thinly stretched teams can’t chase false positives. FireEye Email Security identifies true positive alerts in just four minutes. Investing in FireEye Email Security far outweighs the business impact of an email-borne breach.
• Unrivaled threat intelligence underpins the FireEye email product offering. We collect extensive threat intelligence on the frontlines and draws on this evidence and context to drive forward detection capabilities within our products. FireEye sees more evil than anyone else as we integrate the frontline knowledge of our incident response and managed defense teams to ensure our products do what matters most – protect against the latest breaches – whether in the cloud or on-prem.
• Attackers are constantly adapting their tactics to get past email security defenses. FireEye Email Security continues to address these landscape changes to detect the malicious emails that get past other services. Our high detection efficacy, combined with a low false positive rate, minimizes operational costs and aids early prevention of serious incidents, resulting in annual operating expense savings with inline deployment. New capabilities to help address customer business and technical needs are also rolled out as part of monthly releases, ensuring the product stays current as the threat landscape evolves. This includes deep relationship analysis, expanding the use of machine learning, and automating tools.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

