Photo Gallery
|
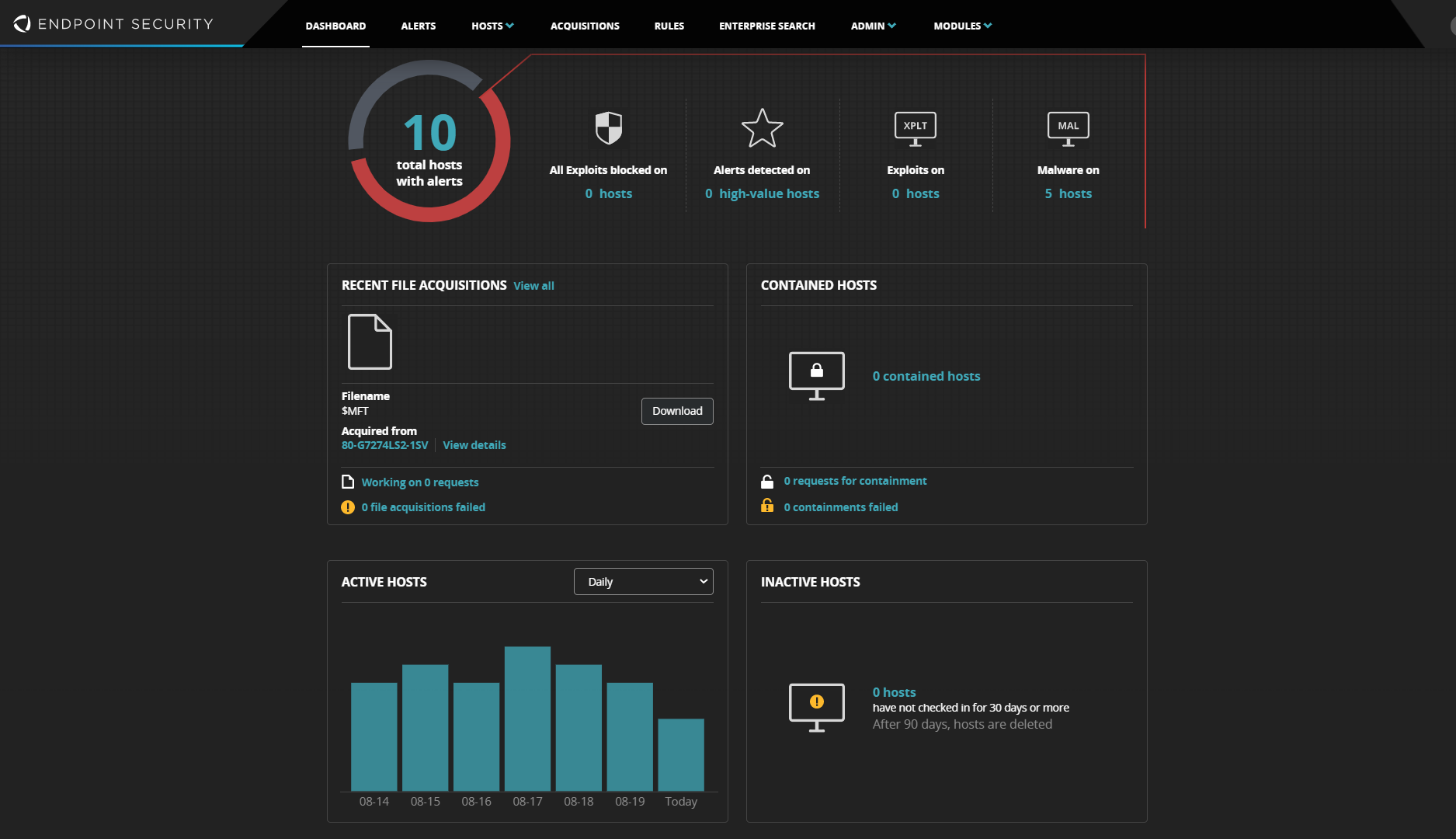
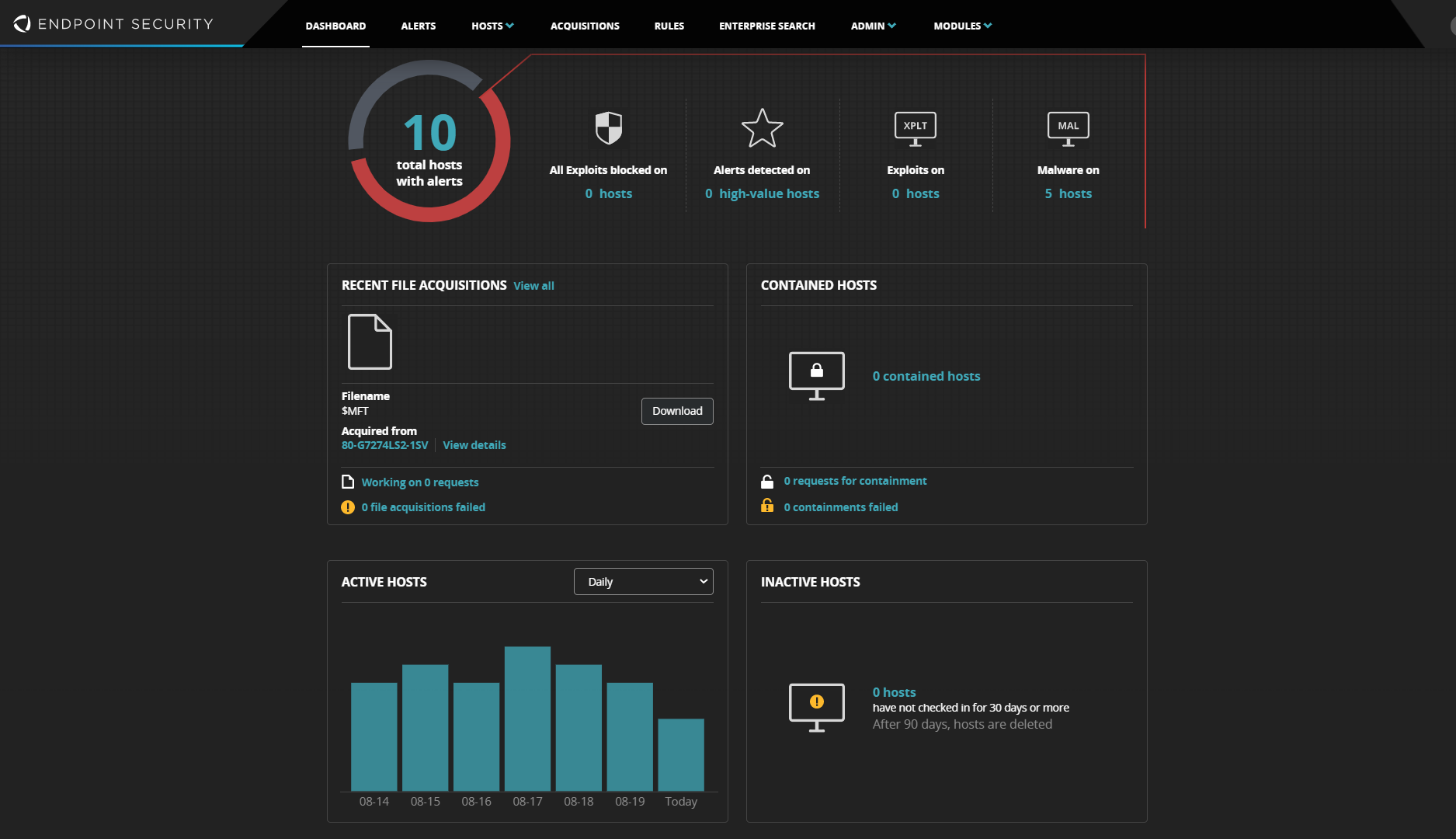
FireEye Endpoint Security
Additional Info
| Company | FireEye |
| Company size | 1,000 - 4,999 employees |
| Website | http://www.fireeye.com |
NOMINATION HIGHLIGHTS
Endpoint attacks can harm companies far more than the money spent in remediation. Systems are down, data is exposed, and companies may be liable for costs, not to mention reputational damage.
FireEye Endpoint Security protects against the threat of cyberattacks and reduces risk to users, data, and proprietary information, by defending where your data is stored and accessed. Combining multiple protection engines, endpoint detection and response (EDR) and threat intelligence, FireEye Endpoint Security detects and blocks simple and sophisticated attacks.
This protection is delivered by expert-built endpoint defense using targeted engines to protect against common threats, detect and block advanced attacks and respond to the breaches in a single agent. This defense in depth strategy provides protection with four integrated engines and customer deployable modules. The defense begins with a signature-based engine filtering out the known and common threats. For unknown or advanced malware, we have a machine learning, trained against a large library of real-world threats, called MalwareGuard. To protect against exploits in browsers and business software, we have a behavior analytics engine that detects unusual behavior and stops it before it can cause damage, called ExploitGuard. As no defense is 100% accurate, detection and response are through intelligence-based Indicators of Compromise (IOCs). These engines are updated with threat intelligence unique to FireEye.
In May 2020 we took innovation one step further. FireEye addressed the industry problem of time to respond to a new threat with a new modular framework. These customer deployable modules are created to rapidly respond to new threats tactics.
Using these engines and modules, customers can expect to see detection rates of over 99% with no false positives. Security teams are enabled to respond with intelligence-led information, so they can detect what other products miss while making staff more
How we are different
Unlike traditional endpoint security vendors, FireEye Endpoint Security delivers comprehensive defense using fully customizable protection modules. Supported by the world’s leading frontline Mandiant responders, the module creation blocks malware and exploits, detects advanced attacks, and provides the response tools and techniques that fit an organization’s unique risk profile and security posture.
One size doesn’t fit all when it comes to endpoint protection. For instance, a global healthcare company requires a different type of security protection on its endpoint than a regional manufacturer. Every organization needs a unique solution to protect its users and network from the threats and threat actors most likely targeting them. FireEye’s modular approach means organizations can benefit from the roll-out of new features or threat responses without waiting for the next upgrade. Customers can decide which modules they want to deploy and for whom, tailoring the level of protection down to an individual level if they choose. FireEye Endpoint Security modules fall under three general categories – Protection, Investigation & Response, and Enterprise Readiness – with several coming as a direct result of knowledge from the frontlines of cyber security from the efforts by Mandiant® Solutions to address specific growing threats.
FireEye’s unique differentiator is the extensive intelligence gained on the frontlines of the world’s most significant breaches to offer the strongest possible machine learning product. We’ve trained our model with public and private data sources, including data gathered from 18M+ endpoint agents, attack analyses based on over one million hours of incident response, and adversarial intelligence collected from a global network of analysts that speak 30+ languages. Our focus is on integrating that intelligence to constantly improve our anti-malware engines, like our machine learning and behavioral analysis models, to detect the latest malicious techniques – and when FireEye Endpoint triggers an alert, our customers know it’s worth investigating.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

