Gigamon ThreatINSIGHT
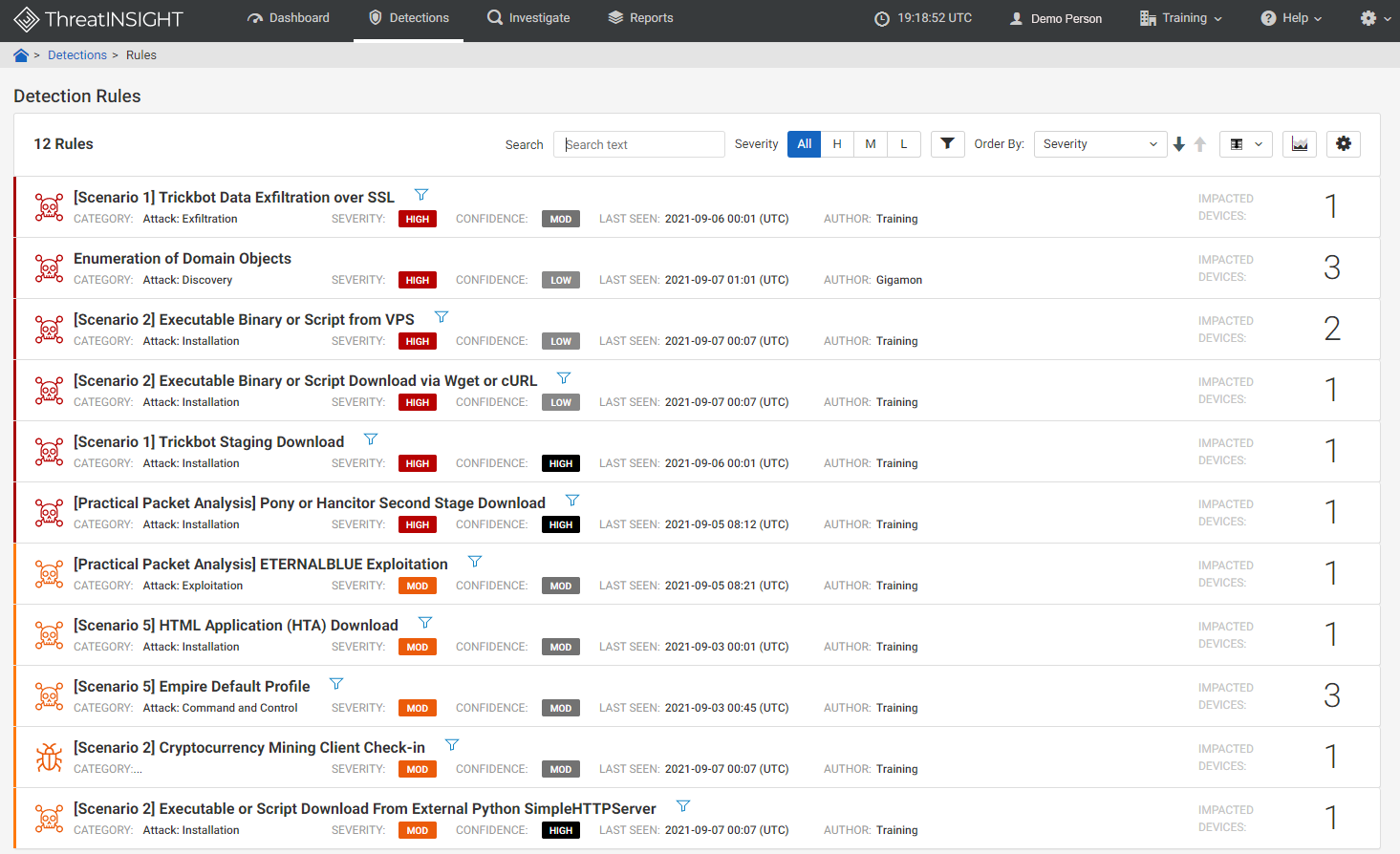
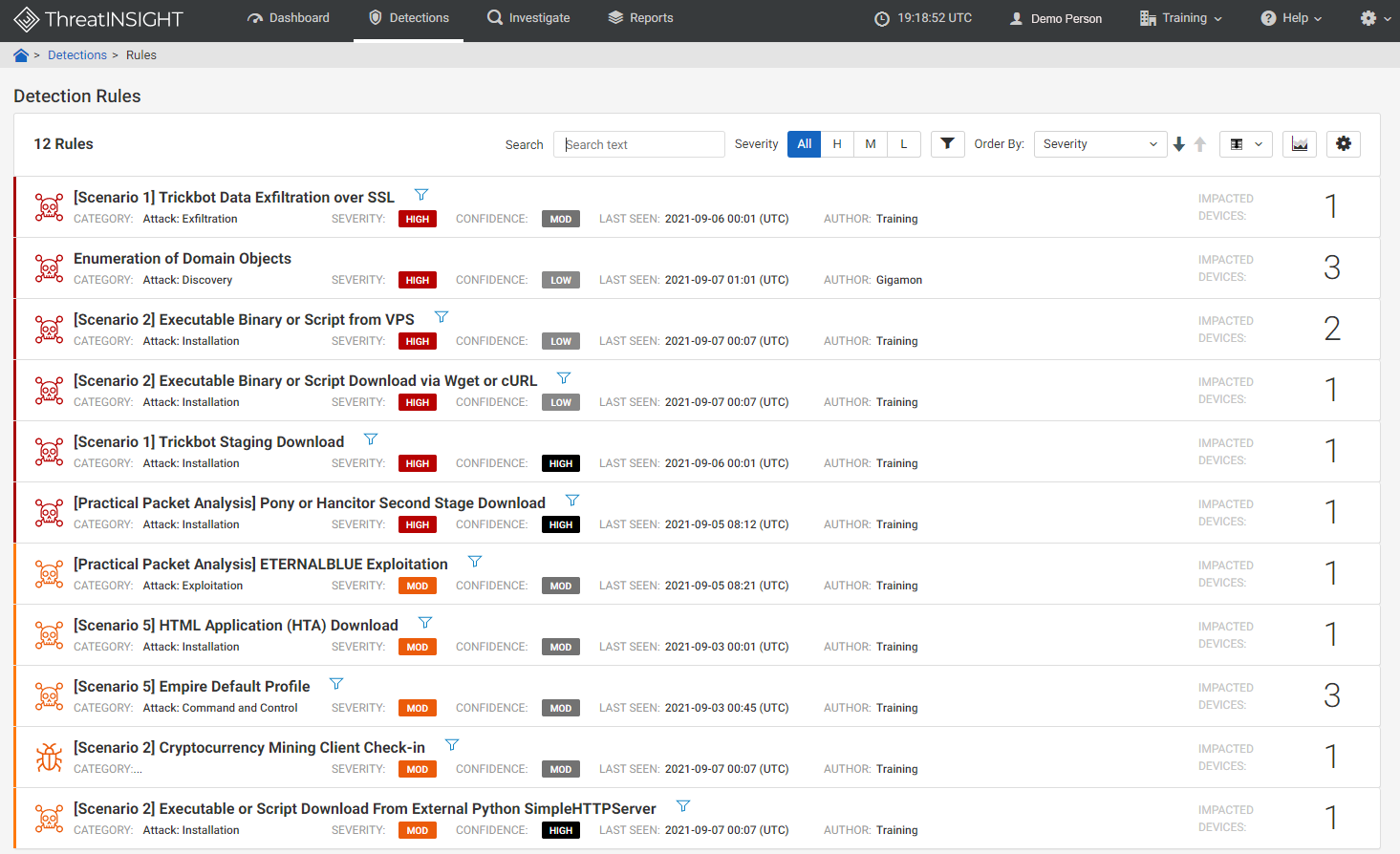
Photo Gallery
 |

 |
Gigamon ThreatINSIGHT


Additional Info
| Company | Gigamon |
| Website | https://www.gigamon.com/ |
| Company size (employees) | 500 to 999 |
| Type of solution | Cloud/SaaS |
Overview
Gigamon ThreatINSIGHT Guided-SaaS NDR™ is the industry’s first guided software-as-a-service (SaaS) network, detection and response (NDR) solution that’s purpose-built to help enterprises get ahead of investigating suspicious behavior and improve security operations center (SOC) analyst effectiveness. Gigamon ThreatINSIGHT Guided-SaaS removes burdensome distractions that otherwise prohibit teams from focusing on identifying adversary activity across the ATT&CK framework.
With ThreatINSIGHT Guided-SaaS NDR, teams are able to focus on threats, not tools, by getting started faster with plug-n-play deployment and zero maintenance. ThreatINSIGHT Guided SaaS NDR improves security posture with fast and efficient threat hunting to reduce exposure times to incidents. Teams are also able to leverage the Cloud Data Warehouse, which provides access to current and up to 356-day historical data across vectors from hybrid networks to provide the visibility and context needed for comprehensive investigative efforts regardless of dwell times
With a sharp rise in the adoption of NDR solutions to complement the endpoint detection and response (EDR) and security information and event management (SIEM) defense stacks, security professionals have recognized ThreatINSIGHT Guided SaaS NDR, the first cloud-native high-velocity NDR solution, as the representative solution in this space – awarded a Cyber Catalyst℠ designation as part of the annual Cyber Catalyst by Marsh℠ evaluation program in January 2021.
The recent significant increase in engagement from Gigamon core partners, and net new ones, also reinforce the significance of enduring these difficult times with a united front to be better prepared to support growth across industries. In response, November 2021 brought the integration of ThreatINSIGHT Guided-SaaS NDR and Crowdstrike, delivering seamless net-to-end visibility.
ThreatINSIGHT Guided SaaS NDR has also gained significant traction within the analyst community. The product was included in Gartner’s 2020 Market Guide for Network Detection and Forrester’s Now Tech: Network Analysis And Visibility Q2 2020 report.
How we are different
- Visibility is foundational to any effective security posture, particularly visibility into all network communications. However, modern IT infrastructure is increasingly complex and is constantly changing, leading to security blind spots.Gigamon ThreatINSIGHT Guided- SaaS NDR is purpose-built to help enterprises get ahead of investigating suspicious behavior and improve security operations center (SOC) analyst effectiveness. It stands out from other solutions within the industry by taking a data-centric approach to threat detection across both inbound and outbound (north/south) and internal (east/west) network communications. The sensors pass the information into the INSIGHT Cloud Data Warehouse, where the metadata is indexed, and enriched with information and stored for 356 days for easy access to historical data needed to address the increase in ransomware threats with long dwell times.
-ThreatINSIGHT Guided-SaaS NDR provides expert-level guidance and addresses the challenges of SOC burnout. Gigamon is the only NDR vendor on the market to offer each subscription with expert-level guidance from Gigamon Technical Success Managers (TSM), who are seasoned incident response practitioners that help with use case expansion, alignment to industry best practices and user-relevant support. Additionally, ThreatINSIGHT is supported by the world-class Gigamon Applied Threat Research (ATR) team, delivering leading-edge detection capabilities. This means having access to adversary knowledge and indecent management guidance during high-pressure active threats. Gigamon ThreatINSIGHT also combats SOC analyst distraction with zero tool maintenance or detection tuning.
- ThreatINSIGHT Guided-SaaS NDR gives SOC teams the edge in finding real-world threats and improves their effectiveness. 365-day data retention gives analysts the insight they need to remediate threats, regardless of dwell times. Guided Playbooks improve investigators’ ability to find attackers based on real-world behaviors at the click of a button. SignalStream aggregates ThreatINSIGHT data into an organization’s SEIM for more thorough investigations.



