“Group-IB Threat Hunting Framework & Group-IB Digital Risk Protection”
Photo Gallery
 |
 |
"Group-IB Threat Hunting Framework & Group-IB Digital Risk Protection"

Additional Info
| Company | Group-IB |
| Website | "https://www.group-ib.com/threat-hunting-framework.html & https://www.group-ib.com/digital-risk-protection.html" |
| Company size (employees) | 500 to 999 |
| Type of solution | Hybrid |
Overview
“Back in 2011, we created a certified computer emergency response service, united by a mission: to immediately contain cyber threats, regardless of when and where they take place and who is involved.
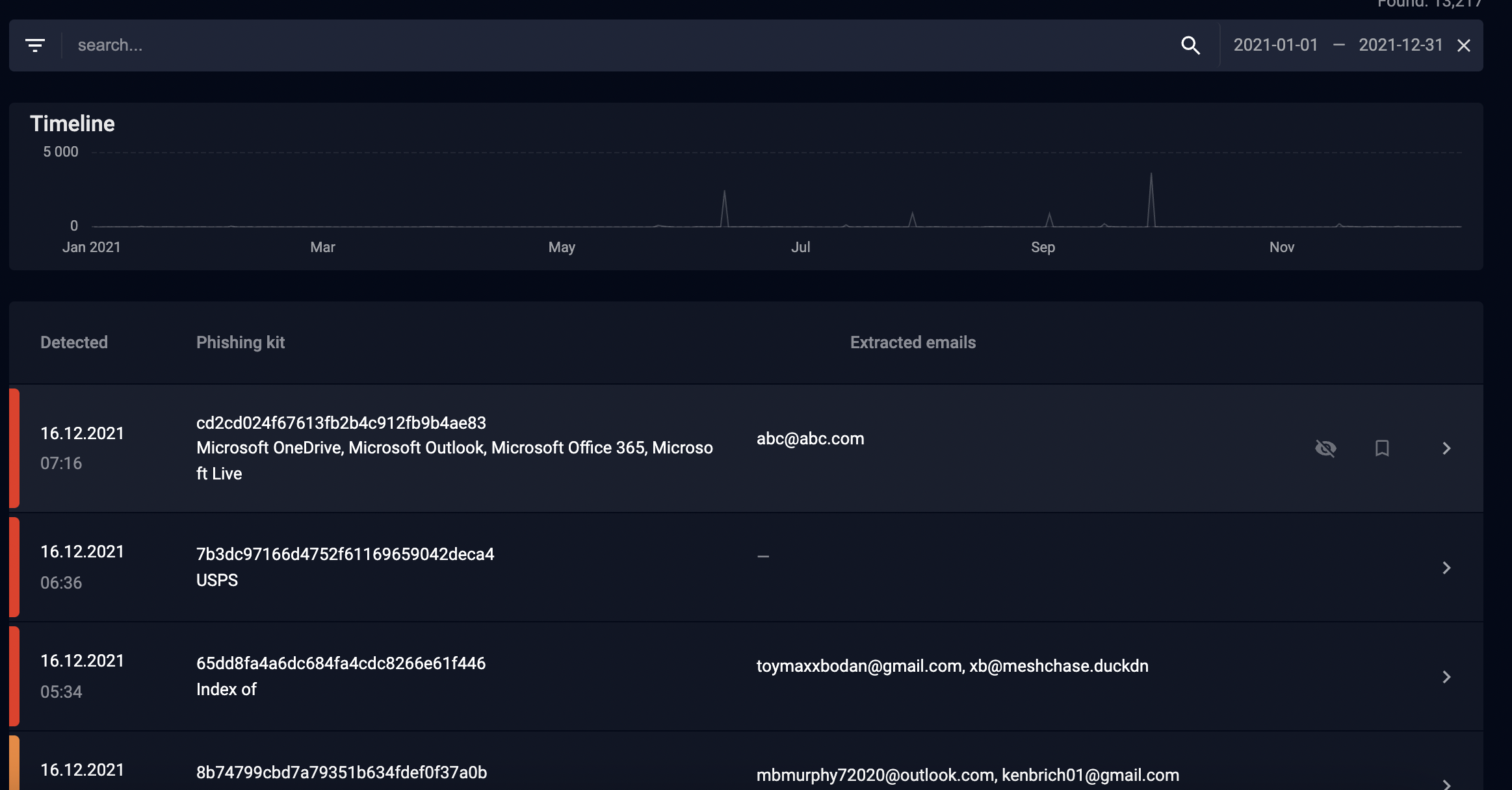
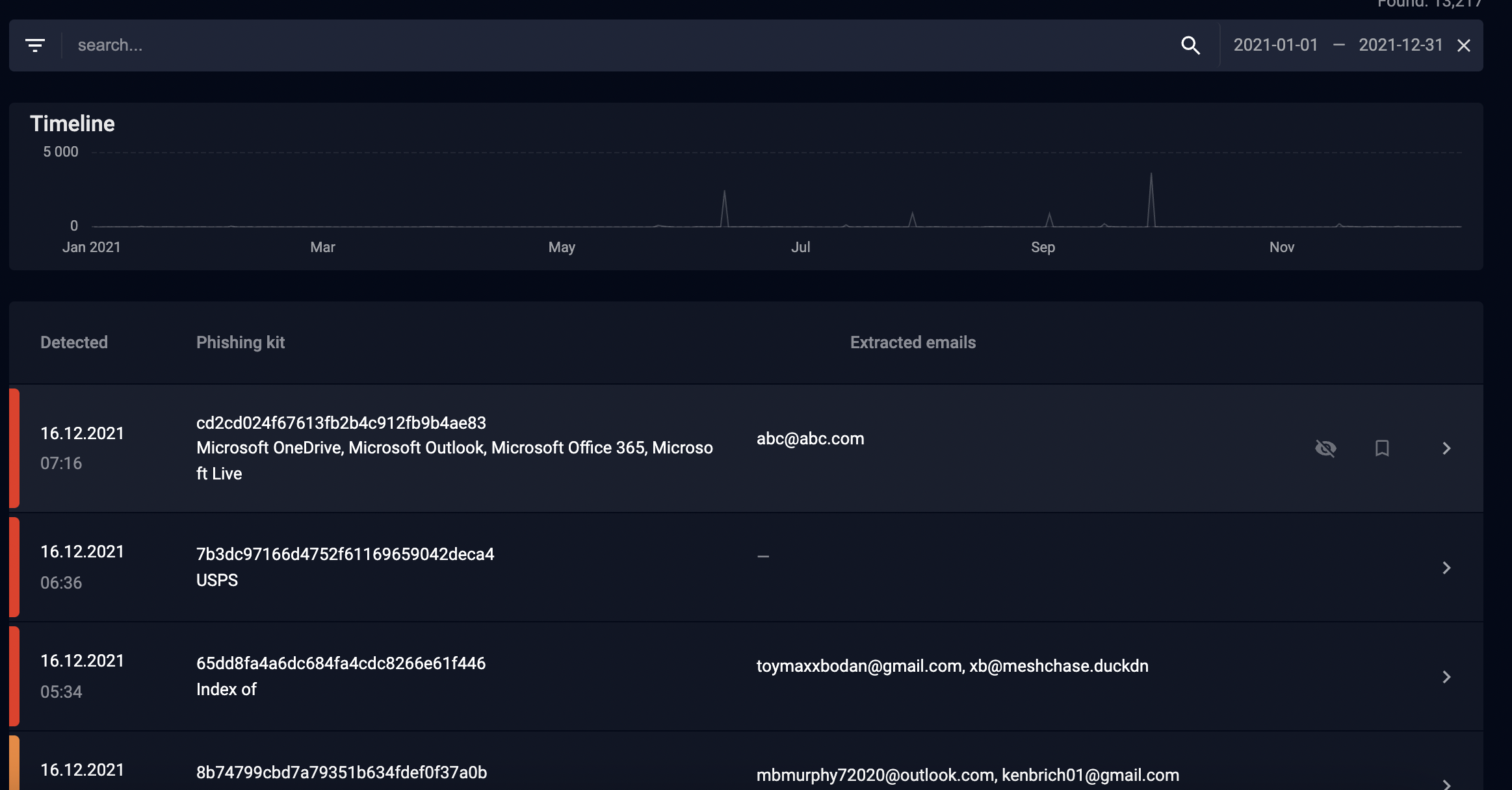
In this regard, Group-IB Threat Hunting Framework operates as a single system for managing detection infrastructure, automated analysis, event and alert storage, and retrospective incident analysis. It helps CERT-GIB manage incidents effectively and efficiently, gives analysts access to an extensive database of events, and reduces the time spent on incident analysis thanks to automatic grouping and correlation.
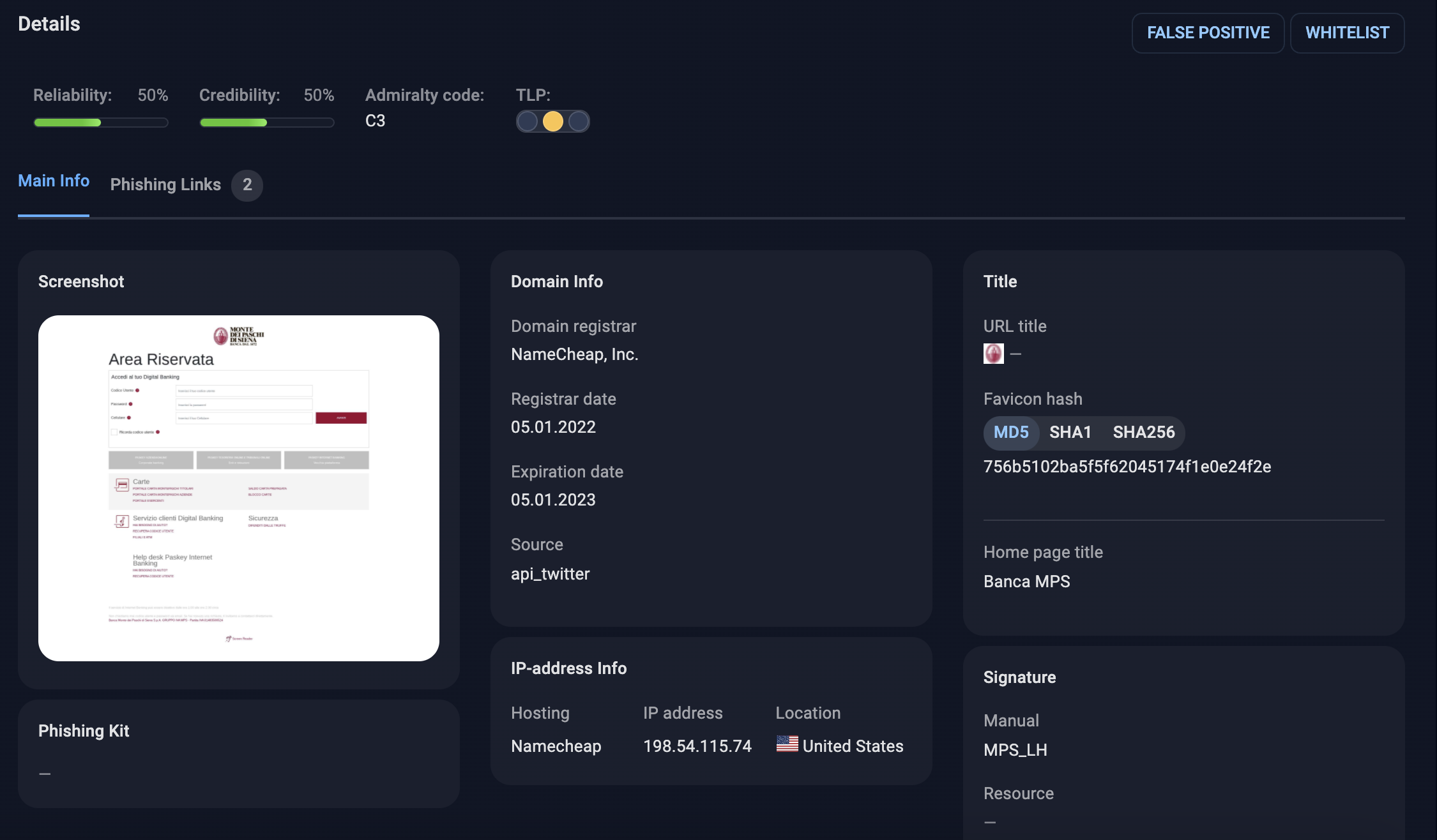
For its part, Group-IB Digital Risk Protection uses artificial intelligence technologies to detect the illegitimate use of logos, trademarks, content, and design layouts. Group-IB Digital Risk Protection automatically monitors millions of online resources where the customer’s brand or intellectual property may be present 24/7/365. Collected data includes screenshots, images, html files, redirect chains, traffic sources, and domain-related parameters.
Once violations are determined, every effort is made to eliminate them. Group-IB’s solution implements a comprehensive takedown procedure that has resulted in an 85% takedown rate pre-trial (20,000 violations a day). Again, the combination of automation and human expertise results in the fastest possible response time and makes Group-IB’s solution reliable.
Group-IB DRP implements a three-stage takedown process to maximize the chances of violations being eliminated.
1. Notification
Our team identifies the resource owner and requests them to remove the detected violation.
2. Enforcement
Group-IB leverages its global network of partnerships with domain registrars, hosting providers, social media admins, and CERTs to enforce the removal of the violation.
3. Cease and desist
We obtain official pre-trial orders for the detected violation & takedown
How we are different
"· Group-IB anti phishing technology is based on 33 Group-IB's own cutting-edge solutions and inventions, patented around the world.
· Thanks to Group-IB established cooperation with international organizations (FIRST, Trusted Introducer, APWG, OIC-CERT, and others) and CERTs in 150+ countries of the world, we сan promptly block malicious and phishing sites in more than 2500 domain zones.
· We provide 24/7/365 qualified monitoring, phishing blocking and support from experienced CERT-GIB specialists.
"



