Photo Gallery

|


|
Instart Web Skimming Protection

Additional Info
| Company | Instart Web Skimming Protection |
| Company size | 100 - 499 employees |
| Website | https://www.instart.com/products/skimming-protection |
NOMINATION HIGHLIGHTS
Modern web apps rely on JavaScript to bring enhanced functionality, but these scripts open them up to the possibility of attacks that target your customers’ PII. JavaScript, whether first-party code or from a third-party, has complete access to a web page, meaning any script has the ability to skim sensitive data.
Web skimming attacks are extremely difficult to detect since they do not occur within a company’s infrastructure. Instead, malicious JavaScript is loaded directly into a visitor’s browser away from all internal security controls — completely invisible to traditional security solutions that would normally raise flags if unusual activity is detected.
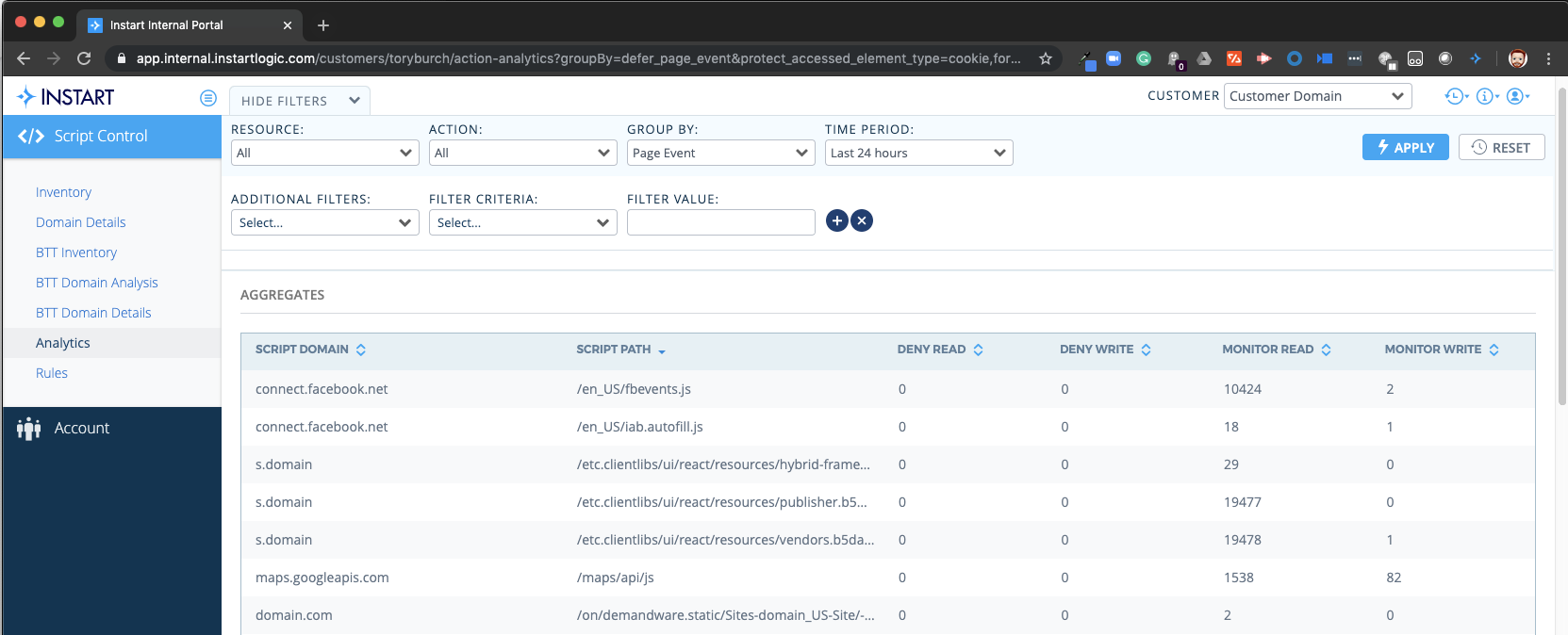
Instart offers industry-leading protection against web skimming attacks to prevent data exfiltration from occurring within the browser. Using its unique Nanovisor technology, Instart Web Skimming Protection provides customers granular control over which sensitive data JavaScript can access in the browser so your customer’s data stays safe and you avoid privacy violations.
Instart Web Skimming Protection provides:
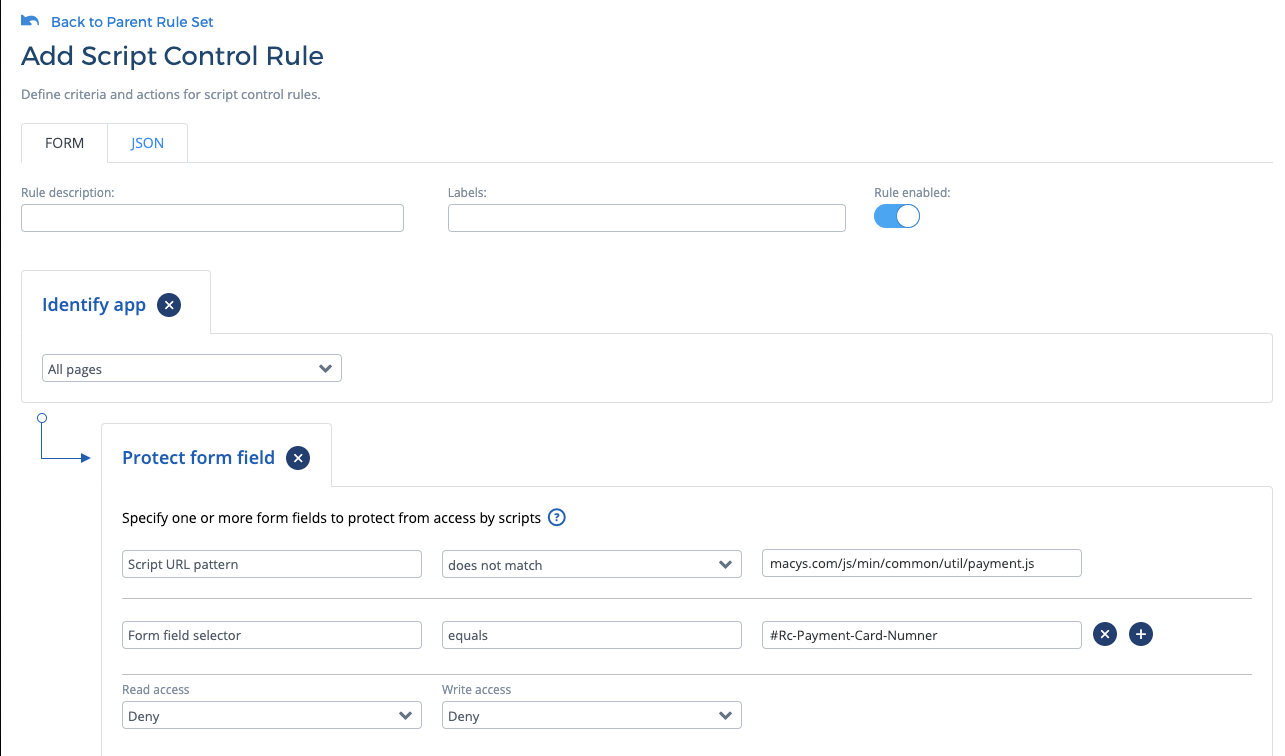
Form protection: Whitelist only the JavaScript that legitimately needs access to form content by preventing the reading of form data, such as passwords, social security numbers, or credit card information, from unauthorized scripts.
Cookie protection: Control cookie access by preventing the reading of private data within cookies, such as names, addresses, and telephone numbers, from unauthorized scripts.
Third-party JavaScript control: Granular control over third-party JavaScript allows you to manage the content the scripts can access on a web page as well as whether they are allowed to run at all.
Unauthorized script access alerting: Proactive alerting when unauthorized access to form fields or cookies is detected.
Cutting-edge nanovisor technology: Instart’s nanovisor, a patented JavaScript virtualization technology allows agentless visibility into JavaScript activity within the web browser, delivering the benefit of unrivaled control.
How we are different
Web skimming attacks like those carried out by Magecart have been making recent headlines for targeting eCommerce websites in an attempt to plant skimming code to steal credit card numbers. Magecart skimming code has been implicated in over 2 million web skimming attacks to date, including companies such as Macy’s, British Airways, and TicketMaster.
The results of these new types of attacks are profound: In the British Airways example, attackers stole sensitive information (names, addresses, credit card information) from 500K+ customers in just 15 days. This led to a $250M fine for failing to protect customer information. The threat is real with very real consequences.
Instart provides the only solution on the market today that can not only detect when a script is accessing information that it shouldn’t, but can prevent the script from getting access in the first place. This is done by adopting a zero-trust model that limits JavaScript access to HTML form fields and cookies unless they are explicitly given permission.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

