Intezer Analyze
Photo Gallery
 |
Intezer Analyze
Additional Info
| Company | Intezer |
| Website | analyze.intezer.com |
| Company size (employees) | 50 to 99 |
| Type of solution | Cloud/SaaS |
Overview
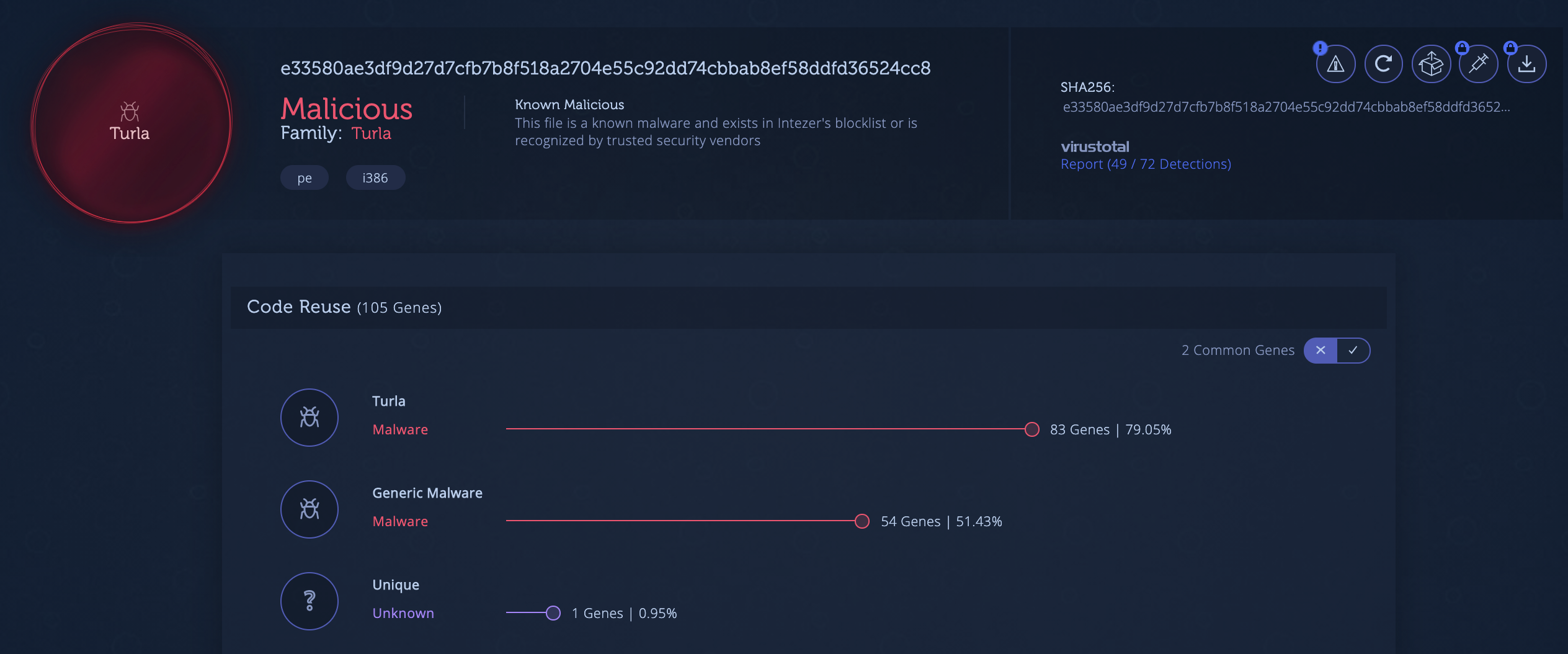
Intezer Analyze is a malware analysis platform that quickly classifies malware and unknown files. The platform is helping security analysts automate some of the most advanced and time-consuming assignments they face today, including reverse engineering and malware classification.
Today’s malware analysis solutions rely on behavioral analysis and signature-based techniques but they are struggling to provide context and increasingly evaded by sophisticated attacks. Intezer classifies cyber attacks at the most granular level by divulging their code origins. Detecting code reuse between threats results in a much deeper understanding of any unknown or malicious file.
Intezer Analyze community users can classify up to 50 files per month for free and have access to features such as IDA Pro and Ghidra plugins, view code and string reuse between threats, and track malware families to get updates on new samples spotted in the wild through code reuse detection.
The technology behind Intezer Analyze has detected code similarities in high-profile nation-state attacks before leading engines and government agencies, including WannaCry, Turla, and Winnti.
How we are different
• Specializing in malware classification. Unlike Antivirus and EDRs, which mostly produce generic results (think Trojan.Generic) and only classify specific hashes, Intezer analyzes the code itself in order to classify the threat and identify variants from the same malware family.
• Accurate detection for APTs where other analysis systems fail.
• “Intezer’s one-of-a-kind technology based on code reuse detection is exactly what our IR teams needed to classify threats. Obtaining deep insights into every suspicious file in seconds saves precious time and efforts, enabling the team to focus on prioritizing and remediating attacks.” —IR Team Lead, Fortune 500 company



