Photo Gallery

|

|
Netsurion® Managed Threat Protection

Additional Info
| Company | Netsurion |
| Company size | 100 - 499 employees |
| Website | https://www.netsurion.com/managed-threat-protection |
NOMINATION HIGHLIGHTS
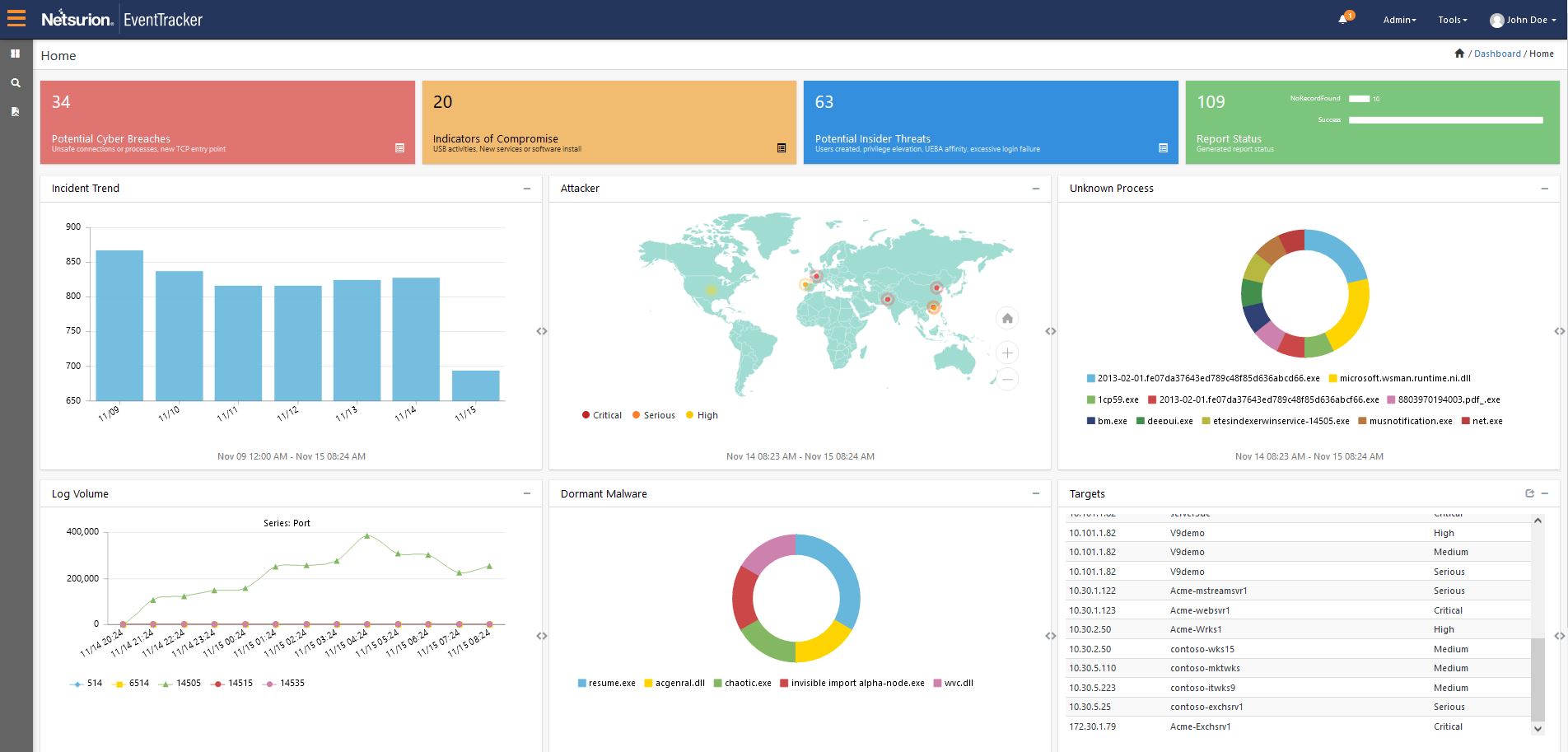
Netsurion Managed Threat Protection is a complete managed security service and platform to predict, prevent, detect, and respond to threats across your network and your entire business. Whether you need a targeted supplement to your existing capabilities and staff or a complete outsourced solution, the managed service is uniquely customizable to your needs. Our comprehensive approach provides capabilities such as advanced network protection, SIEM, actionable threat intelligence, user analytics, and threat hunting, all from one central cloud console. All this technology is combined with our ISO-certified Security Operations Center (SOC) monitored by experts protecting your business 24/7/365.
Network security analytics provides a more in-depth view of cyber criminals and low-and-slow attacks that wait days or even months to launch. We provide unparalleled insights into network threats and possible blind spots. Netsurion optimizes network, user, and application performance with rich context around possible cyber attacks.
Netsurion defends against advanced threats like ransomware targeting endpoints that bypass traditional tools like anti-virus. We prevent all that we can with endpoint security powered by deep learning, and rapidly detect and remediate everything else. Netsurion Managed Threat Protection service provides a holistic all-in-one solution across network, endpoints, and the cloud that is simple and affordable. We increase your effectiveness by reducing false positives, providing remediation recommendations, and prioritizing your next steps. Netsurion’s comprehensive reports and intuitive dashboards provide guidance that enables customers to engage their leadership on topics like cybersecurity maturity. You receive coverage across the entire threat cycle, from prediction, prevention, detection, and rapid response that enhances your cybersecurity maturity over time. Gain a practical way to overcome today’s cybersecurity challenges like ransomware and insider threats, so you can get back to the business of growth and innovation.
How we are different
Netsurion differentiators include the following:
* Improve Attack Surface Visibility and Coverage
In addition to network detection and response, Netsurion safeguards data across servers, endpoints, and the cloud. We integrate MITRE ATT&CK data to help pinpoint how attackers entered organizations and the path of compromise called the “cybersecurity kill chain”. Managed Threat Protection from Netsurion also provides applicable threat controls such as Security Information and Event Management (SIEM), Intrusion Detection System (IDS), Network Traffic Analysis (NTA) and our 24/7/365 Security Operations Center (SOC). Our comprehensive reports outline remediation recommendations that help you reduce attacker dwell time and lateral movement. Our proactive protection also ensures that compromised devices are fully detected and blocked for rapid threat detection and response with minimal false positives.
* Detect Threats Already in Your Network with Behavior Analytics
Compromised login credentials are found in over 80% of all network intrusions. Traditional IT tools provide limited visibility and protection against stolen user credentials. Cyber criminals use leaked or stolen credentials to pivot to other more attractive servers and sensitive data. Netsurion leverages machine learning (ML) and automation to trigger alerts in real time when anomalous behavior could signal a data breach.
* Enhance Network Performance and Uptime
Netsurion helps organizations harness network flow data from devices like routers to identify anomalies and detailed network operating issues. We continuously analyze raw network traffic for both an automated and manual response to network threats. Intuitive dashboards from EventTracker Network Traffic Analysis (NTA) provide insights such as:
- Protocols like RDP that attackers often exploit
- Ports that are exposed to the internet
- Top “talkers” and applications
- Source and destination IP addresses that may represent risky network traffic

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

