Proofpoint Cloud App Security Broker (CASB), Enterprise DLP, Insider Threat Management, Web Security, Remote Browser Isolation and Zero Trust Network Access (ZTNA)
Recognized in the Category:
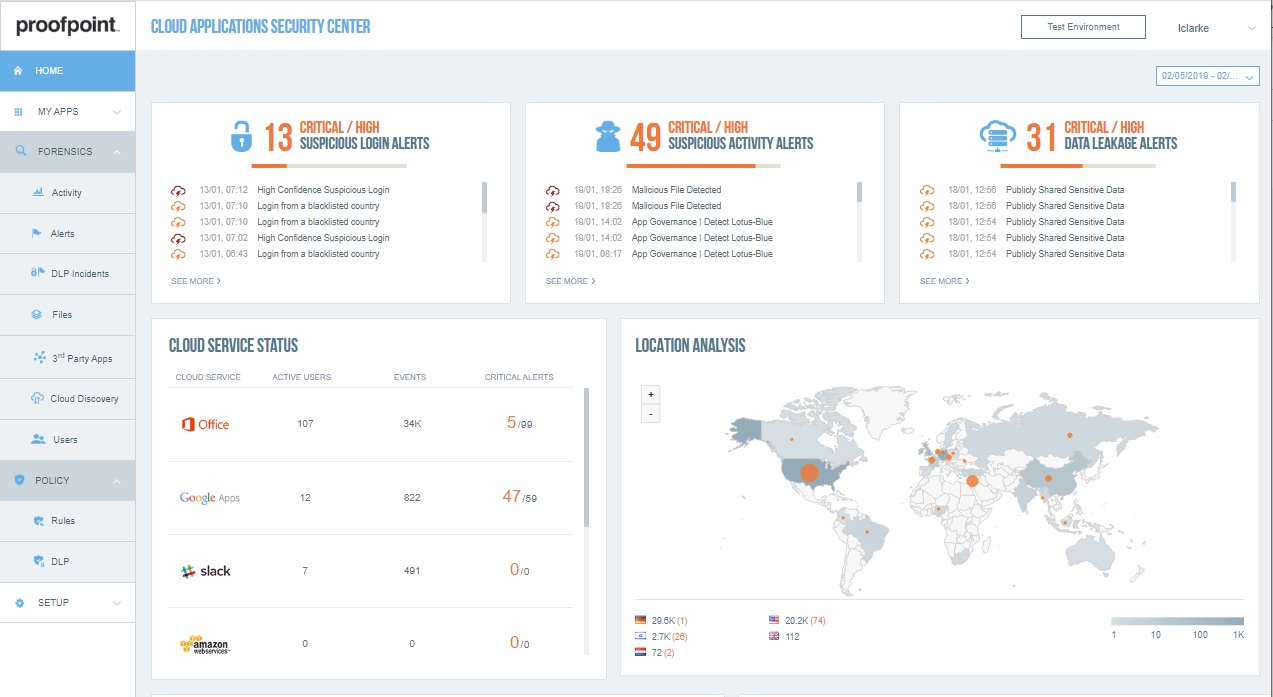
Photo Gallery
|

|
Proofpoint Cloud App Security Broker (CASB), Enterprise DLP, Insider Threat Management, Web Security, Remote Browser Isolation and Zero Trust Network Access (ZTNA)
Additional Info
| Company | Proofpoint |
| Company size | 1,000 - 4,999 employees |
| Website | https://www.proofpoint.com/us |
NOMINATION HIGHLIGHTS
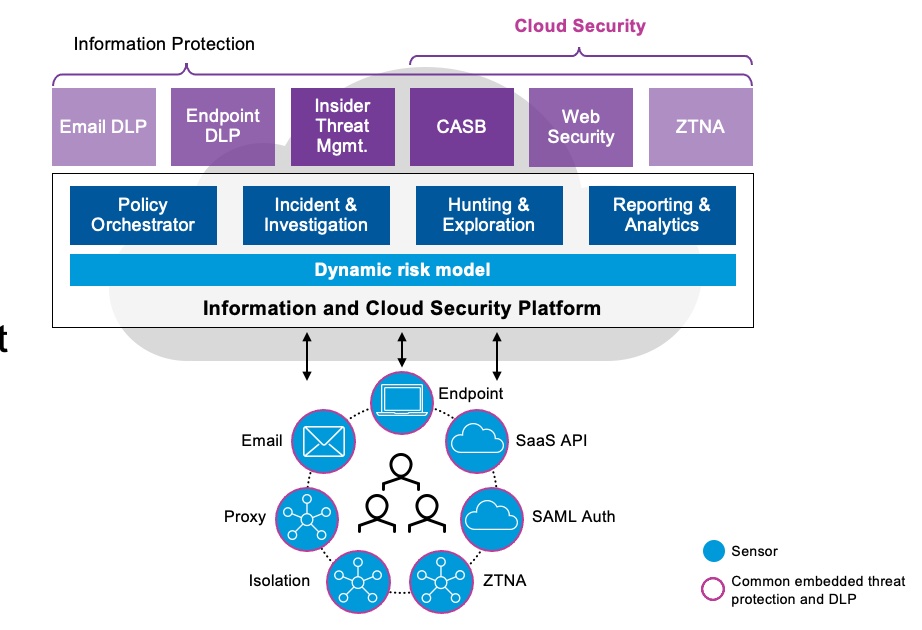
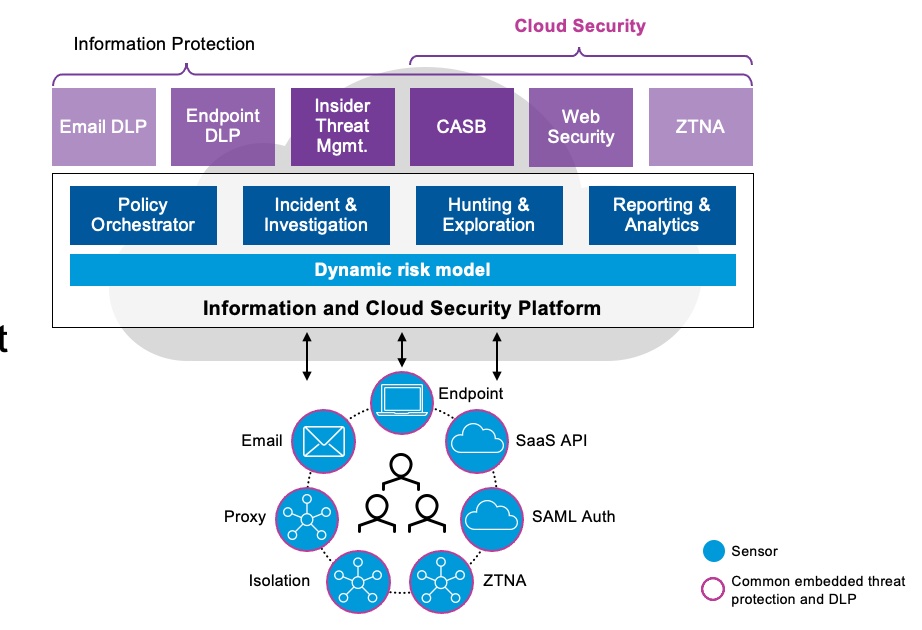
Proofpoint Information and Cloud Security Platform brings together Proofpoint Enterprise DLP, Proofpoint Insider Threat Management, CASB, ZTNA, Browser Isolation and Web Security. This powerful, cloud-native single platform aligns to the industry vision of the SASE architecture, where organizations can apply secure access and threat protection as people access applications and data, no matter their location or device type.
Our platform delivers a unique people-centric approach to access governance for the internet, cloud services and private applications, and DLP across email, cloud apps, the web and endpoints. It combines:
A comprehensive suite of information protection and cloud security solutions
A unified administration and response console
Intelligent risk modeling
World-class threat, content and behavior detection
People-centric visibility and controls
Proofpoint Cloud Security unifies people-centric access controls and threat protection for users of internet, cloud and private applications within a global cloud-native platform. To enable adaptive and people-centric secure access across the enterprise, we combine:
Granular controls such as risk-based authentication, read-only access and micro-segmented application access
Rich, cross-vector threat intelligence on user risk
Advanced threat protection
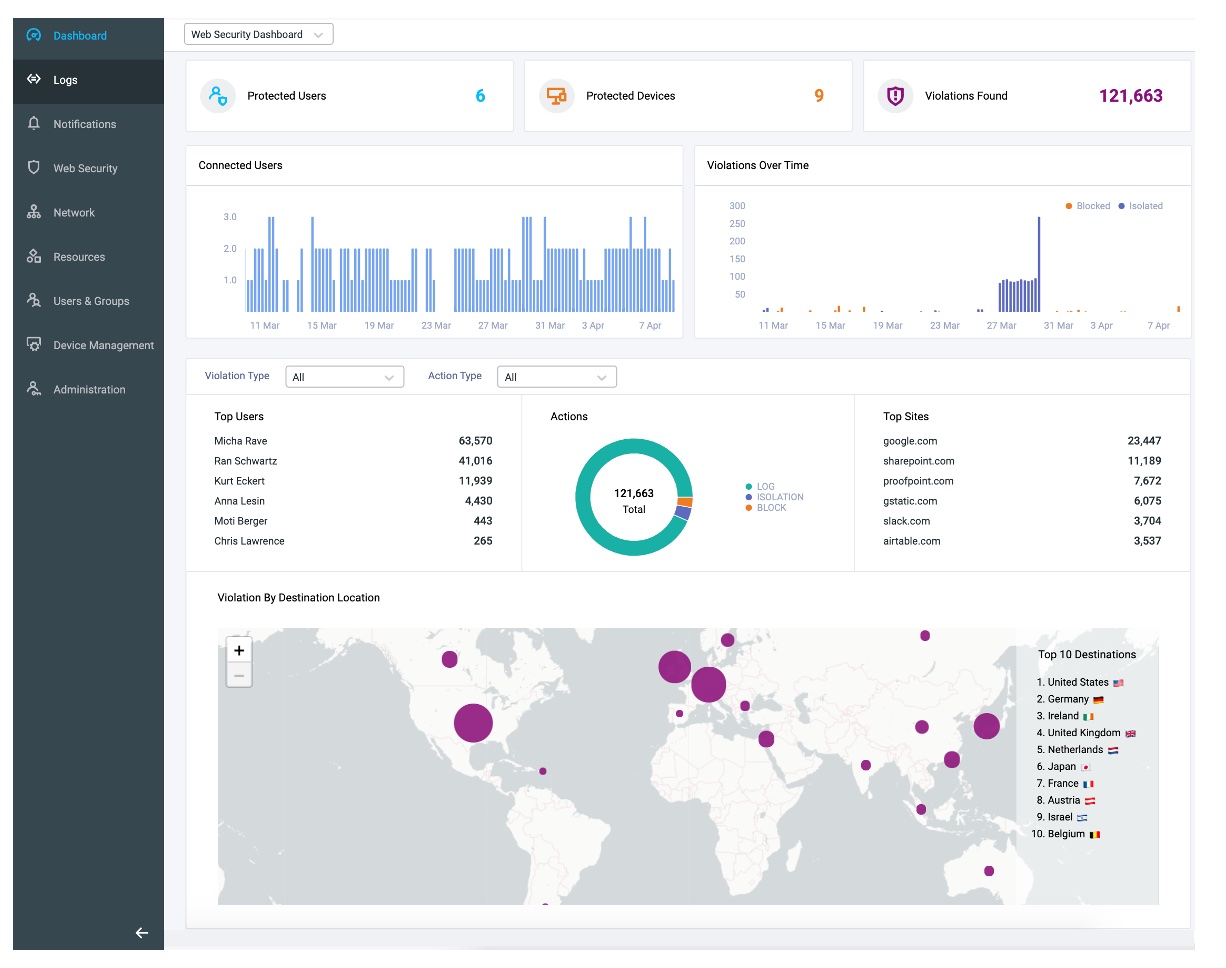
With coverage across all DLP channels and a common data classification framework, Proofpoint Information Protection solution combines content, behavior and threat-based telemetry with sophisticated analytics. Security teams worldwide rely on Proofpoint to address the full spectrum of data loss scenarios across malicious, negligent and compromised users. Its unified alerts also help users better prioritize warnings, respond faster and achieve a shorter time to value.
Our unified admin and response console simplifies day-to-day security operations and accelerates response by combining advanced tools:
Uniform policy management
Common Incident and investigative workflow across cloud, web and private apps
Advanced threat hunting and explorations
People-centric and intuitive timeline-based reporting and analytics
Granular administration and data privacy controls
How we are different
Proofpoint’s solution for SASE differentiates from competitors with people-centric and high-efficacy security analytics that excel at protecting users from threats, such as account compromise, malicious files, malicious apps, abuse of third-party OAuth app access, abuse of IaaS resources and initial access and preparation of ransomware attacks. Competitors fall short in the following areas: shallow depth in detecting account compromise, inability to correlate compromise with post-compromise activity that dramatically slows down security response and incomplete account takeover remediation capabilities across Microsoft, Google and Okta federated applications
Data loss originates with people. They can be negligent, compromised, or malicious. Understanding user intent enables you to apply the appropriate DLP response to mitigate risk. Proofpoint is the only vendor that brings together the telemetry of content, user-behavior and threats across the most critical DLP channels – cloud (SaaS and IaaS storage), email, endpoint and web. Competitors fall short in either their inability to bring together the DLP channels into one console for triage and response or cant correlate threat and user behavior to the data movement.
With Proofpoint’s solution for SASE, you can govern SaaS, web and private apps, as well as IaaS services in a centralized management console. We prioritize context into the apps with the most app vulnerabilities, the most attacked or abused and contain the most sensitive data or accessed by the privileged users. This includes first-party cloud apps (such as Microsoft OneDrive and Salesforce) as well as third-party (such as those created within Google Workspace, Microsoft appStore or federated through OAuth tokens). Competitors fall short by either missing the context of which apps are most abused or attacked in the real-world or lack the depth of detection capabilities in third-party apps such as OAuth authenticated apps.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

