Proofpoint Email Security
Photo Gallery
 |

 |
Proofpoint Email Security
Additional Info
| Company | Proofpoint |
| Website | https://www.proofpoint.com/us |
| Company size (employees) | 1,000 to 4,999 |
| Type of solution | Cloud/SaaS |
Overview
Proofpoint Threat Protection Platform effectively detects and blocks advanced malware spread via email. No matter how malware is delivered- through malicious attachments, URLs or even file-sharing sites, Proofpoint can stop it before it reaches end users’ inboxes.
To better detect advanced malware, such as ransomware and polymorphic malware, Proofpoint utilizes a combination of dynamic, static and protocol analysis techniques to inspect the full attack chain. Powered by Nexus Threat Graph that aggregates and correlates over a trillion threat data points across email, cloud network and social media, Proofpoint Threat Protection Platform delivers unique visibility into the everchanging threat landscape and provides unparalleled malware detection and response.
This technology helps prevent credential theft and protects users against malware and malicious content, especially for phishing emails that contain URLs that become unsafe after they’re delivered.
Proofpoint’s predictive sandboxing technology preemptively sandboxes file sharing URLs before users click rather than relying solely on reputation. It successfully addresses attackers hosting and delivering malicious payloads via legitimate filesharing sites, such as SharePoint and OneDrive. It is more effective at stopping attacks that abuse the trust of legitimate file sharing sites and multi-stage attacks that hide the payload within these sites.
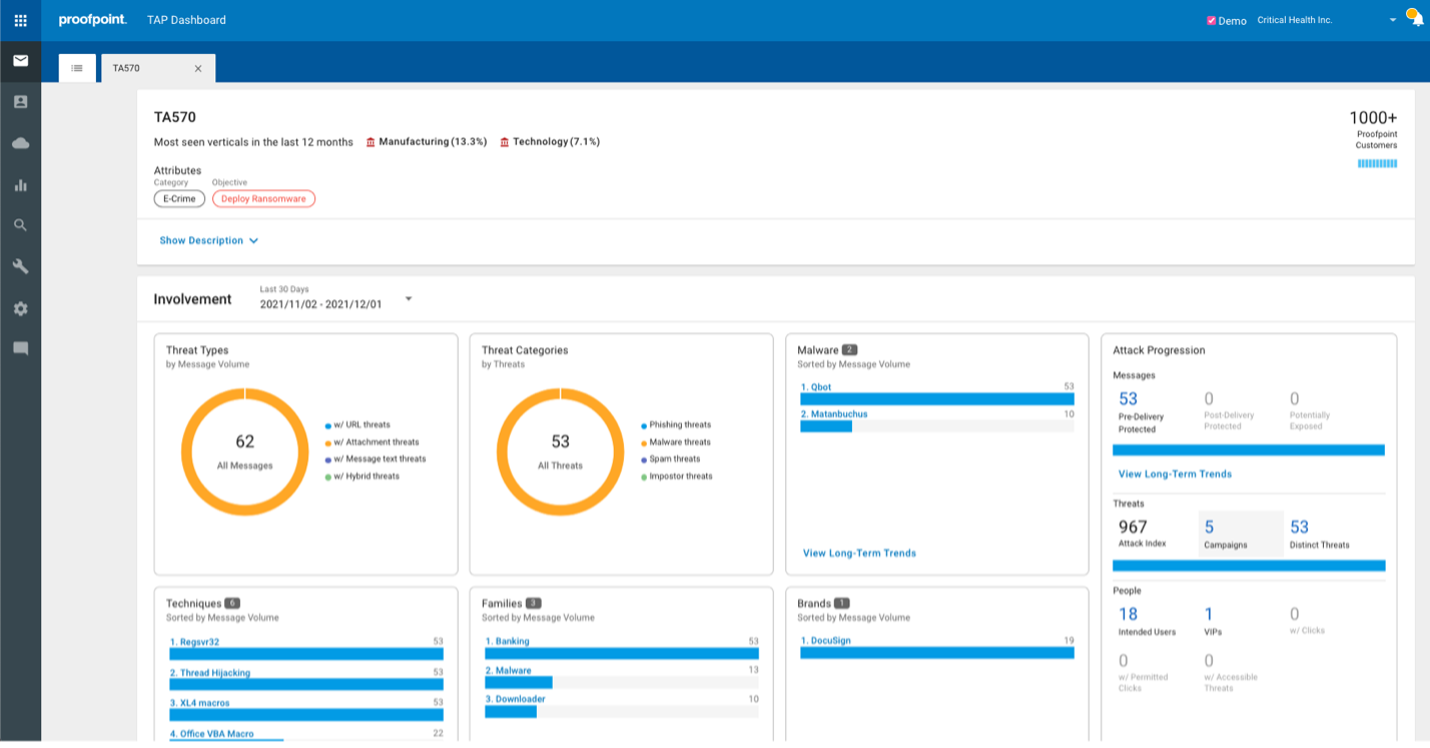
With actionable visibility into complex attack campaigns, Proofpoint provides security teams with insight around who and what is targeted and how, as well as the threat actors involved and the malware and tools they use. It sees everything – from advanced malware and other attacks targeted at the people within the organization, to files in your SaaS file stores for a far-reaching view of the threat landscape.
How we are different
● Stop More Threats, Faster: Proofpoint provides the most effective threat protection and leads the way in new detection techniques that stop various types of email threats, including ransomware, multi-stage malware, credential phishing, email fraud, and account compromise.
Our effectiveness is powered by the Nexus Threat Graph, which is built on billions of emails per day, millions of cloud accounts and 400k-600k malware samples per day from over half of the Fortune 1000. We continuously update our detection engines to address changes in the threat landscape. Through product evaluations against other vendors, Proofpoint always identifies a host of malicious emails evading existing systems.
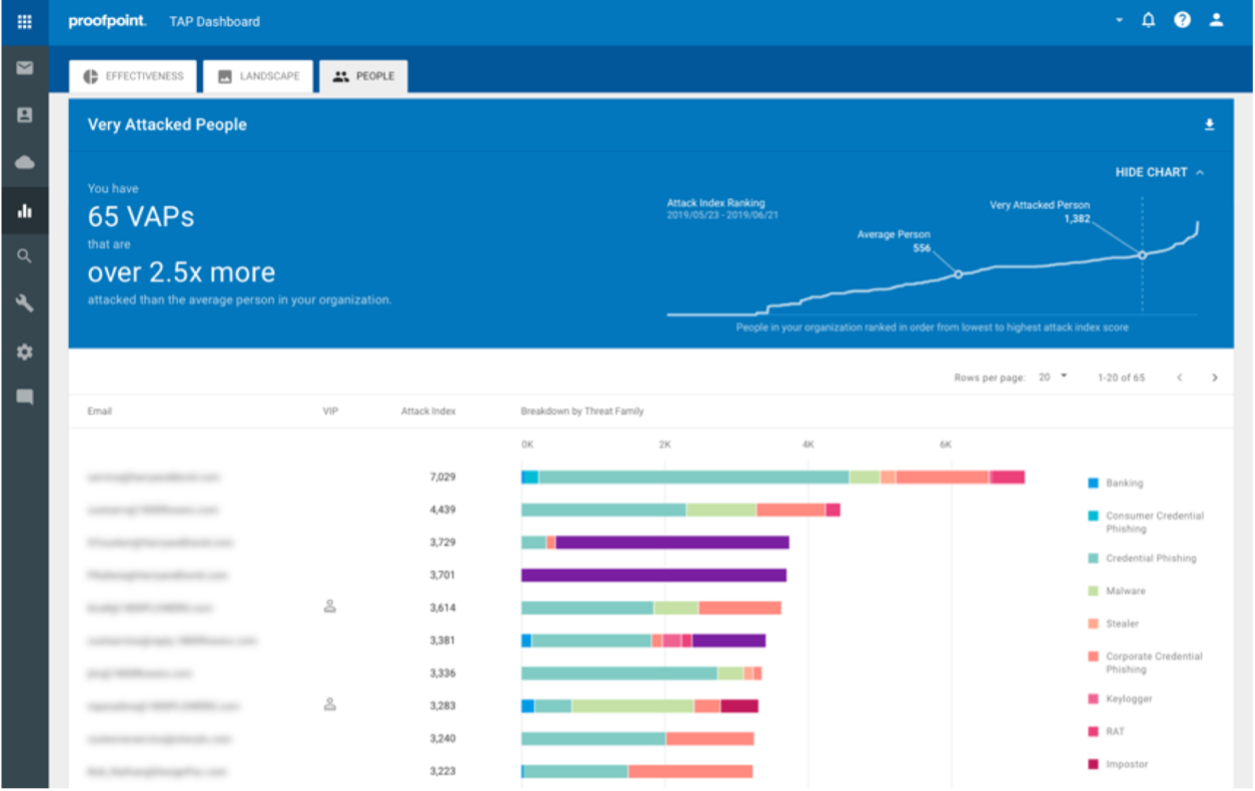
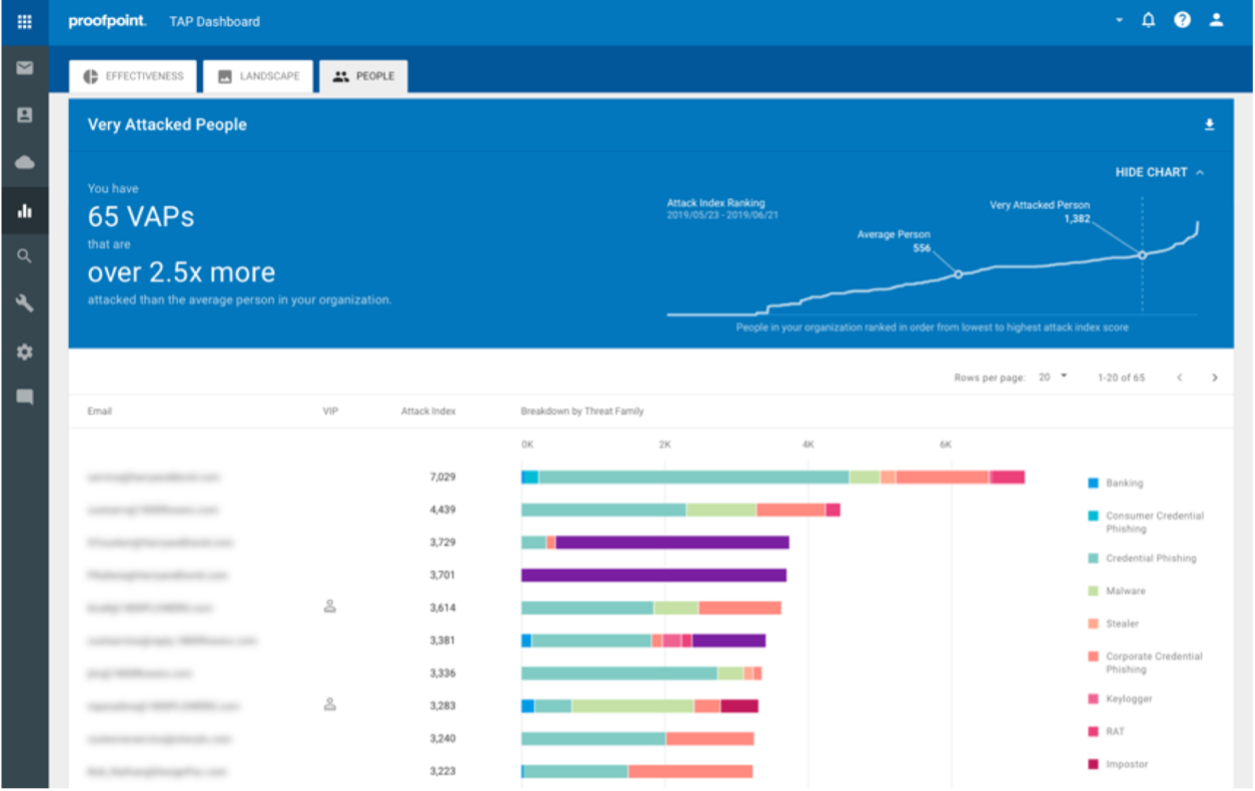
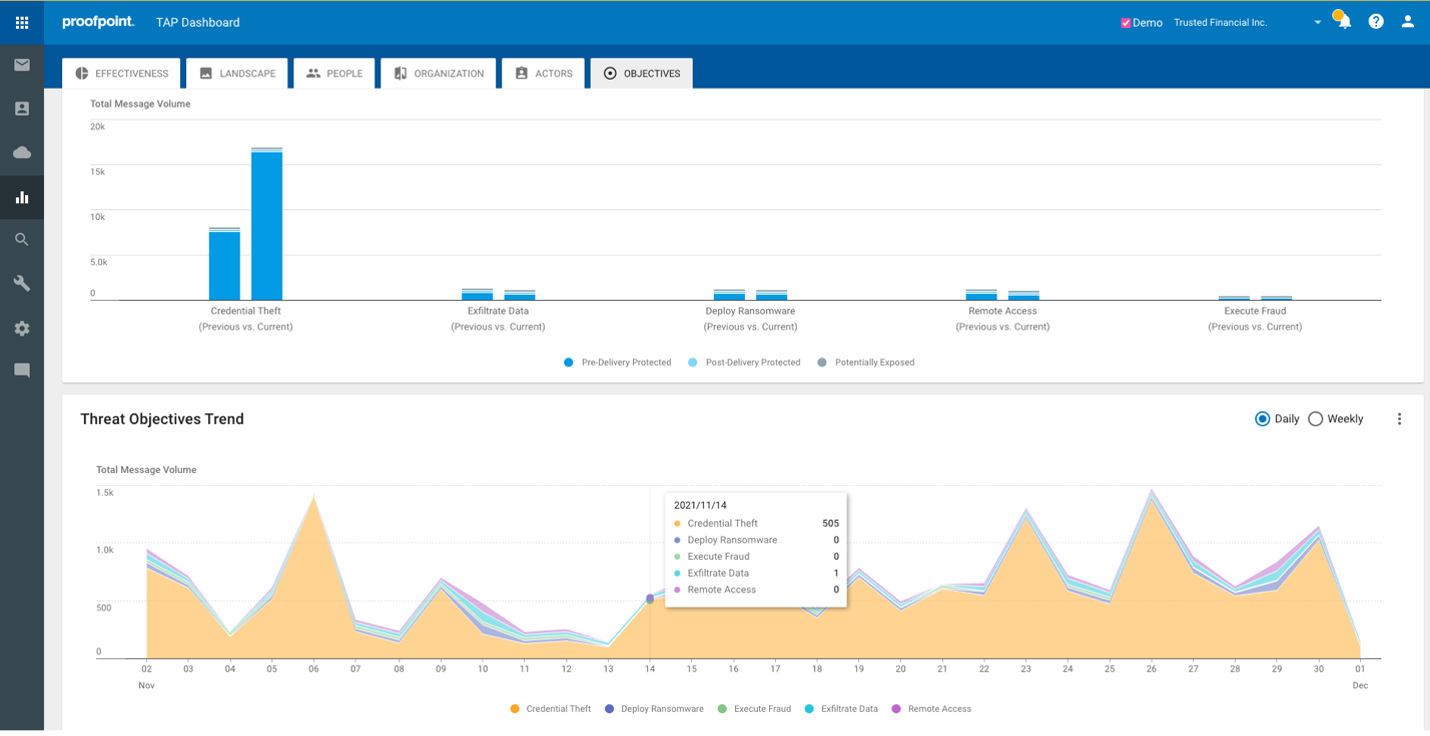
● Unmatched Visibility: Proofpoint provides unique, actionable visibility into the human attack surface, revealing VAPs and peer group comparisons to help organizations assess, prioritize, and mitigate risk. We offer detailed forensics including insight into threats, campaigns, and threat actors, enabling organizations to understand how they are targeted and how to prevent them. Our unique VAP insights also allow organizations to implement adaptive risk-based controls to mitigate the threat risky users pose. Recently, we introduced a new feature to automatically identify supplier risks, including malware, impostor and phishing threats. We also introduce threat objectives, providing insight of attacker’s intentions with different campaigns, including if malware could lead to ransomware. And a user timeline to understand the context of threats and actions of individuals.
● Improve Operational Effectiveness: Proofpoint delivers operational savings by providing an integrated solution that focuses on threats that matter and automates threat detection and remediation. We remove email threats that are weaponized post-delivery, as well as unwanted emails from compromised internal accounts automatically. We streamline abuse mailbox management, eliminating the manual, labor-intensive work associated with identifying whether user-reported emails are malicious, searching for all delivered emails and removing them from inboxes and providing users feedback.



