Photo Gallery

|

|
Salt Security API Protection Platform

Additional Info
| Company | Salt Security |
| Company size | 100 - 499 employees |
| Website | https://salt.security/ |
NOMINATION HIGHLIGHTS
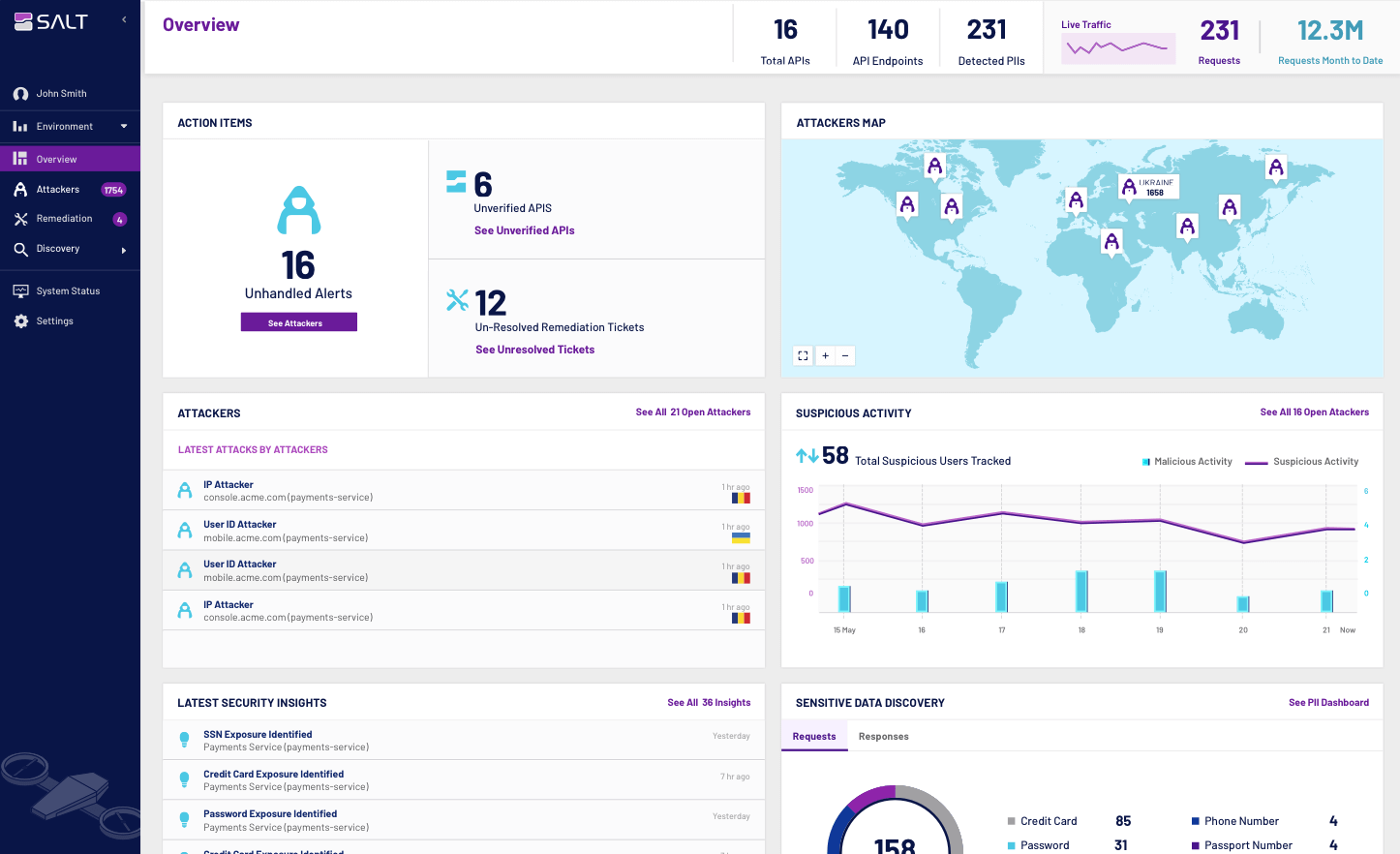
Salt Security has revolutionized API security by building a patented solution that leverages big data along with machine learning (ML) and artificial intelligence (AI) for API discovery, attack prevention, and remediating vulnerabilities. Its flagship offering, the Salt Security API Protection Platform, enables organizations to protect their APIs across build, deploy, and runtime phases. Through its unique API Context Engine (ACE) architecture, the Salt platform is able to discover all APIs and the sensitive data that they expose; identify API vulnerabilities in pre-prod testing; stop API attackers; prevent data exfiltration, account takeovers, and service disruption; and simplify compliance.
Conventional security tools such as Web Application Firewalls (WAFs) and management tools like API gateways cannot protect against today’s modern API attacks, because their proxy architecture validates API transactions one at a time and can detect only known attacks. They have no ability to correlate activity over time and therefore cannot identify the reconnaissance activities that bad actors must perform to learn the unique business logic of an API and propagate a successful API attack.
In contrast, Salt Security taps its big data engine to collect and-analyze the activity of millions of users in parallel, across millions of APIs. This architecture allows the Salt platform to piece together the subtle probing of an attacker during reconnaissance, assess the risk of all their activity, and pinpoint and stop them early in their process. In addition to using this data to stop attacks, Salt turns attackers into penetration-testers, leveraging their activity to provide valuable feedback to developers to eliminate API vulnerabilities. Salt builds a single attacker “fingerprint” made up of correlated insights that reduces the number of alerts, eliminating false positives and helping incident response teams to quickly assess situations. Customers can choose manual or automatic blocking of attackers, stopping them before they reach their objective.
How we are different
1. The Salt Security API Protection Platform has been in the market the longest, so its algorithms are the most advanced. The company also boasts the most customers, the fastest growth, the most application environments and ecosystem integrations supported, the most use cases enabled, and the most API traffic protected - setting the standard for API protection for security teams and the organizations they protect.
2. Unlike any other offering on the market, the Salt platform provides both runtime protection and developer insights, enabling companies to ensure that data and services are immediately protected while providing the remediation details developers need to harden APIs.
3. The Salt platform integrates easily, with no need for agents, code changes, configuration, or tuning.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

