SpyCloud
Photo Gallery
 |

 |
SpyCloud

Additional Info
| Company | SpyCloud |
| Website | https://spycloud.com/ |
| Company size (employees) | 100 to 499 |
| Type of solution | Cloud/SaaS |
Overview
No matter how strict an organization’s identity access management policies are, once credentials are compromised, criminals can use them to take control of personal and corporate accounts alike. Even with a high level of employee awareness and basic protections such as password complexity requirements and multifactor authentication, the sheer scope of today’s threats places a heavy burden on those who make up the first line of defense.
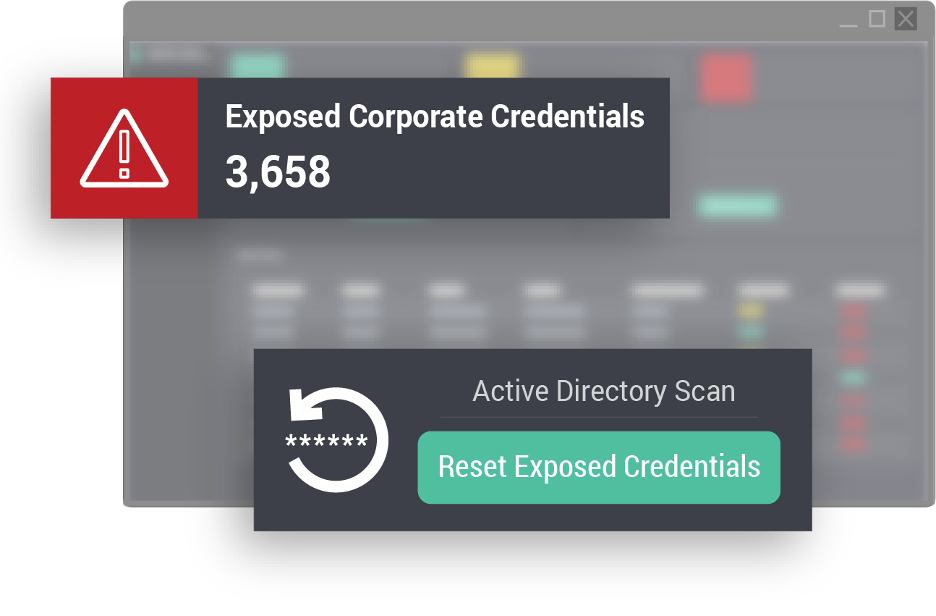
SpyCloud exponentially increases organizations’ vigilance by seamlessly checking credentials at the point of login against a recaptured breach database that is unmatched in both size and access to recently stolen credentials –– as early as days after exposure. If the password is tied to a data breach, further steps such as step-up authentication can corroborate that the user is genuine without introducing unnecessary friction, or the user can simply be forced to reset their password. SpyCloud is unique in that it can also run password-only checks and flag passwords that have ever been compromised in a data breach, regardless of whether they are tied to a given email address or username.
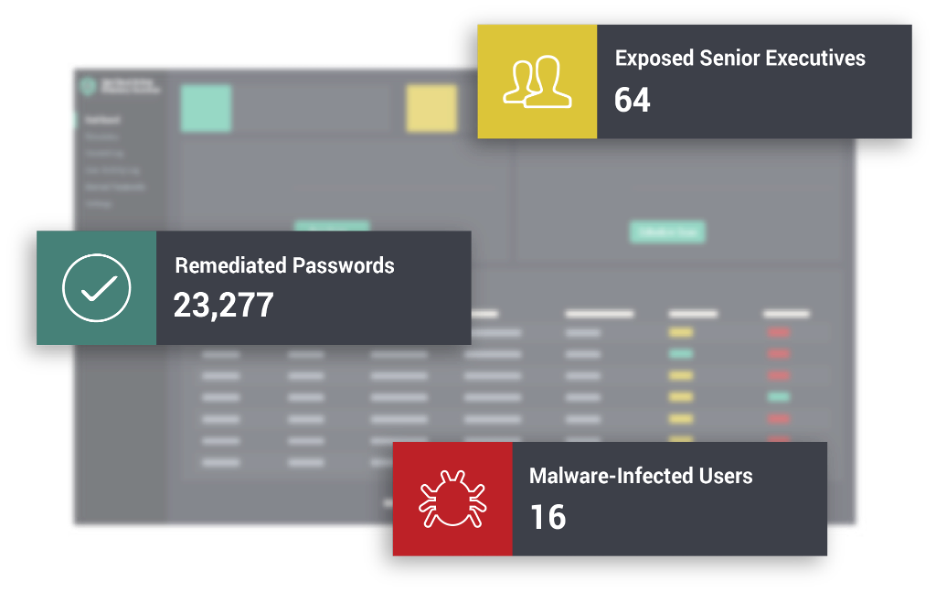
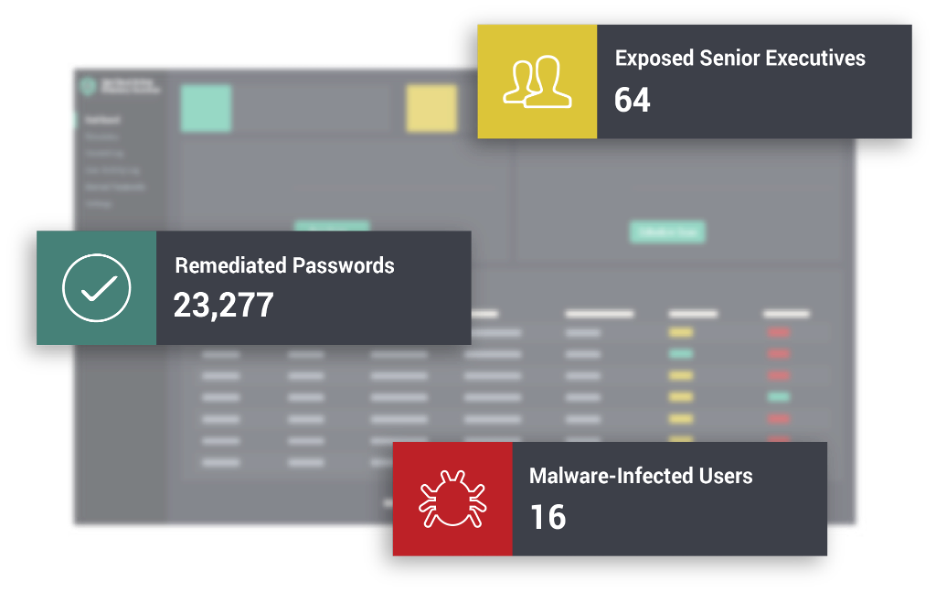
SpyCloud’s solution also fills a critical gap in enterprise IAM/CIAM programs: threat actors use social engineering and reused credentials to bypass traditional safeguards, often targeting executives and privileged users who are likely to have access to valuable, sensitive parts of the network. SpyCloud’s VIP Guardian solution enables businesses to extend password exposure alerts to the personal accounts of executives, board members and employees with privileged access, empowering them to secure compromised personal credentials that could provide entry points to corporate resources, while protecting their privacy. A compromised password used for online shopping or banking reused in a corporate setting could provide an entryway to corporate resources. SpyCloud VIP Guardian enables companies to reduce security blindspots.
How we are different
- Password-only checks: If a user’s password appears in the SpyCloud database, that password is available to cybercriminals. Whether your user has recycled their favorite credentials across multiple accounts or chosen a popular, easy-to-guess password, their account is at risk of account takeover. SpyCloud helps identify and prevent risky password choices by checking user passwords against its entire repository of stolen credentials, regardless of whether a specific user is compromised.
- Earliest possible data recovery: The strength of SpyCloud’s database sets it apart from other IAM solutions. By the time stolen data is “leaked” to the dark web, it may be as late as 18 months after the breach occurred. Companies may not yet be aware they have been breached, and therefore employees and consumers continue using compromised passwords, and the prevalence of password reuse means the longer the exposure window, the higher the risk to lucrative accounts. Through its extensive human intelligence capabilities, SpyCloud is able to recapture breached data within days of the breach occurring, enabling the fastest notification of exposed credentials available. This speed of collection (and therefore the speed with which logins can be checked for compromise) drastically decreases an enterprise’s threat exposure window.
- Multiple methods for interacting with SpyCloud data: Login checks and automatic remediation of compromised accounts are handled through integration with Microsoft Active Directory, and APIs enable rapid integration of SpyCloud data into other existing employee and consumer login workflows, SIEMs and Threat Intelligence Platforms.



