Photo Gallery

|


|
Sqrrl Enterprise


Additional Info
| Company | Sqrrl |
| Company size | 50 employees |
| Website | http://www.sqrrl.com |
NOMINATION HIGHLIGHTS
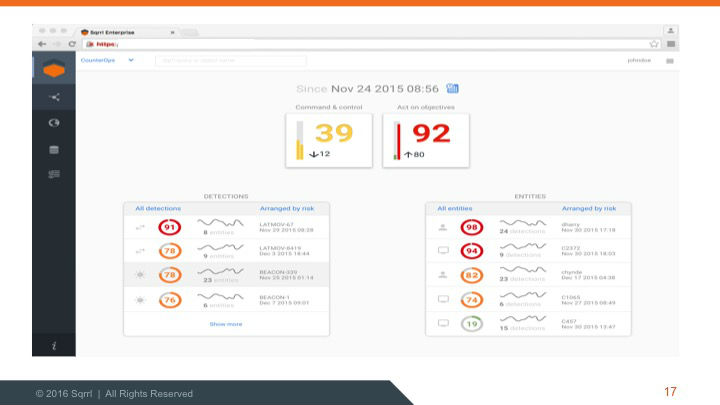
Sqrrl is the security analytics company that enables organizations to target, hunt, and disrupt advanced cyber threats. Sqrrl’s industry-leading threat detection and response threat hunting platform unites threat hunting, behavioral analytics, and incident analysis capabilities in an integrated solution. Unlike traditional signature- or rule-based detection solutions, Sqrrl’s platform detects the Tactics, Techniques, and Procedures (TTPs) of cyber adversaries and greatly reduces the time to investigate cyber incidents. Sqrrl utilizes linked data, machine learning, User and Entity Behavior Analytics (UEBA), risk scoring, and Big Data technologies to power a Behavior Graph that reveals malicious patterns and anomalies hidden within security datasets. Sqrrl leverages network, endpoint, and perimeter security datasets and integrates with various Security Information and Event Management (SIEM) tools.
How we are different
1. Scalability. There is no security solution on the market more scalable than Sqrrl. Sqrrl’s platform is built on a foundation of Apache Hadoop and Accumulo, and Sqrrl has successfully scaled these tools to tens of petabytes running mission critical applications in the U.S. Intelligence Community. Sqrrl combines this massive scalability with near real-time search across all data (i.e., there are no concepts of hot, warm, and cold data in Sqrrl unlike many log-based analysis systems.
2. Linked Data. Sqrrl is pioneering the usage of linked data and property graphs in the security analytics space. Sqrrl goes beyond simple log search and histograms, and provides linked data analysis and visualization capabilities. Linked data analysis and visualization involves the fusion of disparate data sources via defined ontologies enables better ad hoc interrogation of data, greater contextual awareness, faster search, and more intuitive visualization.
3. Advanced Analytics and Threat Hunting. As SC Magazine recently stated, "no company has brought the concept of threat hunting more to the fore than Sqrrl." Sqrrl's threat hunting capabilities are grounded in the concept of a Behavior Graph that combines linked data with various types of advanced algorithms, including machine learning, Bayesian statistics, and graph algorithms.

Community Choice Award
Vote for This Nominee
Share this page on any platform above to cast your vote. Each completed social post counts as one vote for this nomination.
Voting closes July 18, 2026 — winners announced ahead of Black Hat USA
What is the Community Choice Award? →
The Community Choice Award is a separate recognition decided entirely by public votes — not by the judging panel. Every nominee is eligible for both.

