Sumo Logic Cloud SOAR
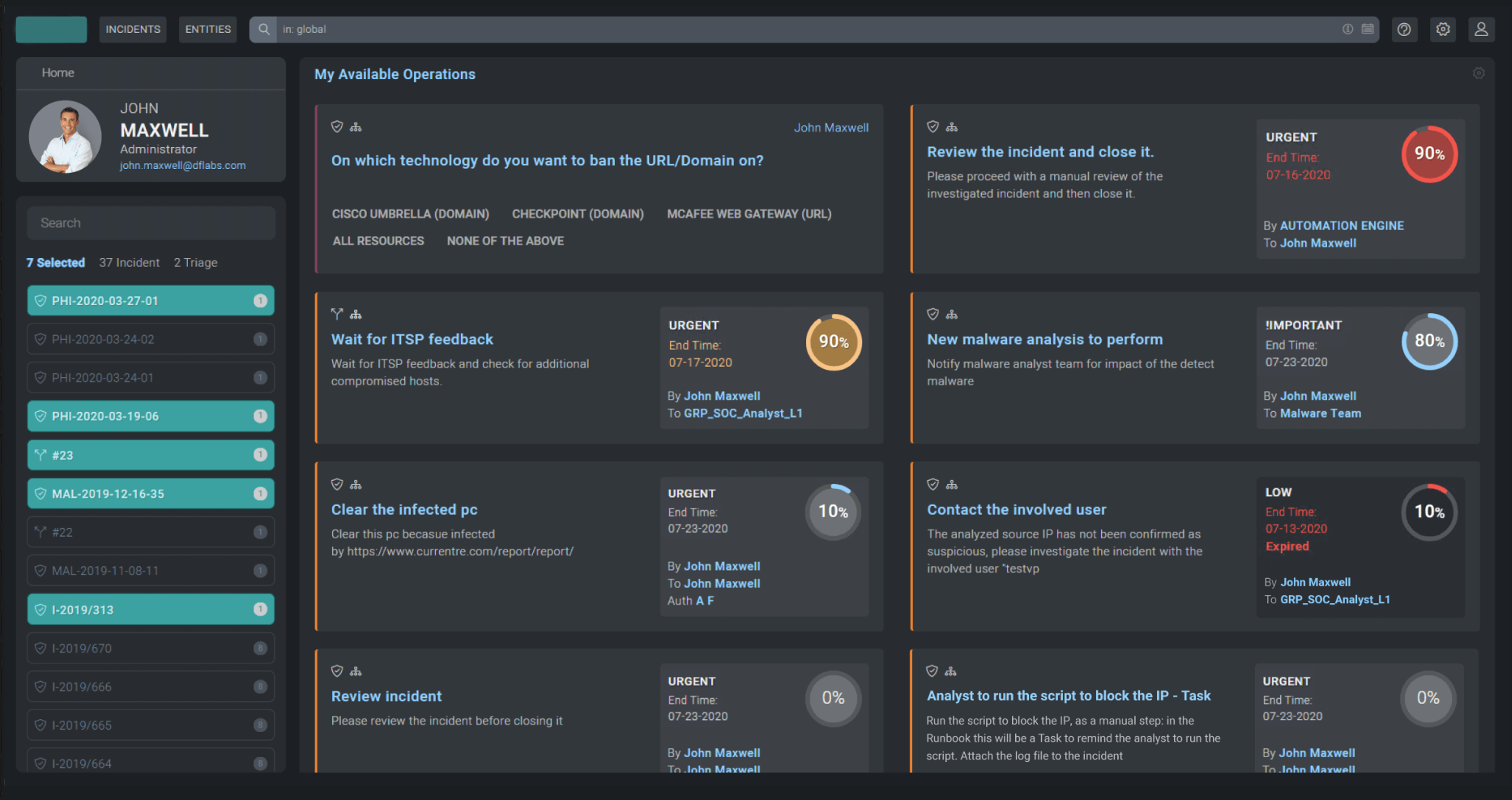
Photo Gallery
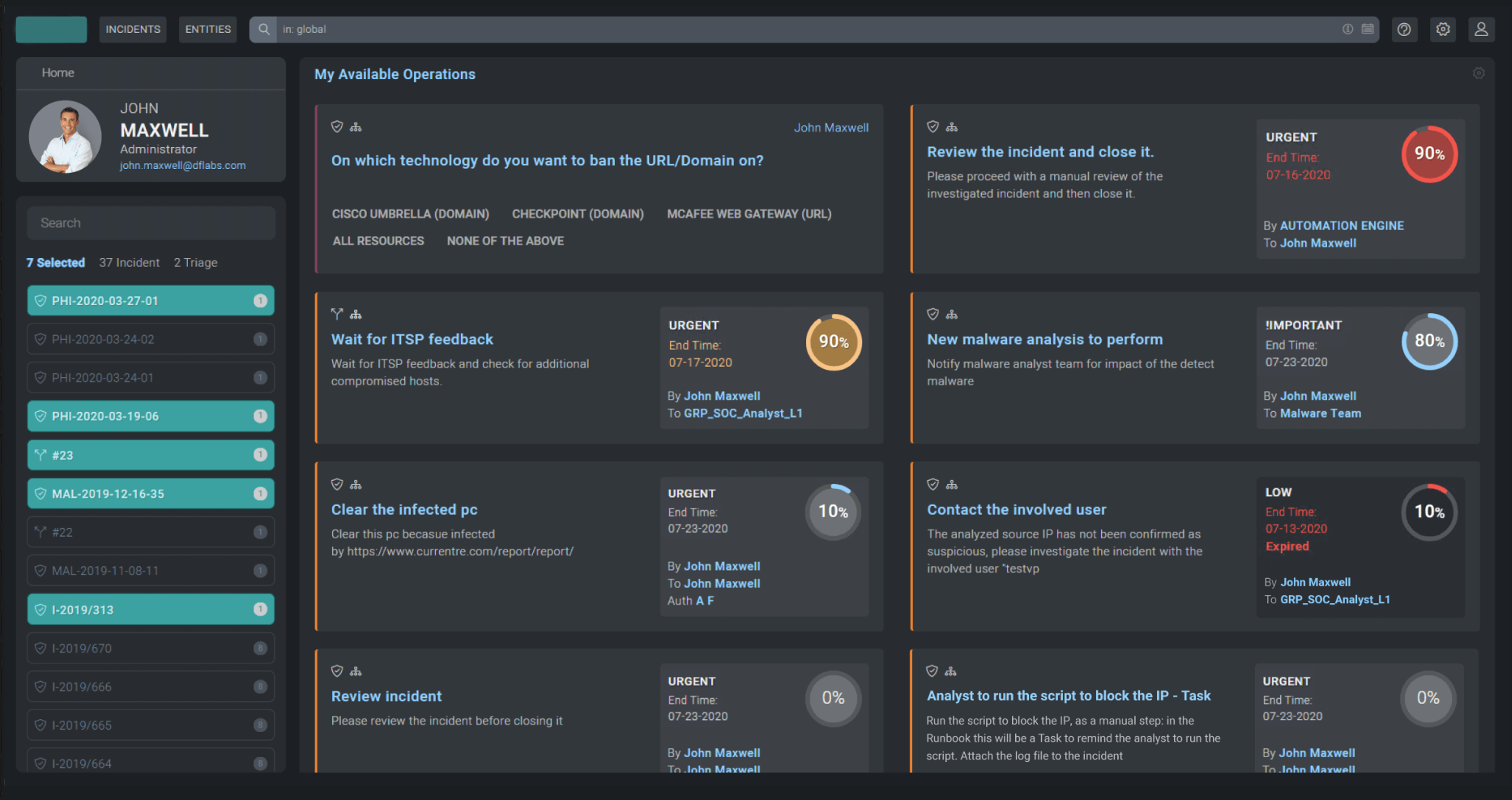 |
|
|
Sumo Logic Cloud SOAR
Additional Info
| Company | Sumo Logic |
| Website | https://www.sumologic.com/ |
| Company size (employees) | 500 to 999 |
| Type of solution | Cloud/SaaS |
Overview
Security Operations Centers (SOC) provide the foundation for enterprise cybersecurity efforts but are stymied by challenges. Sensors generate a deluge of alerts. Integrating, organizing and scoping those alerts into a security case is nearly impossible for a security analyst to process in a timely manner. These sensors, while needed, generate too many false positives, resulting in an impossible task of finding real threats.
The bottom line: traditional security operations are not sustainable.
With the acquisition of DFLabs in 2021, Sumo Logic bolstered its Security Intelligence portfolio with a leading SOAR platform that modernizes organizations’ SOC with improved productivity and increased visibility. The solution offers integrations with 200+ third-party IT and security tools using its existing Open Integration Framework, allowing teams to easily orchestrate across tools to fully automate incident response.
Sumo Logic analyzes 24.3 TB of data per second and an average of 2.10 quadrillion events per day for more than 2,100 customers, with approximately half leveraging its security intelligence solutions for their day-to-day security operations. This ability to scale and support more data for analysis demonstrates that Sumo Logic can easily manage, scale, and burst conditions for customers.
UC Davis uses Sumo Logic SOAR to accelerate threat response while improving the effectiveness of their SOC with progressive automation and orchestration across 30+ security tools. The UC Davis SOC team is able to handle 7+ million alerts that are generated from across 5,000 servers, and 170,000 users using automation, AI and analytics, ensuring an enhanced education experience for all students and faculty.
SOAR platforms are designed with one thing in mind – to triangulate data from different security tools to create a faster incident response. The success of a SOAR deployment depends on the sum of its parts – this is where Sumo Logic Cloud SOAR shines.
How we are different
- Sumo Logic security intelligence customers have access to the best in class cloud-native tools to investigate and respond to threats faster while improving SecOps productivity. A key differentiator between Sumo Logic and other SOAR vendors is its advanced triage capabilities — this allows customers to handle suspicious events that require deeper analysis outside the context of an incident, while helping to reduce the number of false positives and other red flags raised by an elevated number of suspicious events that have to be inspected. Sumo Logic Cloud SOAR builds on the company’s security offerings to include orchestration and automation to quickly address incidents with native integration Sumo Logic Cloud SIEM or other SIEMs as part of a comprehensive modern security solution.
- With Sumo Logic Cloud SOAR, enterprise SOC teams are able to minimize response times with flexible workflow automation across tools to improve standard operating procedures, and Supervised Active Intelligence (SAI) built on ML-based security intelligence suggests relevant processes for specific use cases. Cloud SOAR learns the characteristics of incoming alerts and uses that knowledge to enhance its incident response accuracy. Cloud SOAR remembers the decisions made when alerts are being categorized either as false positives or real threats, and by applying machine learning to historical response, it recommends relevant playbooks when incidents with similar characteristics occur. With improved overall collaboration, SOC teams can successfully pinpoint real threats and coordinate an effective response across tools and team members through native orchestration capabilities, ensuring efficient synergy during each phase of incident response.
- SOC teams can quickly assemble highly customizable reports, dashboards, and KPIs to easily navigate and assess their security intelligence portfolio. Users can easily manage the escalation process and empower analysts to work simultaneously on incidents by providing detailed incident reports with related IOCs, timeline and corrective actions.



