Photo Gallery
 |

 |
Vectra

Additional Info
| Website | http://www.vectra.ai |
| Company size (employees) | 100 to 499 |
| Headquarters Region | North America |
Overview
Vectra has changed the way an entire industry thinks about cybersecurity.
Cyberattacks – whether driven by financial gain, political and social disruption, state-sponsored espionage, or insider threats – are prompting cloud, data center and enterprise organizations to rethink how to best protect their business and critical data. With businesses facing devastating reputational and financial damage from data breaches, the stakes have never been higher.
Unfortunately, the status quo’s outdated approach to security – designed to prevent cyberattackers from getting inside networks – isn’t working. Traditional legacy security designed to keep out attackers are blind to these ever-changing threat behaviors, giving cybercriminals free rein to spy, spread and steal.
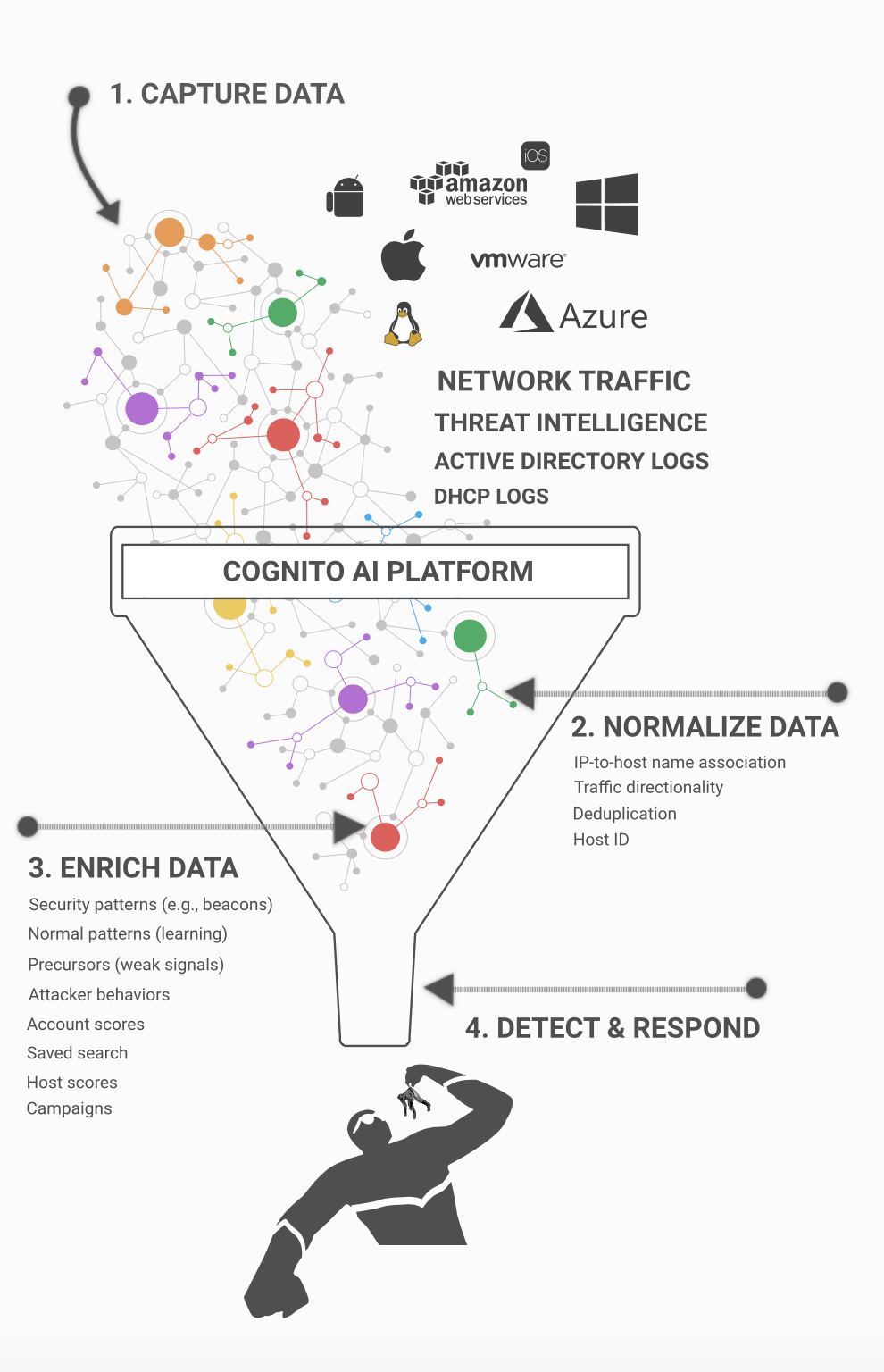
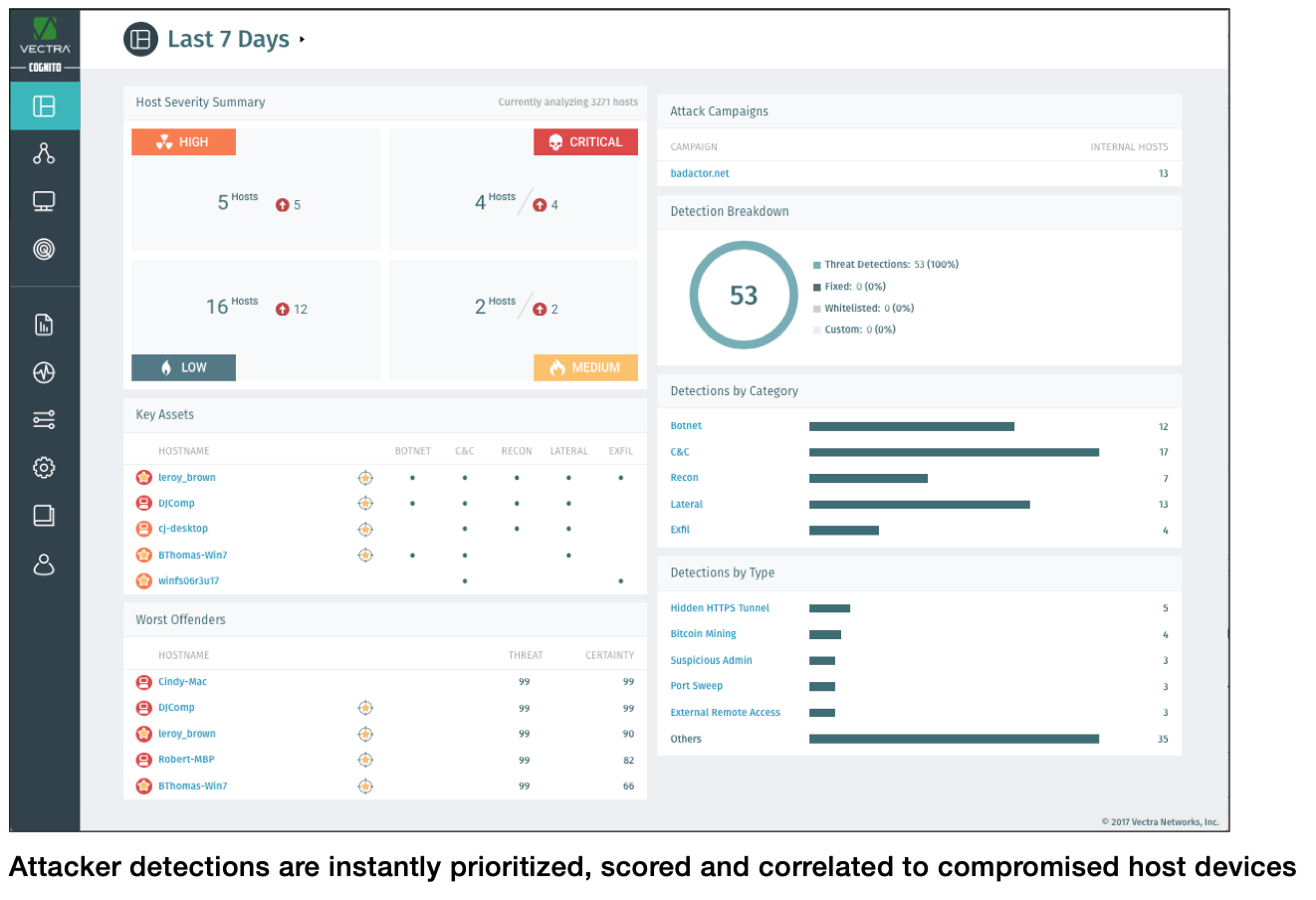
That’s why Vectra created the Cognito® platform. The Cognito platform is a reliable way to detect hidden attackers who get inside and respond instantly to stop in-progress threats from becoming a data breach. It empowers security teams to proactively hunt for evasive threats, augments organizations existing security investments, keeps up with the changing threat landscape, and offers exceptional scale across cloud, data center and enterprise infrastructures.
Cognito Detect™ AI software automates the detection of hidden cyberattacker behaviors and prioritizes the ones that posed the highest risk. Cognito Detect reduces the security operations workload by 34X and gives security professionals more time to focus on the all-important task of stopping data breaches.
Cognito Recall™ is a cloud-based investigative workbench that enables security professionals to proactively hunt for threats and perform conclusive attack investigations. Cognito Recall collects, analyzes and stores unlimited security-enriched metadata for forensic investigations and compliance mandates like GDPR.
Cognito Stream™, used by the biggest organizations in the world, feeds security-enriched metadata extracted from cloud, data center and enterprise networks to an organization’s data lake or SIEM. It correlates security-enriched metadata with other data sources and lets security researchers hunt retrospectively for threats.
How we are different
• Security teams use the Cognito platform to detect and respond to elusive cyberattackers. Vectra was first to apply AI to automatically detect and respond to cyberattackers across cloud, data center and enterprise networks, while enabling security teams to perform conclusive incident investigations and AI-assisted threat hunting.
Vectra prioritizes in-progress attacks that pose the highest business risk so security analysts know where to focus their attention first. Vectra also identifies the scope and precise locations of attacks so security teams can stop them from spreading.
Detecting attackers is incomplete without a quick response, and Vectra responds with deliberate speed. We work in real time with the entire ecosystem of cybersecurity investments to accelerate response time, stop the progression of attacks and avoid data breaches.
• Vectra is igniting a revolution in the fight against cyberthreats. Security researchers and data scientists in the Vectra Threat Labs™ take unexplained phenomena seen in customer networks and dig deeper to find the underlying reasons for the behavior.
Vectra researchers identify, investigate and report on a wide range of cyberattacks, security vulnerabilities and threat behaviors that are largely unknown to the world. With data sets from the research team, data scientists develop the intelligent machine learning algorithms and behavioral analysis behind our advanced AI.
Focusing on the underlying intentions of attackers and thinking about the possible methods they use to achieve them lead to threat-detection algorithms that are incredibly effective for extended periods of time. This ensures that the security posture of our customers is not a constant race against time.
• Vectra is an innovator. Vectra is the leader in network threat detection and response across cloud, data center and enterprise infrastructures. We hold 15 U.S. patents for AI that automate the hunt for cyberattacker behaviors, and 18 patent applications are pending.



