Photo Gallery
 |
 |
Datto

Additional Info
| Website | https://www.datto.com/ |
| Company size (employees) | 1,000 to 4,999 |
| Headquarters Region | North America |
Overview
Datto is the leading provider of enterprise-grade technology for small and medium-sized businesses (SMBs) delivered through the global community of local IT providers called Managed Service providers (MSPs). Datto’s proven Advanced Threat Protection, Unified Continuity, and Business Management solutions drive MSPs’ cyber resilience and efficient operations. Delivered via an integrated platform, Datto’s solutions help global MSP partners serve over 1 million businesses worldwide. From proactive, dynamic detection and prevention to fast, flexible recovery from cyber incidents, Datto offers a variety of solutions to defend against costly downtime and data loss in servers, virtual machines, cloud applications, or anywhere data resides.
Datto’s Business Continuity and Disaster Recovery (BCDR) solution was built for MSPs to prevent data loss and minimize downtime for their clients. Utilizing a cloud-first approach, MSPs can offer their clients an all-in-one solution that incorporates local backup and recovery. Additionally, Datto’s SaaS Protection offers comprehensive backup and recovery for critical cloud data in Microsoft 365 and Google Workspace. It is designed specifically for MSPs to protect their clients’ SaaS data and manage client data retention and cost. Furthermore, Datto’s SaaS Defense is a comprehensive, advanced threat protection solution for Microsoft 365 applications that is a fully integrated add-on solution to SaaS Protection.
Datto’s Remote Monitoring & Management (RMM) Ransomware Detection monitors for the existence of crypto-ransomware on endpoints using behavioral analysis of files, sending alerts when a device is infected. Once detected, Datto RMM attempts to stop the ransomware process and isolates the device to prevent the ransomware from spreading.
Additionally, Datto recently released a Log4j Shell RMM component for Datto partners and all MSPs that helps users leverage the power and reach of RMM, regardless of vendor, to enumerate systems that are both potentially vulnerable and that have been potentially attacked.
How we are different
Datto helps more than 1 million SMBs keep the lights on by providing protection from cyber threats and was founded on the idea that data backup required a new approach that assured reliable recovery from adverse events for SMBs. As the world’s leading provider of cloud-based software and security solutions purpose-built for delivery by MSPs, Datto’s proven Unified Continuity, Networking, and Business Management solutions drive cyber resilience, efficiency, and growth for MSPs. Through Datto’s solutions, digital assets can be protected wherever they live, preventing data loss and costly business downtime.
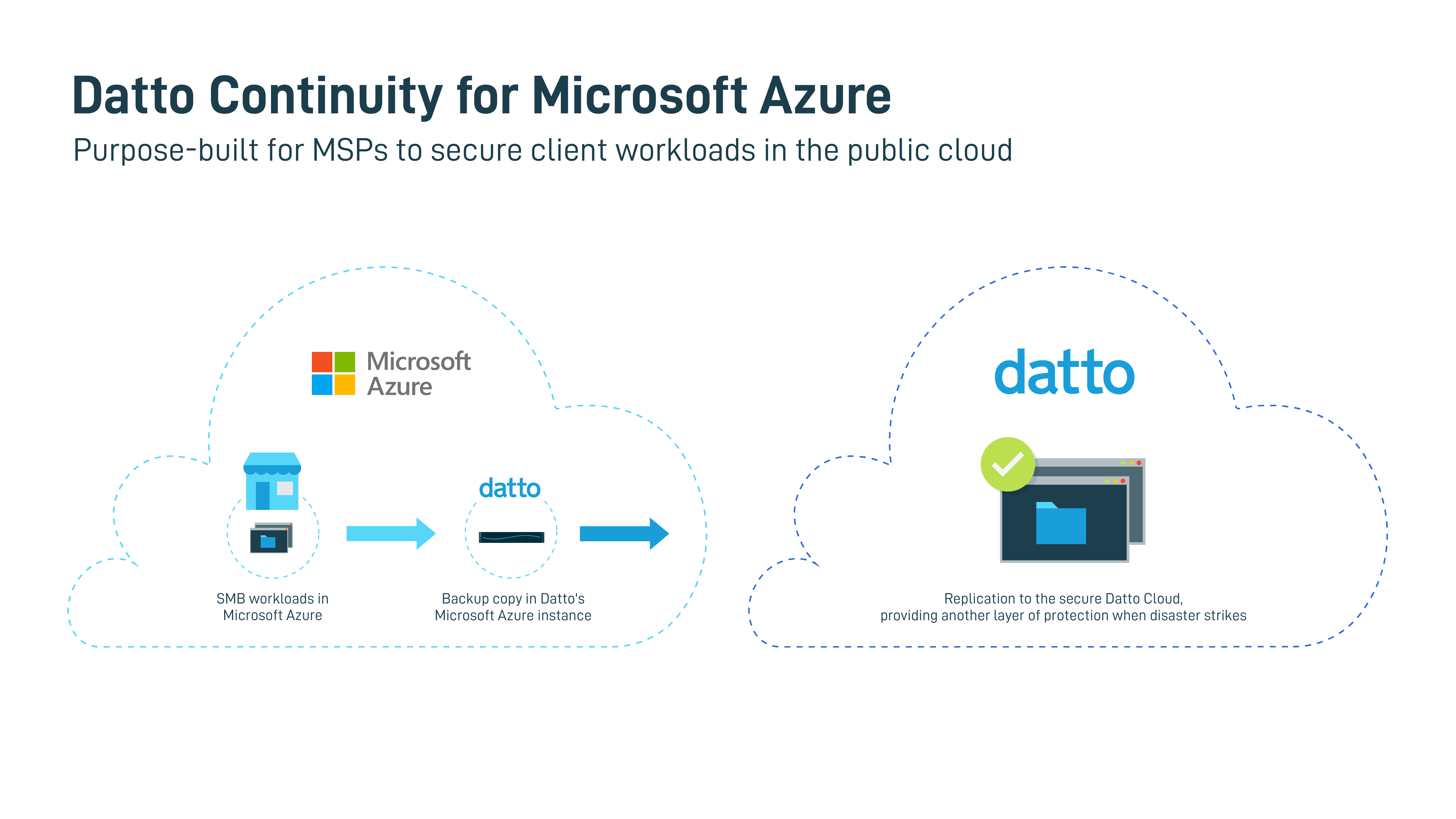
Datto is the first to provide MSP and SMBs specific protection in the cloud with Datto Continuity for Microsoft Azure product. In 2021, Datto stepped up to meet a large unmet need for MSPs--solving how to protect SMB data in the public cloud. While public clouds do protect their physical hosts, network and data centers, they do not protect user data, applications, endpoints, or insulate users and their data against cloud outages. Datto addressed this gap by building a customized solution from the ground up, engineered especially for MSPs to manage SMB client data in Microsoft Azure (the most used provider of MSPs). There is no other solution on the market that addresses this need that is tailored to the specific needs of MSPs and SMBs, as opposed to the needs of enterprise customers.
Datto is a security-first company and trusted MSP partner. The company continues to provide cyber resilience education to MSPs via live events, videos, podcasts, peer group engagement, and a variety of other mediums, forums and content types. Datto provides the larger MSP ecosystem with educational materials to help them analyze their own defenses, driving the creation of security controls in Datto products that help SMB end-users defend against common attack tactics.



