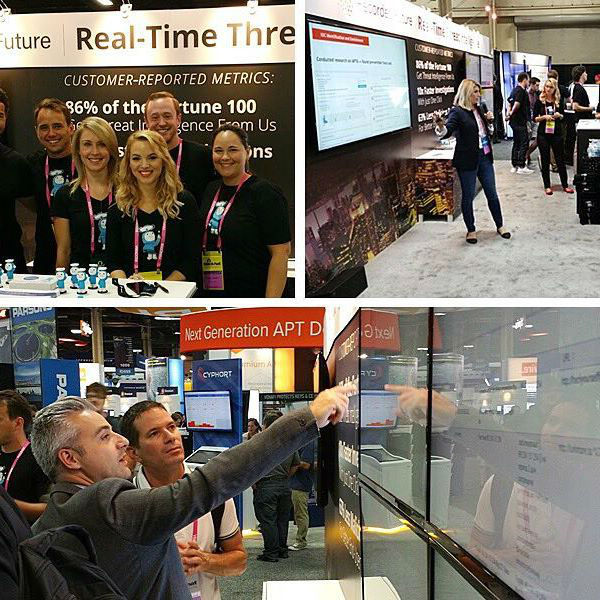
Recorded Future
Photo Gallery
 |

 |
Recorded Future


Additional Info
| Website | https://www.recordedfuture.com |
| Company size (employees) | 51-200 |
| Headquarters Region | North America |
Overview
In 2016, Recorded Future spearheaded the charge to empower every organization with relevant threat intelligence they can apply across their whole security infrastructure.
Our OMNI Intelligence Partner program was launched. Seeing security teams maximize their value from Recorded Future through all-source analysis that combines our unmatched breadth of intelligence with specialized threat content. Partnering with top security firms to give analysts a breakthrough in speed and confidence for this all-source analysis. Launch partners included Palo Alto Networks, Resilient, FireEye iSIGHT Intelligence, DomainTools, Farsight Security, PhishMe ReversingLabs, and Shodan. Security teams get on-demand integration of malware sandbox analysis, incident response investigations, and finished intelligence reporting, as well as domain, DNS, phishing, and internet of things (IoT) enrichment — all put in context with Recorded Future’s real-time threat intelligence.
We also made real-time, high context threat intelligence available to security operations teams through their SIEM. Our integrations let them correlate data in their SIEM with intelligence from Recorded Future. Our IP address risk list identifies thousands of indicators, and gives them dozens of context features to target the indicators that matter most for their security. It’s not just an IP list with risk scores; we continually update and age out indicators with patented algorithms that mine risk evidence from hundreds of thousands of sources including technical feeds, social media, security communities, dark web, paste sites and code repositories.
How we are different
Our customers are gaining measurable value from our real-time threat intelligence. Here are three metrics reported by our customers:
86% of the Fortune 100 uses Recorded Future
10x Productivity Gain From Real-Time Threat Intelligence for SIEMs
63% reduction in malicious traffic



